Cyber Crime Essay for Students and Children
500+ words essay on cyber crime.
Cyber Crime Essay – Everybody thinks that only stealing someone’s private data is Cyber Crime. But in defining terms we can say that ‘Cyber Crime refers to the use of an electronic device (computer, laptop, etc.) for stealing someone’s data or trying to harm them using a computer.
Besides, it is an illegal activity that involves a series of issues ranging from theft to using your system or IP address as a tool for committing a crime.


Types of Cyber Crime
Speaking in a broadway we can say that Cyber Crime are categorized into four major types. These are Financial, Privacy, Hacking, and Cyber Terrorism.
The financial crime they steal the money of user or account holders. Likewise, they also stole data of companies which can lead to financial crimes. Also, transactions are heavily risked because of them. Every year hackers stole lakhs and crores of rupees of businessmen and government.
Privacy crime includes stealing your private data which you do not want to share with the world. Moreover, due to it, the people suffer a lot and some even commit suicide because of their data’s misuse.
In, hacking they intentional deface a website to cause damage or loss to the public or owner. Apart from that, they destroy or make changes in the existing websites to diminish its value.
Modern-day terrorism has grown way beyond what it was 10-20 years ago. But cyber terrorism is not just related to terrorists or terrorist organizations. But to threat some person or property to the level of creating fear is also Cyber Terrorism.
Get the huge list of more than 500 Essay Topics and Ideas
Cyber Crime in India
Web world or cyberspace is a massive community of millions and billions of users and websites. Also, people access it for different uses like shopping, movies, music, video games, transactions, and e-commerce, etc.

In this Age of Technology and easy access to the internet, anyone can easily reach it. Because of this fast pace growth from the previous decade. Besides, the internet has opened a world of information on which anyone can connect.
Due to, this the rate of crime especially the rate of Cyber Crime has increased much fold. Moreover, the rate of circulation of data is also increased much fold due to the higher speed of internet. Above all, due to all these issues, the Cybersecurity has become a major concern for society.
Laws related to Cyber Crimes
To stop the spread of Cyber Crime and to safeguard the interest of people the government has made several laws related to Cyber Crimes. Also, these laws serve as protection against Cyber Crime. Apart from that, the government has also introduced cyber cells in police stations to counter the problem of Cyber Crime as fast as they can.
Ways of stopping Cyber Crime
Cyber Crime is not something which we cannot deal with our self. Likewise, with little use of our common sense and logic, we can stop Cyber Crimes from happening.
To conclude, we can say that Cyber Crime is a dangerous offense to someone’s privacy or any material. Also, we can avoid Cyber Crime by following some basic logical things and using our common sense. Above all, Cyber Crime is a violation of not only law but of human rights too.
{ “@context”: “https://schema.org”, “@type”: “FAQPage”, “mainEntity”: [{ “@type”: “Question”, “name”: “What is the main cause of Cyber Crime?”, “acceptedAnswer”: { “@type”: “Answer”, “text”: “The greed for quick money and the desire to get famous quickly are the two main reasons of Cyber Crime. Also, most of the targets of Cyber Crime banks, businessman, financial firms, etc.” } }, { “@type”: “Question”, “name”: “What is the punishment of Cyber Crime in India?”, “acceptedAnswer”: { “@type”: “Answer”, “text”:”If the person is found guilty then there are several punishments based on the level of crime. A simple crime can cost you a fine while a bigger crime can lead you to jail.”} }] }
Customize your course in 30 seconds
Which class are you in.

- Travelling Essay
- Picnic Essay
- Our Country Essay
- My Parents Essay
- Essay on Favourite Personality
- Essay on Memorable Day of My Life
- Essay on Knowledge is Power
- Essay on Gurpurab
- Essay on My Favourite Season
- Essay on Types of Sports
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Download the App
- CBSE Class 10th
- CBSE Class 12th
- UP Board 10th
- UP Board 12th
- Bihar Board 10th
- Bihar Board 12th
- Top Schools in India
- Top Schools in Delhi
- Top Schools in Mumbai
- Top Schools in Chennai
- Top Schools in Hyderabad
- Top Schools in Kolkata
- Top Schools in Pune
- Top Schools in Bangalore
Products & Resources
- JEE Main Knockout April
- Free Sample Papers
- Free Ebooks
- NCERT Notes
- NCERT Syllabus
- NCERT Books
- RD Sharma Solutions
- Navodaya Vidyalaya Admission 2024-25
- NCERT Solutions
- NCERT Solutions for Class 12
- NCERT Solutions for Class 11
- NCERT solutions for Class 10
- NCERT solutions for Class 9
- NCERT solutions for Class 8
- NCERT Solutions for Class 7
- JEE Main 2024
- JEE Advanced 2024
- BITSAT 2024
- View All Engineering Exams
- Colleges Accepting B.Tech Applications
- Top Engineering Colleges in India
- Engineering Colleges in India
- Engineering Colleges in Tamil Nadu
- Engineering Colleges Accepting JEE Main
- Top IITs in India
- Top NITs in India
- Top IIITs in India
- JEE Main College Predictor
- JEE Main Rank Predictor
- MHT CET College Predictor
- AP EAMCET College Predictor
- GATE College Predictor
- KCET College Predictor
- JEE Advanced College Predictor
- View All College Predictors
- JEE Main Question Paper
- JEE Main Mock Test
- JEE Main Registration
- JEE Main Syllabus
- Download E-Books and Sample Papers
- Compare Colleges
- B.Tech College Applications
- GATE 2024 Result
- MAH MBA CET Exam
- View All Management Exams
Colleges & Courses
- MBA College Admissions
- MBA Colleges in India
- Top IIMs Colleges in India
- Top Online MBA Colleges in India
- MBA Colleges Accepting XAT Score
- BBA Colleges in India
- XAT College Predictor 2024
- SNAP College Predictor
- NMAT College Predictor
- MAT College Predictor 2024
- CMAT College Predictor 2024
- CAT Percentile Predictor 2023
- CAT 2023 College Predictor
- CMAT 2024 Registration
- TS ICET 2024 Registration
- CMAT Exam Date 2024
- MAH MBA CET Cutoff 2024
- Download Helpful Ebooks
- List of Popular Branches
- QnA - Get answers to your doubts
- IIM Fees Structure
- AIIMS Nursing
- Top Medical Colleges in India
- Top Medical Colleges in India accepting NEET Score
- Medical Colleges accepting NEET
- List of Medical Colleges in India
- List of AIIMS Colleges In India
- Medical Colleges in Maharashtra
- Medical Colleges in India Accepting NEET PG
- NEET College Predictor
- NEET PG College Predictor
- NEET MDS College Predictor
- DNB CET College Predictor
- DNB PDCET College Predictor
- NEET Application Form 2024
- NEET PG Application Form 2024
- NEET Cut off
- NEET Online Preparation
- Download Helpful E-books
- LSAT India 2024
- Colleges Accepting Admissions
- Top Law Colleges in India
- Law College Accepting CLAT Score
- List of Law Colleges in India
- Top Law Colleges in Delhi
- Top Law Collages in Indore
- Top Law Colleges in Chandigarh
- Top Law Collages in Lucknow
Predictors & E-Books
- CLAT College Predictor
- MHCET Law ( 5 Year L.L.B) College Predictor
- AILET College Predictor
- Sample Papers
- Compare Law Collages
- Careers360 Youtube Channel
- CLAT Syllabus 2025
- CLAT Previous Year Question Paper
- AIBE 18 Result 2023
- NID DAT Exam
- Pearl Academy Exam
Animation Courses
- Animation Courses in India
- Animation Courses in Bangalore
- Animation Courses in Mumbai
- Animation Courses in Pune
- Animation Courses in Chennai
- Animation Courses in Hyderabad
- Design Colleges in India
- Fashion Design Colleges in Bangalore
- Fashion Design Colleges in Mumbai
- Fashion Design Colleges in Pune
- Fashion Design Colleges in Delhi
- Fashion Design Colleges in Hyderabad
- Fashion Design Colleges in India
- Top Design Colleges in India
- Free Design E-books
- List of Branches
- Careers360 Youtube channel
- NIFT College Predictor
- UCEED College Predictor
- NID DAT College Predictor
- IPU CET BJMC
- JMI Mass Communication Entrance Exam
- IIMC Entrance Exam
- Media & Journalism colleges in Delhi
- Media & Journalism colleges in Bangalore
- Media & Journalism colleges in Mumbai
- List of Media & Journalism Colleges in India
- CA Intermediate
- CA Foundation
- CS Executive
- CS Professional
- Difference between CA and CS
- Difference between CA and CMA
- CA Full form
- CMA Full form
- CS Full form
- CA Salary In India
Top Courses & Careers
- Bachelor of Commerce (B.Com)
- Master of Commerce (M.Com)
- Company Secretary
- Cost Accountant
- Charted Accountant
- Credit Manager
- Financial Advisor
- Top Commerce Colleges in India
- Top Government Commerce Colleges in India
- Top Private Commerce Colleges in India
- Top M.Com Colleges in Mumbai
- Top B.Com Colleges in India
- IT Colleges in Tamil Nadu
- IT Colleges in Uttar Pradesh
- MCA Colleges in India
- BCA Colleges in India
Quick Links
- Information Technology Courses
- Programming Courses
- Web Development Courses
- Data Analytics Courses
- Big Data Analytics Courses
- RUHS Pharmacy Admission Test
- Top Pharmacy Colleges in India
- Pharmacy Colleges in Pune
- Pharmacy Colleges in Mumbai
- Colleges Accepting GPAT Score
- Pharmacy Colleges in Lucknow
- List of Pharmacy Colleges in Nagpur
- GPAT Result
- GPAT 2024 Admit Card
- GPAT Question Papers
- NCHMCT JEE 2024
- Mah BHMCT CET
- Top Hotel Management Colleges in Delhi
- Top Hotel Management Colleges in Hyderabad
- Top Hotel Management Colleges in Mumbai
- Top Hotel Management Colleges in Tamil Nadu
- Top Hotel Management Colleges in Maharashtra
- B.Sc Hotel Management
- Hotel Management
- Diploma in Hotel Management and Catering Technology
Diploma Colleges
- Top Diploma Colleges in Maharashtra
- UPSC IAS 2024
- SSC CGL 2024
- IBPS RRB 2024
- Previous Year Sample Papers
- Free Competition E-books
- Sarkari Result
- QnA- Get your doubts answered
- UPSC Previous Year Sample Papers
- CTET Previous Year Sample Papers
- SBI Clerk Previous Year Sample Papers
- NDA Previous Year Sample Papers
Upcoming Events
- NDA Application Form 2024
- UPSC IAS Application Form 2024
- CDS Application Form 2024
- CTET Admit card 2024
- HP TET Result 2023
- SSC GD Constable Admit Card 2024
- UPTET Notification 2024
- SBI Clerk Result 2024
Other Exams
- SSC CHSL 2024
- UP PCS 2024
- UGC NET 2024
- RRB NTPC 2024
- IBPS PO 2024
- IBPS Clerk 2024
- IBPS SO 2024
- Top University in USA
- Top University in Canada
- Top University in Ireland
- Top Universities in UK
- Top Universities in Australia
- Best MBA Colleges in Abroad
- Business Management Studies Colleges
Top Countries
- Study in USA
- Study in UK
- Study in Canada
- Study in Australia
- Study in Ireland
- Study in Germany
- Study in China
- Study in Europe
Student Visas
- Student Visa Canada
- Student Visa UK
- Student Visa USA
- Student Visa Australia
- Student Visa Germany
- Student Visa New Zealand
- Student Visa Ireland
- CUET PG 2024
- IGNOU B.Ed Admission 2024
- DU Admission
- UP B.Ed JEE 2024
- DDU Entrance Exam
- IIT JAM 2024
- IGNOU Online Admission 2024
- Universities in India
- Top Universities in India 2024
- Top Colleges in India
- Top Universities in Uttar Pradesh 2024
- Top Universities in Bihar
- Top Universities in Madhya Pradesh 2024
- Top Universities in Tamil Nadu 2024
- Central Universities in India
- CUET PG Admit Card 2024
- IGNOU Date Sheet
- CUET Mock Test 2024
- CUET Application Form 2024
- CUET PG Syllabus 2024
- CUET Participating Universities 2024
- CUET Previous Year Question Paper
- CUET Syllabus 2024 for Science Students
- E-Books and Sample Papers
- CUET Exam Pattern 2024
- CUET Exam Date 2024
- CUET Syllabus 2024
- IGNOU Exam Form 2024
- IGNOU Result
- CUET PG Courses 2024
Engineering Preparation
- Knockout JEE Main 2024
- Test Series JEE Main 2024
- JEE Main 2024 Rank Booster
Medical Preparation
- Knockout NEET 2024
- Test Series NEET 2024
- Rank Booster NEET 2024
Online Courses
- JEE Main One Month Course
- NEET One Month Course
- IBSAT Free Mock Tests
- IIT JEE Foundation Course
- Knockout BITSAT 2024
- Career Guidance Tool
Top Streams
- IT & Software Certification Courses
- Engineering and Architecture Certification Courses
- Programming And Development Certification Courses
- Business and Management Certification Courses
- Marketing Certification Courses
- Health and Fitness Certification Courses
- Design Certification Courses
Specializations
- Digital Marketing Certification Courses
- Cyber Security Certification Courses
- Artificial Intelligence Certification Courses
- Business Analytics Certification Courses
- Data Science Certification Courses
- Cloud Computing Certification Courses
- Machine Learning Certification Courses
- View All Certification Courses
- UG Degree Courses
- PG Degree Courses
- Short Term Courses
- Free Courses
- Online Degrees and Diplomas
- Compare Courses
Top Providers
- Coursera Courses
- Udemy Courses
- Edx Courses
- Swayam Courses
- upGrad Courses
- Simplilearn Courses
- Great Learning Courses
Access premium articles, webinars, resources to make the best decisions for career, course, exams, scholarships, study abroad and much more with
Plan, Prepare & Make the Best Career Choices
Cyber Crime Essay
The unlawful act of gaining unauthorised access to computer systems or digital devices is known as cybercrime. A detailed grasp of how to stop or recover from cyberattacks is provided by cyber security. Online courses offer guidance on how to avoid, safeguard against, and recover from cybercrime risks. Here are a few sample essays on the topic ‘Cyber Crime’.
100 Words Essay on Cyber Crime
200 words essay on cyber crime, 500 words essay on cyber crime.

Cybercrime is the most discussed problem in the twenty-first century. The usage of cellphones and the internet is increasing dramatically over the world, which is generating questions about consumers' security and privacy. Because of this, it is crucial for all users to understand cybercrime and security. Cybercrime is defined as organised criminal conduct carried out by attackers online. Cybercrime comes in numerous forms, such as fraud, computer viruses, cyberstalking, and others. Due to these, businesses and government organisations are spending more on maintaining and employing professionals in cybercrime.
There are millions and billions of users and websites in the vast community known as cyberspace. People utilise it for a variety of activities including e-commerce, transactions, shopping, movies, music, and video games. Anyone can simply access anything online in the current technological era owing to accessible internet connection. As a result, crime in general and cybercrime in particular have surged dramatically. Additionally, the faster internet connection has greatly boosted the rate of data circulation. All of these problems are responsible as to why cyber security has grown to be a significant issue for society.
The government has created a number of cybercrime-related laws in an effort to curb the spread of the crime and to protect people's interests. These laws also provide defence against cybercrime. Aside from that, the government has established cyber cells in police stations to combat cybercrime as quickly as possible.
Cybercrime is an attack that can be harmful to both an individual and a business. There have been several instances where a cyber attack led to a data leak that caused a significant loss for a business or a person. These cyber-attacks could have negative effects on the country and the business. The countless instances of cyberattacks that have taken place in India and other nations have necessitated increased security measures. There are four main categories of cybercrime, according to a popular definition—hacking, money, privacy, and cyber terrorism.
Cybercrime is a type of crime in which illegal activities are carried out online or using computers. Cybercrime comes in a variety of forms which involves harassing online users. Cybercrime is the most serious and rapidly expanding type of crime in this day and age. Any person's life may be negatively impacted for a very long time by becoming a cyber victim. Cybercrimes have a wide range of repercussions on financial and investment activity in digital organisations.
One typical tactic used by criminals is to lure online users in by creating attractive websites and sending phoney emails purporting to be from banks or other organisations and asking for personal information. It makes it easier for criminals to access a person's bank account and personal data. Due to viruses, mail fraud, account hacking, and software piracy, people have been victims of cybercrimes. They also run into problems with unauthorised access mailing, threats from pornographic emails, and video transmission.
Types of Cyber Crime
Cyberstalking | It is the use of electronic communication to track down a person or to make repeated attempts to get in touch with them in order to foster personal interaction despite their blatant lack of interest. Anyone who monitors the internet, email, or any other form of electronic communication is guilty of stalking.
Phishing | It is a sort of fraud that includes collecting personal data from recipients of emails that seem to be coming from a reliable source, including Customer ID, IPIN, Credit/Debit Card number, Card expiration date, CVV number, etc.
Vishing | It is an attempt when criminals attempt to obtain personal information over the phone, such as Customer ID, Net Banking password, ATM PIN, OTP, Card expiration date, CVV, etc.
Smishing | It is a sort of fraud that employs text messages sent to mobile devices to entice victims into dialling a fake phone number, going to a fake website, or downloading harmful software.
Impersonation And Identity Theft | This includes the dishonest or fraudulent use of another person's electronic signature, password, or other distinctive identification trait.
Virus, Worms, Trojan | A computer virus is a programme designed to infiltrate your computer, corrupt your files and data, and spread itself. Worms are malicious software applications that repeatedly duplicate themselves on local drives, network shares, etc. Trojan is a malicious programme that mimics a legitimate application. Trojans offer unauthorised people and applications access to your computer through a backdoor entry, allowing them to steal sensitive data.
How to Prevent Cyber Crime
Backup every piece of information—data, systems, and considerations—to make it easier for businesses to recover from unforeseen events with the help of prior data.
Pick a firewall that offers protection from viruses, malware, and dishonest hackers.
Never divulge private information to a stranger since they might exploit it for fraud.
To avoid cybercrime, check your security settings—in order to determine if someone has logged into your computer, a cyber firewall analyses your network settings.
Antivirus software aids in identifying potential threats and malware before they infect a computer system. Never use software that has been cracked since it poses a serious risk of data loss or malware attack.
Keep your information protected when accessing untrusted websites—information can readily bypass the data through phishing websites.
Explore Career Options (By Industry)
- Construction
- Entertainment
- Manufacturing
- Information Technology
Bio Medical Engineer
The field of biomedical engineering opens up a universe of expert chances. An Individual in the biomedical engineering career path work in the field of engineering as well as medicine, in order to find out solutions to common problems of the two fields. The biomedical engineering job opportunities are to collaborate with doctors and researchers to develop medical systems, equipment, or devices that can solve clinical problems. Here we will be discussing jobs after biomedical engineering, how to get a job in biomedical engineering, biomedical engineering scope, and salary.
Data Administrator
Database professionals use software to store and organise data such as financial information, and customer shipping records. Individuals who opt for a career as data administrators ensure that data is available for users and secured from unauthorised sales. DB administrators may work in various types of industries. It may involve computer systems design, service firms, insurance companies, banks and hospitals.
Ethical Hacker
A career as ethical hacker involves various challenges and provides lucrative opportunities in the digital era where every giant business and startup owns its cyberspace on the world wide web. Individuals in the ethical hacker career path try to find the vulnerabilities in the cyber system to get its authority. If he or she succeeds in it then he or she gets its illegal authority. Individuals in the ethical hacker career path then steal information or delete the file that could affect the business, functioning, or services of the organization.
Data Analyst
The invention of the database has given fresh breath to the people involved in the data analytics career path. Analysis refers to splitting up a whole into its individual components for individual analysis. Data analysis is a method through which raw data are processed and transformed into information that would be beneficial for user strategic thinking.
Data are collected and examined to respond to questions, evaluate hypotheses or contradict theories. It is a tool for analyzing, transforming, modeling, and arranging data with useful knowledge, to assist in decision-making and methods, encompassing various strategies, and is used in different fields of business, research, and social science.
Geothermal Engineer
Individuals who opt for a career as geothermal engineers are the professionals involved in the processing of geothermal energy. The responsibilities of geothermal engineers may vary depending on the workplace location. Those who work in fields design facilities to process and distribute geothermal energy. They oversee the functioning of machinery used in the field.
Remote Sensing Technician
Individuals who opt for a career as a remote sensing technician possess unique personalities. Remote sensing analysts seem to be rational human beings, they are strong, independent, persistent, sincere, realistic and resourceful. Some of them are analytical as well, which means they are intelligent, introspective and inquisitive.
Remote sensing scientists use remote sensing technology to support scientists in fields such as community planning, flight planning or the management of natural resources. Analysing data collected from aircraft, satellites or ground-based platforms using statistical analysis software, image analysis software or Geographic Information Systems (GIS) is a significant part of their work. Do you want to learn how to become remote sensing technician? There's no need to be concerned; we've devised a simple remote sensing technician career path for you. Scroll through the pages and read.
Geotechnical engineer
The role of geotechnical engineer starts with reviewing the projects needed to define the required material properties. The work responsibilities are followed by a site investigation of rock, soil, fault distribution and bedrock properties on and below an area of interest. The investigation is aimed to improve the ground engineering design and determine their engineering properties that include how they will interact with, on or in a proposed construction.
The role of geotechnical engineer in mining includes designing and determining the type of foundations, earthworks, and or pavement subgrades required for the intended man-made structures to be made. Geotechnical engineering jobs are involved in earthen and concrete dam construction projects, working under a range of normal and extreme loading conditions.
Cartographer
How fascinating it is to represent the whole world on just a piece of paper or a sphere. With the help of maps, we are able to represent the real world on a much smaller scale. Individuals who opt for a career as a cartographer are those who make maps. But, cartography is not just limited to maps, it is about a mixture of art , science , and technology. As a cartographer, not only you will create maps but use various geodetic surveys and remote sensing systems to measure, analyse, and create different maps for political, cultural or educational purposes.
Budget Analyst
Budget analysis, in a nutshell, entails thoroughly analyzing the details of a financial budget. The budget analysis aims to better understand and manage revenue. Budget analysts assist in the achievement of financial targets, the preservation of profitability, and the pursuit of long-term growth for a business. Budget analysts generally have a bachelor's degree in accounting, finance, economics, or a closely related field. Knowledge of Financial Management is of prime importance in this career.
Product Manager
A Product Manager is a professional responsible for product planning and marketing. He or she manages the product throughout the Product Life Cycle, gathering and prioritising the product. A product manager job description includes defining the product vision and working closely with team members of other departments to deliver winning products.
Underwriter
An underwriter is a person who assesses and evaluates the risk of insurance in his or her field like mortgage, loan, health policy, investment, and so on and so forth. The underwriter career path does involve risks as analysing the risks means finding out if there is a way for the insurance underwriter jobs to recover the money from its clients. If the risk turns out to be too much for the company then in the future it is an underwriter who will be held accountable for it. Therefore, one must carry out his or her job with a lot of attention and diligence.
Finance Executive
Operations manager.
Individuals in the operations manager jobs are responsible for ensuring the efficiency of each department to acquire its optimal goal. They plan the use of resources and distribution of materials. The operations manager's job description includes managing budgets, negotiating contracts, and performing administrative tasks.
Bank Probationary Officer (PO)
Investment director.
An investment director is a person who helps corporations and individuals manage their finances. They can help them develop a strategy to achieve their goals, including paying off debts and investing in the future. In addition, he or she can help individuals make informed decisions.
Welding Engineer
Welding Engineer Job Description: A Welding Engineer work involves managing welding projects and supervising welding teams. He or she is responsible for reviewing welding procedures, processes and documentation. A career as Welding Engineer involves conducting failure analyses and causes on welding issues.
Transportation Planner
A career as Transportation Planner requires technical application of science and technology in engineering, particularly the concepts, equipment and technologies involved in the production of products and services. In fields like land use, infrastructure review, ecological standards and street design, he or she considers issues of health, environment and performance. A Transportation Planner assigns resources for implementing and designing programmes. He or she is responsible for assessing needs, preparing plans and forecasts and compliance with regulations.
An expert in plumbing is aware of building regulations and safety standards and works to make sure these standards are upheld. Testing pipes for leakage using air pressure and other gauges, and also the ability to construct new pipe systems by cutting, fitting, measuring and threading pipes are some of the other more involved aspects of plumbing. Individuals in the plumber career path are self-employed or work for a small business employing less than ten people, though some might find working for larger entities or the government more desirable.
Construction Manager
Individuals who opt for a career as construction managers have a senior-level management role offered in construction firms. Responsibilities in the construction management career path are assigning tasks to workers, inspecting their work, and coordinating with other professionals including architects, subcontractors, and building services engineers.
Urban Planner
Urban Planning careers revolve around the idea of developing a plan to use the land optimally, without affecting the environment. Urban planning jobs are offered to those candidates who are skilled in making the right use of land to distribute the growing population, to create various communities.
Urban planning careers come with the opportunity to make changes to the existing cities and towns. They identify various community needs and make short and long-term plans accordingly.
Highway Engineer
Highway Engineer Job Description: A Highway Engineer is a civil engineer who specialises in planning and building thousands of miles of roads that support connectivity and allow transportation across the country. He or she ensures that traffic management schemes are effectively planned concerning economic sustainability and successful implementation.
Environmental Engineer
Individuals who opt for a career as an environmental engineer are construction professionals who utilise the skills and knowledge of biology, soil science, chemistry and the concept of engineering to design and develop projects that serve as solutions to various environmental problems.
Naval Architect
A Naval Architect is a professional who designs, produces and repairs safe and sea-worthy surfaces or underwater structures. A Naval Architect stays involved in creating and designing ships, ferries, submarines and yachts with implementation of various principles such as gravity, ideal hull form, buoyancy and stability.
Orthotist and Prosthetist
Orthotists and Prosthetists are professionals who provide aid to patients with disabilities. They fix them to artificial limbs (prosthetics) and help them to regain stability. There are times when people lose their limbs in an accident. In some other occasions, they are born without a limb or orthopaedic impairment. Orthotists and prosthetists play a crucial role in their lives with fixing them to assistive devices and provide mobility.
Veterinary Doctor
Pathologist.
A career in pathology in India is filled with several responsibilities as it is a medical branch and affects human lives. The demand for pathologists has been increasing over the past few years as people are getting more aware of different diseases. Not only that, but an increase in population and lifestyle changes have also contributed to the increase in a pathologist’s demand. The pathology careers provide an extremely huge number of opportunities and if you want to be a part of the medical field you can consider being a pathologist. If you want to know more about a career in pathology in India then continue reading this article.
Speech Therapist
Gynaecologist.
Gynaecology can be defined as the study of the female body. The job outlook for gynaecology is excellent since there is evergreen demand for one because of their responsibility of dealing with not only women’s health but also fertility and pregnancy issues. Although most women prefer to have a women obstetrician gynaecologist as their doctor, men also explore a career as a gynaecologist and there are ample amounts of male doctors in the field who are gynaecologists and aid women during delivery and childbirth.
An oncologist is a specialised doctor responsible for providing medical care to patients diagnosed with cancer. He or she uses several therapies to control the cancer and its effect on the human body such as chemotherapy, immunotherapy, radiation therapy and biopsy. An oncologist designs a treatment plan based on a pathology report after diagnosing the type of cancer and where it is spreading inside the body.
Audiologist
The audiologist career involves audiology professionals who are responsible to treat hearing loss and proactively preventing the relevant damage. Individuals who opt for a career as an audiologist use various testing strategies with the aim to determine if someone has a normal sensitivity to sounds or not. After the identification of hearing loss, a hearing doctor is required to determine which sections of the hearing are affected, to what extent they are affected, and where the wound causing the hearing loss is found. As soon as the hearing loss is identified, the patients are provided with recommendations for interventions and rehabilitation such as hearing aids, cochlear implants, and appropriate medical referrals. While audiology is a branch of science that studies and researches hearing, balance, and related disorders.
Hospital Administrator
The hospital Administrator is in charge of organising and supervising the daily operations of medical services and facilities. This organising includes managing of organisation’s staff and its members in service, budgets, service reports, departmental reporting and taking reminders of patient care and services.
For an individual who opts for a career as an actor, the primary responsibility is to completely speak to the character he or she is playing and to persuade the crowd that the character is genuine by connecting with them and bringing them into the story. This applies to significant roles and littler parts, as all roles join to make an effective creation. Here in this article, we will discuss how to become an actor in India, actor exams, actor salary in India, and actor jobs.
Individuals who opt for a career as acrobats create and direct original routines for themselves, in addition to developing interpretations of existing routines. The work of circus acrobats can be seen in a variety of performance settings, including circus, reality shows, sports events like the Olympics, movies and commercials. Individuals who opt for a career as acrobats must be prepared to face rejections and intermittent periods of work. The creativity of acrobats may extend to other aspects of the performance. For example, acrobats in the circus may work with gym trainers, celebrities or collaborate with other professionals to enhance such performance elements as costume and or maybe at the teaching end of the career.
Video Game Designer
Career as a video game designer is filled with excitement as well as responsibilities. A video game designer is someone who is involved in the process of creating a game from day one. He or she is responsible for fulfilling duties like designing the character of the game, the several levels involved, plot, art and similar other elements. Individuals who opt for a career as a video game designer may also write the codes for the game using different programming languages.
Depending on the video game designer job description and experience they may also have to lead a team and do the early testing of the game in order to suggest changes and find loopholes.
Radio Jockey
Radio Jockey is an exciting, promising career and a great challenge for music lovers. If you are really interested in a career as radio jockey, then it is very important for an RJ to have an automatic, fun, and friendly personality. If you want to get a job done in this field, a strong command of the language and a good voice are always good things. Apart from this, in order to be a good radio jockey, you will also listen to good radio jockeys so that you can understand their style and later make your own by practicing.
A career as radio jockey has a lot to offer to deserving candidates. If you want to know more about a career as radio jockey, and how to become a radio jockey then continue reading the article.
Choreographer
The word “choreography" actually comes from Greek words that mean “dance writing." Individuals who opt for a career as a choreographer create and direct original dances, in addition to developing interpretations of existing dances. A Choreographer dances and utilises his or her creativity in other aspects of dance performance. For example, he or she may work with the music director to select music or collaborate with other famous choreographers to enhance such performance elements as lighting, costume and set design.
Videographer
Multimedia specialist.
A multimedia specialist is a media professional who creates, audio, videos, graphic image files, computer animations for multimedia applications. He or she is responsible for planning, producing, and maintaining websites and applications.
Social Media Manager
A career as social media manager involves implementing the company’s or brand’s marketing plan across all social media channels. Social media managers help in building or improving a brand’s or a company’s website traffic, build brand awareness, create and implement marketing and brand strategy. Social media managers are key to important social communication as well.
Copy Writer
In a career as a copywriter, one has to consult with the client and understand the brief well. A career as a copywriter has a lot to offer to deserving candidates. Several new mediums of advertising are opening therefore making it a lucrative career choice. Students can pursue various copywriter courses such as Journalism , Advertising , Marketing Management . Here, we have discussed how to become a freelance copywriter, copywriter career path, how to become a copywriter in India, and copywriting career outlook.
Careers in journalism are filled with excitement as well as responsibilities. One cannot afford to miss out on the details. As it is the small details that provide insights into a story. Depending on those insights a journalist goes about writing a news article. A journalism career can be stressful at times but if you are someone who is passionate about it then it is the right choice for you. If you want to know more about the media field and journalist career then continue reading this article.
For publishing books, newspapers, magazines and digital material, editorial and commercial strategies are set by publishers. Individuals in publishing career paths make choices about the markets their businesses will reach and the type of content that their audience will be served. Individuals in book publisher careers collaborate with editorial staff, designers, authors, and freelance contributors who develop and manage the creation of content.
In a career as a vlogger, one generally works for himself or herself. However, once an individual has gained viewership there are several brands and companies that approach them for paid collaboration. It is one of those fields where an individual can earn well while following his or her passion.
Ever since internet costs got reduced the viewership for these types of content has increased on a large scale. Therefore, a career as a vlogger has a lot to offer. If you want to know more about the Vlogger eligibility, roles and responsibilities then continue reading the article.
Individuals in the editor career path is an unsung hero of the news industry who polishes the language of the news stories provided by stringers, reporters, copywriters and content writers and also news agencies. Individuals who opt for a career as an editor make it more persuasive, concise and clear for readers. In this article, we will discuss the details of the editor's career path such as how to become an editor in India, editor salary in India and editor skills and qualities.
Linguistic meaning is related to language or Linguistics which is the study of languages. A career as a linguistic meaning, a profession that is based on the scientific study of language, and it's a very broad field with many specialities. Famous linguists work in academia, researching and teaching different areas of language, such as phonetics (sounds), syntax (word order) and semantics (meaning).
Other researchers focus on specialities like computational linguistics, which seeks to better match human and computer language capacities, or applied linguistics, which is concerned with improving language education. Still, others work as language experts for the government, advertising companies, dictionary publishers and various other private enterprises. Some might work from home as freelance linguists. Philologist, phonologist, and dialectician are some of Linguist synonym. Linguists can study French , German , Italian .
Public Relation Executive
Travel journalist.
The career of a travel journalist is full of passion, excitement and responsibility. Journalism as a career could be challenging at times, but if you're someone who has been genuinely enthusiastic about all this, then it is the best decision for you. Travel journalism jobs are all about insightful, artfully written, informative narratives designed to cover the travel industry. Travel Journalist is someone who explores, gathers and presents information as a news article.
Quality Controller
A quality controller plays a crucial role in an organisation. He or she is responsible for performing quality checks on manufactured products. He or she identifies the defects in a product and rejects the product.
A quality controller records detailed information about products with defects and sends it to the supervisor or plant manager to take necessary actions to improve the production process.
Production Manager
Merchandiser.
A QA Lead is in charge of the QA Team. The role of QA Lead comes with the responsibility of assessing services and products in order to determine that he or she meets the quality standards. He or she develops, implements and manages test plans.
Metallurgical Engineer
A metallurgical engineer is a professional who studies and produces materials that bring power to our world. He or she extracts metals from ores and rocks and transforms them into alloys, high-purity metals and other materials used in developing infrastructure, transportation and healthcare equipment.
Azure Administrator
An Azure Administrator is a professional responsible for implementing, monitoring, and maintaining Azure Solutions. He or she manages cloud infrastructure service instances and various cloud servers as well as sets up public and private cloud systems.
AWS Solution Architect
An AWS Solution Architect is someone who specializes in developing and implementing cloud computing systems. He or she has a good understanding of the various aspects of cloud computing and can confidently deploy and manage their systems. He or she troubleshoots the issues and evaluates the risk from the third party.
Computer Programmer
Careers in computer programming primarily refer to the systematic act of writing code and moreover include wider computer science areas. The word 'programmer' or 'coder' has entered into practice with the growing number of newly self-taught tech enthusiasts. Computer programming careers involve the use of designs created by software developers and engineers and transforming them into commands that can be implemented by computers. These commands result in regular usage of social media sites, word-processing applications and browsers.
ITSM Manager
Information security manager.
Individuals in the information security manager career path involves in overseeing and controlling all aspects of computer security. The IT security manager job description includes planning and carrying out security measures to protect the business data and information from corruption, theft, unauthorised access, and deliberate attack
Business Intelligence Developer
Applications for admissions are open..

JEE Main Important Chemistry formulas
As per latest 2024 syllabus. Chemistry formulas, equations, & laws of class 11 & 12th chapters

Aakash iACST Scholarship Test 2024
Get up to 90% scholarship on NEET, JEE & Foundation courses

Resonance Coaching
Enroll in Resonance Coaching for success in JEE/NEET exams

ALLEN JEE Exam Prep
Start your JEE preparation with ALLEN

NEET 2024 Most scoring concepts
Just Study 32% of the NEET syllabus and Score upto 100% marks

JEE Main high scoring chapters and topics
As per latest 2024 syllabus. Study 40% syllabus and score upto 100% marks in JEE
Everything about Education
Latest updates, Exclusive Content, Webinars and more.
Download Careers360 App's
Regular exam updates, QnA, Predictors, College Applications & E-books now on your Mobile
Cetifications
We Appeared in

Presentations made painless
- Get Premium
117 CyberCrime Essay Topic Ideas & Examples
Inside This Article
117 Cybercrime Essay Topic Ideas & Examples
In today's digitally interconnected world, cybercrime has become a significant concern for individuals, businesses, and governments alike. The ever-evolving nature of cyber threats poses challenges to law enforcement agencies and cybersecurity professionals. If you are tasked with writing an essay on cybercrime, but struggling to come up with a topic, fret not! Here, we present 117 cybercrime essay topic ideas and examples to help inspire your writing.
- The rise of ransomware attacks: Causes, consequences, and preventive measures.
- Cyberbullying: Analyzing its psychological impact on victims and strategies for prevention.
- Social engineering attacks: Understanding the methods and mitigating the risks.
- The role of international cooperation in combating cybercrime.
- The dark web: A haven for illegal activities.
- Cyber warfare: Assessing the implications and international norms.
- Online identity theft: Examining the financial and emotional consequences.
- The use of artificial intelligence in cybercrime prevention.
- Cyber espionage: Analyzing state-sponsored attacks and their impact on national security.
- The role of cryptocurrencies in facilitating cybercrime.
- Cyberstalking: Legal challenges and protective measures.
- The impact of cybercrime on small businesses.
- The ethics of hacking: White hat versus black hat.
- Cyberterrorism: Assessing the risks and counterterrorism strategies.
- The role of legislation in combating cybercrime.
- The psychological profile of cybercriminals: Identifying common characteristics.
- The influence of cybercrime on financial markets and economies.
- Cyber fraud: Analyzing different types and methods.
- The impact of cybercrime on critical infrastructure.
- Cybersecurity awareness: Strategies for educating individuals and organizations.
- The role of social media in facilitating cybercrime.
- Cyberbullying among teenagers: Causes, consequences, and preventive measures.
- The future of cybersecurity: Anticipating emerging threats.
- The impact of cybercrime on healthcare organizations.
- The role of machine learning in detecting and preventing cyber threats.
- Cyberattacks on the electoral process: Safeguarding democratic systems.
- The legal challenges of prosecuting cybercriminals.
- The role of international organizations in addressing cybercrime.
- Cyber insurance: Analyzing its effectiveness in mitigating financial losses.
- The impact of cybercrime on intellectual property theft.
- The vulnerabilities of IoT devices: Securing the interconnected world.
- The role of education in raising cybercrime awareness.
- The impact of cybercrime on national security.
- The role of cloud computing in enhancing cybersecurity.
- Cyberbullying in the workplace: Addressing its prevalence and impact.
- The psychology behind cybercriminals: Understanding their motivations.
- The impact of cybercrime on e-commerce and online transactions.
- Cybersecurity regulations: Balancing privacy and protection.
- The influence of state-sponsored hacking on international relations.
- The role of cybersecurity certifications in professional development.
- Cyberattacks on critical infrastructure: Analyzing vulnerabilities and protective measures.
- The impact of cybercrime on human rights and privacy.
- Cyber espionage: The blurred lines between nation-states and cybercriminals.
- The role of artificial intelligence in cyber defense.
- The psychology of phishing attacks: How do they manipulate human behavior?
- The impact of cybercrime on the banking sector.
- The role of information sharing in combating cyber threats.
- The rise of cybercrime during the COVID-19 pandemic.
- The legal challenges of extraditing cybercriminals across borders.
- The impact of cybercrime on children and adolescents.
- The role of cybersecurity in protecting personal data.
- Cyberattacks on the transportation industry: Analyzing risks and vulnerabilities.
- The impact of cybercrime on trust in digital systems.
- Cyber insurance: Its role in incentivizing cybersecurity investments.
- The ethical considerations of hacking for a cause: Hacktivism.
- The impact of cybercrime on national economies.
- Cybersecurity in the age of artificial intelligence: Challenges and opportunities.
- The role of open-source intelligence in investigating cybercrimes.
- Cyberattacks on critical infrastructure: Learning from historical incidents.
- The impact of cybercrime on the reputation of organizations.
- The psychology of online scams: Understanding victims' susceptibility.
- The vulnerabilities of smart cities: Securing the urban future.
- The impact of cybercrime on human trafficking and exploitation.
- The role of cybersecurity in protecting intellectual property.
- Cyber espionage: Analyzing the tactics and techniques of nation-state actors.
- The impact of cybercrime on the tourism industry.
- The role of cybersecurity in protecting elections and democratic processes.
- Cybersecurity in the era of quantum computing: Preparing for the future.
- The impact of cybercrime on the entertainment industry.
- The psychology of online radicalization: Analyzing the role of the internet.
- The vulnerabilities of supply chain networks: Safeguarding global trade.
- The impact of cybercrime on national healthcare systems.
- The role of cybersecurity in protecting critical research and development.
- Cyber insurance: Challenges and opportunities for insurance providers.
- The dark side of social media: Cyberbullying and harassment.
- The impact of cybercrime on the aviation industry.
- The role of cybersecurity in protecting autonomous vehicles.
- Cyber espionage: Analyzing the economic and political motivations behind attacks.
- The impact of cybercrime on the gaming industry.
- The vulnerabilities of smart home devices: Protecting personal privacy.
- The role of cybersecurity in protecting intellectual property in the pharmaceutical industry.
- Cyberattacks on the energy sector: Analyzing the risks and protective measures.
- The impact of cybercrime on the media and journalism.
- The psychology of online grooming: Protecting vulnerable individuals.
- The vulnerabilities of e-voting systems: Safeguarding democratic processes.
- The impact of cybercrime on the retail industry.
- The role of cybersecurity in protecting autonomous drones.
- Cyber espionage: Analyzing the impact on technological advancements.
- The impact of cybercrime on the music industry.
- The vulnerabilities of smart grid systems: Securing the future of energy.
- The role of cybersecurity in protecting intellectual property in the film industry.
- Cyberattacks on the water supply: Analyzing the risks and protective measures.
- The impact of cybercrime on the sports industry.
- The psychology of online addiction: Analyzing the impact on mental health.
- The vulnerabilities of smart transportation systems: Ensuring passenger safety.
- The impact of cybercrime on the fashion industry.
- The role of cybersecurity in protecting smart city infrastructure.
- Cyber espionage: Analyzing the impact on scientific advancements.
- The impact of cybercrime on the food and beverage industry.
- The vulnerabilities of wearable technology: Protecting personal health data.
- The role of cybersecurity in protecting intellectual property in the automotive industry.
- Cyberattacks on the telecommunications sector: Analyzing the risks and protective measures.
- The impact of cybercrime on the art and design industry.
- The psychology of online gaming addiction: Analyzing its effects on players.
- The vulnerabilities of smart healthcare systems: Protecting patient data.
- The impact of cybercrime on the hospitality industry.
- The role of cybersecurity in protecting smart home infrastructure.
- Cyber espionage: Analyzing the impact on military capabilities.
- The impact of cybercrime on the beauty and cosmetics industry.
- The vulnerabilities of augmented reality technology: Protecting user privacy.
- The role of cybersecurity in protecting intellectual property in the aerospace industry.
- Cyberattacks on the financial sector: Analyzing the risks and protective measures.
- The impact of cybercrime on the real estate industry.
- The psychology of online shopping addiction: Analyzing consumer behavior.
- The vulnerabilities of blockchain technology: Ensuring secure transactions.
- The impact of cybercrime on the agricultural industry.
- The role of cybersecurity in protecting smart grid infrastructure.
These 117 cybercrime essay topic ideas and examples should provide ample inspiration for your writing. Whether you choose to focus on the psychological aspects, the technical challenges, or the societal impacts of cybercrime, remember to approach the topic with a critical mindset and back your arguments with reliable sources. Good luck with your essay!
Want to create a presentation now?
Instantly Create A Deck
Let PitchGrade do this for me
Hassle Free
We will create your text and designs for you. Sit back and relax while we do the work.
Explore More Content
- Privacy Policy
- Terms of Service
© 2023 Pitchgrade
105 Cybercrime Essay Topics
🏆 best essay topics on cybercrime, ✍️ cybercrime essay topics for college, 🎓 most interesting cybercrime research titles, 💡 simple cybercrime essay ideas, ❓ cybercrime research questions.
- The Hacking of Yahoo in 2013 and 2014
- Significance of Computer Forensics to Law Enforcement
- Cybercrime and Its Impact on Society
- Cyber Security: The Nature and Scope of Cybercrime
- Ethics of Hacking and Cracking
- Computer Forensics Laboratory’ Legal Requirements
- Cybercrime From the Religious Viewpoint
- Digital Forensic Examination of Counterfeit Documents A citizen has contacted the police regarding the selling of counterfeit public documents. The investigator contacted the computer forensic laboratory to examine the evidence.
- The Cybercrime Effect on Public Administration Cybercrime incidents occur in almost all government and public sectors and in the daily lives of individuals; such moments violate stability and the usual way of life.
- Cyber Crime : Issues and Threats Cyber crime involves the stealing or manipulation of information effectively distorting its values across global networks.
- St. Louis County’s Cybercrime Task Force Plan The current paper presents a plan for the development of a cybercrime task force for St. Louis County to assign priorities for the task force.
- Cybercrime and the Culture of Fear Sexual exploitation and other offenses against children remain tragic—in spite of their frequency—and those numbers have been diminishing since the advent of the internet.
- Trends in Cybercrime and Society The internet has played a pivotal role in boosting science, business, and education. Nevertheless, the internet is an additional tool for committing many crimes.
- Cybercrime Legislation in the UAE, US and India The paper will narrow down to present similarities and differences between the cybercrime laws in UAE and the United States, and between the cybercrime laws in the UAE and India.
- The Phone Hacking Scandal Among the major news event in the recent few days was the phone hacking scandal that was linked to the News of the World; a tabloid newspaper in the United Kingdom (UK).
- Network Security and Cyber Crime, Super-Highway Metaphor Some of the major practices that can be done in ensuring maximum data security and integrity is through making all the servers only accessible by the administrators of networks.
- The Justifiability of Hacking and the Government’s Role This paper discusses privacy in the age of technologies, government hacking, the human right to privacy, and the need for government surveillance.
- Computer Forensics for Solving Cyber Crimes This paper presents research about the deployment of computer forensics in solving cybercrime. The paper brings out a number of cases concerning crimes in the cyberspace.
- Computer Forensics and Investigations A computer forensics examiner may be called to provide evidence and advice in a court of law. Before logs disappear, digital forensics investigators are required to capture them.
- Digital Forensics in Law Enforcement The paper shows that digital forensics in law enforcement is useful in collecting extra proof after an occurrence to support charges against a suspect.
- IT Security: Hacking and Its Components The aim of this paper is to analyze hacking and its components, such as ethical hacking, and to manage cyber security, on the example of the University’s data break-in.
- Social Issues Surrounding Cybercrime Among many social problems that have already been discussed, the issue of rising cybercrime has been on my mind the most.
- Cybercrime and Ransomware: Literature Analysis Criminal justice and the processes that it involves is one of the most multi-layered, controversial, and ever topical areas of legal procedures in general.
- Researching of Cybersecurity and Cybercrime The paper will discuss the technology transfer processes followed by the funding sources for technologies in the cybersecurity field
- Cyber Law and Digital Forensic Science The advantage and disadvantage of external media at the same time is that information is easy to hide, steal, or destroy since it is located on a small object.
- Digital Forensics and Deoxyribonucleic Acid The practice of digital forensics involves analysis of data collected computing devices from a particular crime scene.
- Computer Forensics and Investigations: Basic Procedures In this paper, the author is going to show the basic procedures that ought to be undertaken while performing a digital forensic examination.
- Computer Forensics in the FCC vs. Jack Brown Case In the case of the FCC vs. Jack Brown, this will involve accessing the information that has been stored in different file formats.
- The Council of Europe Convention on Cybercrime of 2001 The Council of Europe Convention on Cybercrime was created to deal with what is well-thought-out to be a unique attribute of cybercrime.
- Cybercrime Legislation in the UAE, the US and the EU Cyber and computer crime definitions were developed after the enhancement of technology, and they improved after years of making proposals.
- The Development of New Technologies: Wireless Hacking Techniques With the rapid development of new technologies, the safety of personal data is expected to increase. The purpose of this paper is to discuss some wireless hacking techniques.
- Cybercrime: Categories and Challenges This essay introduces the concept of cybercrime, informs the reader of its categories, and mentions several challenges that cybercrime presents.
- Sexting and Related Cybercrime Legislation Sexting represents a relatively law phenomenon on the law, with specific legislation dealing with sexting and minors not being present in a majority of US states.
- Gathering, Analyzing, and Presenting Digital Evidence: Computer Forensic Investigators This paper aims at accomplishing four tasks, which are to providing HCC Partners in Life with computer forensic services that would support a case in a court of law.
- Black Hat vs White Hat Hacking This paper explores hacking from the perspective of ethics. In this paper, white hat and black hat hackers are the ethical players and their actions will be tested for ethicality.
- Computer Forensics Investigation Plan The US Constitution prohibits employers from conducting searches on employees. However, the protection does not apply to private organizations.
- The Greater Threat of Cybercrime Versus Cyberattack
- Cyber Bullying: Old Problem in New-Age Packaging – Cybercrime
- Capital Punishment for Cybercrime: The Case in Nigeria
- Bargaining Interpersonal Organization Accounts as a Form of Cybercrime
- Canada and China: Cybercrime and Cryptocurrency
- Corruption, Fraud, and Cybercrime as Dehumanizing Phenomena
- Cybercrime and Its Impact on International Business
- Explaining Cybercrime Using Criminological Theories
- Cybercrime: Fraud and Powerful Invisible Attacker
- Growth, Development, and Policing of Cybercrime in the 21st Century
- Cybercrime Has Become One of the Most Threatening Issues
- How Social Media Has Contributed to the Spread of Cybercrime
- Cybercrime: Identity Theft and New Criminal Opportunities
- The Crime Scene Characteristics for Cybercrime and the Process of Investigating It
- Cybercrime: Preventing the Horrific Crimes on the Internet
- The Protection From Cyberattacks and Cybercrime in Bangladesh
- Does the Pandemic Explain Recent Spikes in Cyber Crime?
- Cybercrime Prevention Measures: How to Avoid Hacking
- The Role of Digital Forensics in Solving Cybercrimes
- Cybercrime: The Latest Ways of Stealing Identity and Money
- Potential Impact of Cyber Crime on the Economy
- Cybercrime and Cyberpiracy Impact on Domestic and Foreign Business
- Cybercrime in the Banking Sector and Its Impact on the Banking Industry
- Development of the Prevention of Cyber Crime in Malaysia
- Good Cybercrime: Trends and Future
- The Solutions for Cybercrimes in Information Technology
- Cybercrimes, Their Types, and Measures That We Take to Keep Us Safe From the Happenings
- Peculiarities of Cybercrime and Security
- How Technology Has Influenced the Evolution of Cybercrime
- The Impact of Cybercrime on the Global Criminal Justice System
- Cybercrime and Society: Identity Theft
- Closing the Space Between Cybercrime and Cybersecurity
- A Fast-Growing Area of Cybercrime
- Cybercrimes: An Unprecedented Threat to Society
- Key Steps to Managing a Cybercrime Scene
- Rights to Anonymity in Cybercrime
- What Is the Role of America in Protecting Corporations From Cybercrime?
- Cybercrime and Its Effects on the World’s Major Countries
- Exploring Cybercrime: Realities and Challenges
- Cybercrime Trends: How to Protect Your Business
- The Rise of Cybercrime in the United States
- How the Russia-Ukraine Conflict Is Impacting Cybercrime
- Cybercrime: A Complete Guide to All Things Criminal on the Web
- Top 5 Cybercrimes and Prevention Tips
- How Does Cybercrime Impact Small Businesses?
- What Are the Different Types of Cybercrimes and Cybercriminals?
- Can We Tackle the Ever-Evolving Threat of Cybercrime?
- What Is the Difference Between Crime and Cybercrime?
- Is Cybercrime Civil or Criminal?
- Why Is Cybercrime Considered a Crime?
- When Did Cybercrime Become a Crime?
- How Can Cybercrimes Be Prevented?
- What Was the First Cybercrime?
- How Does Cybercrime Affect Human Rights?
- Who Is Responsible for Cybercrime?
- What Was the Biggest Cybercrime Ever?
- How Does Cybercrime Affect the Victim?
- What Are the Effects of Cybercrime on Society?
- Which Country Is Top in Cybercrime?
- Does Cybercrime Affect Social Media?
- Where Was the First Cybercrime?
- What Are the Major Categories of Cybercrimes?
- How Does Cybercrime Impact the Economy?
- Which City Is Famous for Cybercrime?
- Who Are the Victims of Cybercrime and Why?
- Are There Defining Characteristics of a Cybercrime?
- What Theory Best Explains Cybercrime?
- Is There a Difference Between Computer Crimes and Cybercrimes?
- What Is the Overlap Between Criminal Justice and Cybercrime?
Cite this post
- Chicago (N-B)
- Chicago (A-D)
StudyCorgi. (2022, June 5). 105 Cybercrime Essay Topics. https://studycorgi.com/ideas/cybercrime-essay-topics/
"105 Cybercrime Essay Topics." StudyCorgi , 5 June 2022, studycorgi.com/ideas/cybercrime-essay-topics/.
StudyCorgi . (2022) '105 Cybercrime Essay Topics'. 5 June.
1. StudyCorgi . "105 Cybercrime Essay Topics." June 5, 2022. https://studycorgi.com/ideas/cybercrime-essay-topics/.
Bibliography
StudyCorgi . "105 Cybercrime Essay Topics." June 5, 2022. https://studycorgi.com/ideas/cybercrime-essay-topics/.
StudyCorgi . 2022. "105 Cybercrime Essay Topics." June 5, 2022. https://studycorgi.com/ideas/cybercrime-essay-topics/.
These essay examples and topics on Cybercrime were carefully selected by the StudyCorgi editorial team. They meet our highest standards in terms of grammar, punctuation, style, and fact accuracy. Please ensure you properly reference the materials if you’re using them to write your assignment.
This essay topic collection was updated on December 27, 2023 .
Talk to our experts
1800-120-456-456
- Cyber Crime Essay
Essay on Cyber Crime
Cyber crime is the most discussed issue of the 21st century. The technology sector world wide is witnessing a boom in the consumer of smartphones and the internet which is raising concerns with regard to the privacy and security of the users. Owing to this reason, it is highly essential for all the users to know about cyber crime & security. As a result, thi topic has become the most favorite topic of the examiner and can often be seen asked in the exams. In this view, students must have information on cyber crime and stay prepared to tackle such topics in the essay question in the English paper.
Introduction
Cybercrime is a dangerous attack a company or an individual may face. There are many cases where the cyber attack has brought massive loss to the company and individuals due to the data hack. We live in a technology-driven era, and every piece of information is now fed on computers. Cybercrime involves an attack on computers and digital devices. These cyber-attacks can prove hazardous not just for the organization, but also for the nation. To date, there are many digital attack cases in India and global, pushing for more security measures. These attacks are also affecting the economy of the country if not controlled in the initial stage.
What is Cybercrime?
Cybercrime or attack is defined as the systematic criminal activity occurring digitally
and done by attackers. There are many examples of cybercrime, including fraud,
malware viruses, cyberstalking and others. Due to these, government agencies and
companies are investing more in the maintenance and hiring of cybercrime experts.
Earlier, cybercrime was committed only by individuals or by small groups. However, now a highly complex cybercriminals network work on attacking the system for data
collection.
Three groups of cybercrimes-
This is the form of cyberstalking, trafficking, and grooming. Over the years, this
This type of cybercrime has been taken seriously by law enforcement agencies. It is
now keeping a track over every such attack on an individual.
Similar to the real world where criminals steal the property, in the cyber world,
attackers steal data. Here, the attacker steals a person's bank details and
misuse the credit card for online purchase. By using malicious software, the
attacker attacks the property to disrupt the system of the organization.
These types of crimes are denoted as cyber terrorism. This can be a terror because
the attacker can get hold of essential documents related to government
projects. An enemy nation or terrorist usually makes such attacks. There are
many cases globally where a terrorist hacks government data.
Apart from these, there is a financial crime where the hacker steals the money of the
user account holder. Moreover, they steal company data and finance.
In this type, the computer system of the person is hacked to get personal
information. In many countries, including India, hacking is a punishable act.
It is quite different from ethical hacking. In normal hacking, illegal use
different types of software to enter the system of the target person. Hacker is
then able to monitor every activity done by the person.
This Cybercrime is about violating copyright and downloading music or movies. In
India, many movies before their releases are leaked on the movie download
sites. In other words , theft is also called privacy, which can bring a huge
loss to the organization.
Cyber Stalking
It is online harassment by an individual or a group of people. Normally, these
stalkers target an individual and harass online. There are many cases of
cyberstalking in India, resulting in the target person ending up taking
Malicious Software
These are computer-based cybercrimes where virus-based software is installed in the
target people or organization computers. This is to damage the system and
corrupt the data of the target.
Laws Related to Cybercrime
In India, there are many cybercrime laws enacted to stop this threat. Be it for
the individual or the organization; these laws help to either bring down the
number of cases or eliminate these digital crimes.
Apart from these laws, as an individual, you also need to take steps to stop these
crimes. Like, not providing your login details, installing trust anti-virus
software and keeping your online profile private can help to act against such
Cybercrime is a significant threat that can bring huge loss to the individual and the
organization. It is essential to follow basic online rules to ensure the safety
of self and the organization.
Benefits of Cyber Crime Essay in English provided by Vedantu
The essay on cybercrime provided by Vedantu is prepared by highly qualified teachers which makes it a reliable source of information. This information could be utilized for a variety of reasons. Being a reliable piece of information the essay will benefit everyone curious to know about the topic.
Following are the highlights of its benefits:
Reliable information
Adaptive to the context
Precise language
Fulfills the requirements of the students for english exam questions
Comprehensive and analytical. The article digs in the depth of the issue and analyzes it through a 360 degree perspective.
The essay could also be used by the students for preparing themselves for the essay question in the English paper. This essay is an excellent guide to understand what the examiner is looking for in the exam. Moreover, the topic of cybercrime is quite a recurrent one in the exam. So the students use this essay to deal with the same topic.
The Essay on Cyber Crime is an excellent guide on averting any possibilities of a cyber attack. On today's date, one is mostly on the internet for a variety of reasons. It becomes essential for one to know important tips that can keep one safe from cyberbullies, thieves, or blackmailers. It is also important for one to understand the right course of actions to be taken in an eventuality of such an incident.
Download the cybercrime essay for students in English on the Vedantu website.

FAQs on Cyber Crime Essay
1. How Does Cybercrime Work?
Group of people or an individual commits most of these cyber-crimes. These criminals use a systematic process to hack and commit these acts. These criminal communities share strategies and tools to launch attacks. Some of the cybercrime techniques
Fast Flux - In this method, the hacker moves data quickly among computers in a botnet, making it challenging to find the right source.
Social Engineering - This method includes using lies and manipulation to trick people into revealing their personal information.
Skimmers - This involves installing a skimming tool in an ATM and stealing the information. You may find such skimming devices in ATMs.
There are some digital criminals targeting organizations to steal personal information.
2. How Cybercrime Affects Society?
Cybercrime can hugely affect society. In 2018, the US faced a loss of $600 billion. As consumers are increasingly allowing technologies to get into their lives, cyber attackers are getting better access. Some of the essential information available are-
Personal health data, sleep schedules, and geo-locations Shopping history, account information, and passive conversations noticed voice-controlled devices, Private conversations on social media accounts.
Your entire life is now available on social media, making it vulnerable to hack or cyber-attack. Attackers use different techniques including- installing malware, virus, phishing, cyberstalking, etc. These can certainly bring loss of lives and data for individuals and organizations. For society, this is a significant loss in the long run. One needs to be very careful when presenting himself socially.
3. How to stay secure in times of cybercrime?
Cybercrime is a real threat posing to society. It is the 21st-century version of theft and blackmailing. There are certain ways one should adopt to prevent any possibilities of cybercrime. Do not disclose the banking details to random people or fill the CVV of your debit or credit cards on an unknown and unverified website. Keep your passwords always discrete. The camera of the laptop should always be covered.
4. Where can I get a cybercrime essay?
One can find a good quality cyber crime essay on Vedantu's website. The essay which is prepared by the expert teachers describes everything that one needs to know about cybercrime. It is the one-stop solution for all your requirements on the topic. Their essay is available in PDF format on the website and could be downloaded on any device. One downloaded essay could be used in offline mode too. If one finds it feasible, the printout of the PDF could also be taken out.
237 Cyber Security Essay Topics, Ideas, and Examples
🏆 best cybersecurity essay topics and examples, 💡 most interesting cybersecurity topics to write about, 👍 good essay topics on cybersecurity, ⭐ simple & easy cyber security essay topics, ✍️ cyber security topics for college, ⌨️ good cyber security essay examples and topics, 🖱️ compelling computer security research topics, ❓ cyber security paragraph questions.
- Benefits and Dangers of Ethical Hacking The advantages of ethical hacking The following are some of the advantages associated with the use of ethical hacking in an organization.
- Sources of Digital Forensic Data With live system data, the aim of the investigator is to capture information concerning volatile data that may disappear when a device powers off or it is disconnected from the network. We will write a custom essay specifically for you by our professional experts 808 writers online Learn More
- Kosovo 1999: Hacking the Military The paper addresses the motivation behind the attacks, the methods of attack, and the responses of the defenders to these attacks.
- Importance of Army Cybersecurity This includes bringing awareness to the cybersecurity issue, involving more people to combat the problem of cyberattacks, and organizing the information based on specialty and tasks that must be completed.
- Cybersecurity and Encryption Analysis: VPN, PKI & Firewalls The end-to-end encryption is the more complex process that can be discussed as the data encryption between the client application and the server provided with the help of additional technologies.
- Société Générale Bank: Effective Security Controls The management of the bank revealed that Kerviel exploited every loophole to hack the computer operations at the bank. It is also important to list the potential risks because it enables the security personnel to […]
- Ethical and Illegal Computer Hacking For the ethical hackers, they pursue hacking in order to identify the unexploited areas or determine weaknesses in systems in order to fix them.
- Cyber Security Technologies The technology is regularly designed to alter the attack surface of a network, making it hard for attackers to access a system and reducing the susceptibilities and predictabilities available at any time.
- Artificial Intelligence in Cybersecurity The use of AI is regulated by a large amount of documentation, which should take into account the current legislation in the country of use and ethical issues related to AI, many of which have […]
- Computer Forensics Tools and Evidence Processing The purpose of this paper is to analyze available forensic tools, identify and explain the challenges of investigations, and explain the legal implication of the First and Fourth Amendments as they relate to evidence processing […]
- Cybersecurity Workforce in Emergent Nations The lack of help from developed countries in the training and education of a cybersecurity workforce for developing nations can negatively affect the former. Public and private organizations also contribute to the development of cybersecurity […]
- Cybersecurity Threats to Educational Institutions The rapid adoption of digital solutions is exposing schools to the cyber-security threat, which is currently the biggest concern that these institutions face as they make a complete shift from the analog to the digital […]
- Sony Corporation Hacking and Security System The organization had to stop the hackers and ensure information did not flow freely but it was unfortunate, as the company sought the services of the California court because it had no capacity to deal […]
- Cybersecurity in the Financial Services Industry In reaction to ransomware attacks, a business such as a bank may have to spend a substantial amount of money, which may cause customers to lose faith in the safety of their funds.
- The Impact of Mobile Devices on Cybersecurity The very popularity and extent of the use of mobile computing devices and the internet creates a special vulnerability to businesses.
- Ethical, Legal, and Social Implications of Hacking So as to discuss the ethical, lawful, and ethical inferences of this concern, people need an understanding of the phrase ethical hacking.
- Computer Forensics: Identity Theft The forensics process that is maintained in the framework of computer-related technologies provides professionals with the opportunity to gather, analyze, and report on the information.
- Preparing a Computer Forensics Investigation Plan However, if the information is thought to be contained in the permanent storage, then a computer has to be shut down before transporting it to a laboratory for forensic analysis. The first step in the […]
- The Role of U.S. Government in Cybersecurity According to the government of the United States, cybersecurity is among the most serious economic and security challenges that the government needs to deal with.
- Hacking: Positive and Negative Perception The possible advantage of cooperating with hackers for security systems mangers of international organizations and governmental organizations is the probability to recruit them and use their knowledge to empower different organizations to improve their security […]
- The Department of Homeland Security’s Cybersecurity Mission Cybersecurity is evolving rapidly, and DHS’s cybersecurity mission is equipped with models adapting to the ever-changing security and information dynamics. The DHS cybersecurity mission is designed with models that adapt to changing dynamics and landscapes.
- The Future Career in Cybersecurity During the interview, it is necessary to highlight the knowledge of working as a graph as a mathematical theory and the simple use of spanning trees in cybersecurity.
- The Biggest Cybersecurity Treat to Expect First of all, all employees who somehow use the Internet of Things devices and have access to the corporate IoT network are to be trained to utilize it correctly.
- Securing Offboarded Employees: Modern Cybersecurity Strategies Disgruntled employees can be potentially dangerous to the whole company’s well-being due to cybercrimes that can affect the entire company’s work.
- Advanced Research Methods in Cybersecurity Performance measurements refer to the internal functions of the company and ways in which cybersecurity management contributes to the accomplishment of critical tasks within the firm.
- Gaps in Cyber Security Caused by BYOD In conclusion, these vulnerabilities caused by the insufficient regulation and general unpreparedness of organizational and public networks expose facilities that use BYOD to severe risks of data leaks and hacker attacks.
- Cybersecurity Threats in Physician Practice The purpose of the source is to inform readers of the strategies to help healthcare professionals identify, avoid and respond to ransomware dangers.
- Digital Forensic Analysis of Fitbit The comparison of the results and the analyses of the data as a result of the research gave the authors of the article a conclusion in regards to the methodology that has evidence-based results in […]
- Cybersecurity Contingency & Incident Review Process Next, it is necessary to implement various stages of digital transformation of cybersecurity, which include improving the maturity of enterprises in cybersecurity issues and the use of new solutions.
- Forensic Accounting and Cyber Security The recent trend of increased exposure due to the access of extended financial and fraud concerns by social media and the internet has necessitated the need to curb the tendency.
- Global Cybersecurity in the 21st Century Research Question: Is there a significant connection between the US President’s approach to cybersecurity and the actual presence of the given phenomenon?
- Hacking Prevention: Mobile Phone Anti-Virus However, the less discussed and addressed subject is the cybersecurity of mobile phones, which are among the most used and vital devices for the majority of the population.
- Legal Risks of AI Cybersecurity in the European Union Thus, this paper seeks to fill the gap on whether or not safety and security can be covered in cybersecurity for AI by the same rules that are used in private law. The EU has […]
- Cyber Security: Critical Infrastructure Protection Objects of forensic science are storage mediums that are not part of other devices and which fulfill the function of information storage as the main one.
- Cybersecurity: Firewall and Testing The most effective and reliable way to test a software program of a firewall for its security would be firewall penetration testing.
- Relation Between Cybersecurity and Cybercrime Meanwhile, one should not assume that cybersecurity is the prerogative of technicians and software engineers only since the consequences of a breach will affect the entire business or private life of those not associated with […]
- Cybersecurity in 2021-2022: Cybersecurity Advancements In IoT, Blockchain is being utilized to protect connected devices through decentralization and encryption, adding to the evolving nature of system security.
- Encryption and Hacking Techniques There are several advantages of text-based encryption, and they include the fact that the data can be used across different devices through the concept of multi-device encryption techniques.
- The US, Russia, and China Cybersecurity Conflict The current situation in the space of cybersecurity provides a significant example of how complicated this area of National Security and its influence on foreign politics can be.
- Cybersecurity and Geopolitics Relationship Provision of security to information technology and the tools used in the technology is also paramount. Cyber security is also described as measures and operations that are put in place to be to ensure that […]
- Cybersecurity and Corporations’ Input to It Whatever committee or board of directors is in charge of overseeing cybersecurity risks, the primary goal is for an organization to have an integrated approach to preparing for and protecting against cyber incidents and detecting […]
- Cybersecurity and Corporations’ Role First, it is worth indicating some of the key reasons for corporations to be in the center of cybersecurity discussion. In April, the company rejected the possibility of a data breach and apparently did not […]
- Cybersecurity and Geopolitical Issues Geopolitics is the study of integration and effect of earth geography and physical outlay on the political structures, and international relations and reforms that affect the same at different levels.
- Virtual Reality and Cybersecurity As a result, it is the mandate of the framework entities to establish solutions to the inherent barriers to the implementation of the business plan.
- Cybersecurity Policy Regarding Critical Infrastructures The article will explicitly analyze the processes behind cybersecurity development as well as the impact of the cybersecurity polies to the global security policies.
- Cybersecurity: Critical Infrastructure Control Systems The most vital stages of this nature include the analysis of the situation, the assessment of goals to make sure that they are realistic, and the expected effectiveness of implementing new policies.
- Cybersecurity in the United States Thus, the current research project is going to address the following question: Is there a significant connection between the US President’s approach to cybersecurity and the actual presence of the given phenomenon?
- Cybersecurity: The Matter of National Security However, if the security of cyberspace is critically evaluated and all the risks eliminated, cyberspace can be an asset that will continue to transform the world.
- Cybersecurity Advancements in Electric Power Systems Therefore, there will be an increase in the volume of work performed, a reduction in design time and an increase in the quality of work through the use of technology in the next five years.
- Cybersecurity Dangers and Their Analysis The officer clicks the file, and the malware attacks the system stealing the data and bypassing some security measures. The cyber security framework under the NIST is helping organizations to understand and manage cybersecurity.
- The US and Apple Relationship in the Field of Cybersecurity In this paragraph, an important aspect is to determine the degree of interaction between the two structures. This paper argues that in times of crisis, such powers should be surrendered to the more considerable public […]
- Data Management and Cybersecurity Namely, the principal standard of the HIPAA, as well as the concept of cybersecurity, have proven to factor into some of the key aspects of my professional and personal life.
- Cybercrime and Cybersecurity as Challenges One will also learn the defensive cyber security technologies and techniques used in modern organizations to protect systems data and achieve Knowledge of the maintenance and design of reliable and safe information systems.
- Digital Forensics Tools and Software One of the most famous software programs for digital forensics is Autopsy, a toolkit that examines the images present on a device’s hard drive.
- Tim Cook’s Leadership and Apple’s Cybersecurity In this paper, the main types of leadership that can be applied to the leadership style of Tim Cook are considered.
- Cybersecurity Weaknesses: The Case of LinkedIn The Internet has become the largest storage of personal and corporate information in the history of the world. The data relating to hundreds of millions of users was leaked online in the Dark Web segment […]
- The Importance of Leadership Skills in the Field of Cybersecurity The wider the information networks cover the world, the more frequent and dangerous cyber-attacks are, and the more cybersecurity specialists become in demand.
- White Hat and Black Hat Hacking On the other hand, White Hats work with companies and help them identify weaknesses in their systems and fix relevant vulnerabilities to ensure that attackers cannot illegally gain access to data.
- Modern Cybercrime: Most Recent Threats and Cybersecurity This is due to the fact that the Internet is a public open system in which data moves uncontrollably and can be discovered, intercepted, or stolen if the correct knowledge of the equipment is applied.
- Cyber Security Issue: RansomWare Until the victim pays a specific amount of money to the attackers within a particular time, cybercriminals can use the virus mentioned above to access the user’s sensitive personal or organizational information. The infection and […]
- Cybersecurity Strategy, Law, and Policy Team Assignment It may be critical to prevent cybersecurity breaches or data leaks to maintain the effective functioning of the government and ensure the sovereignty of the country.
- The Cybersecurity Threat Landscape The threats may come from different sources, and the criminals may focus on distinct vulnerabilities in the security of the system.
- Public-Private Partnerships for Election Systems Cybersecurity In public contracts, the private sector provides the service directly to the public and bears all the associated end-user risks. Private parties can use all the gained knowledge and expertise to conduct security assessments of […]
- Solving the Cybersecurity Workforce Crisis Since cyber security specialists are highly demanded in the current market, the private sector has been offering increased compensation in comparison with the government sector, which has led to decreased interest in IT positions in […]
- Cryptographic Algorithms: The Use in Cyber Security Cryptographic protection of a system depends on two factors, 1) the strength of the keys and effectiveness of associated protocols, and 2) protection of said keys via key management.
- Assessment of Cybersecurity Program Maturity Padgett-Beale Financial Services must choose the appropriate framework and standards, determine required regulations and laws to comply with, and identify the best practices for maturity assessment to achieve an impenetrable cybersecurity management program.
- Cybersecurity Implementation Plan for PBI-FS Therefore, the current plan will define the objectives, goals, and objectives, and scope of the implementation. The implementation of the cybersecurity management plan pursues both business and project goals and objectives.
- Facebook Compatibility With Padgett-Beale Cybersecurity Philosophy The purpose of this paper is to evaluate Facebook on the subject of cybersecurity and compatibility with Padgett-Beale’s cybersecurity philosophy and goals.
- Cybersecurity Issues in Industrial Critical Infrastructure This way, the author analyzes the potential impact of various cybersecurity threats capable of interrupting the stability of the supply of energy to communities and industries.
- Supply Chain’s Cybersecurity and Risk Analysis Since there are so many parties involved, it is crucial to assess every part of the process, from obtaining the raw material to the delivery to the customer. Cybersecurity is the critical answer to most […]
- Amazon Inc.’s Business Profile and Cybersecurity On the contrary, Amazon has continued to rise in the industry and has expanded from selling only books to trade in nearly any product and providing various services.
- Integrating Cybersecurity Framework With Information Technology Governance Frameworks ISMS builds a model of relationships between the aforementioned activities, and, as Almuhammadi and Alsaleh argue, companies “understand their cyber security risk management approach and what are the processes in place to manage the risk”.
- Cybersecurity, Ethics, and Privacy in the Global Business Environment Therefore, the purpose of this paper is to cover the types of possible threats and mitigation methods, explain the importance of a continuity plan, and outline ethical and privacy concerns for organizations.
- Technology Acceptance Model and Cybersecurity In this context, the implementation of TAM in the company is critical for the effective functioning of the organization. In this context, the introduction of TAM leads to the fact that satisfaction directly affects the […]
- Cybersecurity: Multi-State Information Sharing and Analysis Center The MS-ISAC also advises the agencies on the best tools available in the market that provide the best protection of the government systems and data.
- Cybersecurity Strategy and Plan of Action Padgett-Beale’s primary intention of merging the company was to relocate the call epicenter to a property owned by the company roughly 10 miles from the company’s previous location and opposite the newly released Padgett-Beale resort.
- Digital Forensic Examination, DVR Another application would be to determine the network’s or a user’s IP and track their online activity. The information can be used to determine an unknown individual’s location and possibly identity, or for a known […]
- Cybersecurity and How It Impacts Identity Protection and/or Ransomware Firstly, organizational leadership should not undervalue the importance of cybersecurity since the risk of losing the data stored in the company’s database may harm the corporate reputation and trustworthiness.
- Cybersecurity in the Energy Sector The stable supply of energy is the key to the normal functioning of American society, as it fuels all essential industries that ensure the vitality of the nation.
- Cybersecurity for Open Data Initiatives Governments continue to play a vital role in the open data movement.Data.gov was developed under OPEN Government Data Act; this is Title II of Foundations for the Evidence-based Policymaking Act.
- Sifers-Grayson Company: The Cybersecurity Breach Finally, the recommendations, as per the improvement of the incident response capability, are introduced to ensure the elimination of the identified drawbacks and the compliance of the engineering company with the security requirements presented by […]
- Computer Forensic Incident All evidence should be collected in the presence of experts in order to avoid losing data as well as violating privacy rights.N.
- Cybersecurity Necessity and Benefits Second, the exploration of human factors in the framework of cyber-security can assist in resolving the issues of understanding a defender’s cognitive state, possibilities for automation, and an attacker’s subjective traits.
- Cybersecurity Incident Response and Risk Minimization Such plan or strategy represents a list of steps, which should be immediately taken in case of a cyber-attack to limit the potential damage and reduce expenses.
- Internet Hacking and Cybersecurity Conundrum Analysis Many people have gained access to computer systems, the Internet, and related products and services, leading to the emergence of cyber-related threats. Cybersecurity improvements are vital to the continuous developments in information technology, national security, […]
- Internet Hacking and Cybersecurity Conundrum Therefore, the increasing number of attacks during the pandemic could be handled with the help of machine learning and have the numerous human workers assigned to less crucial tasks that actually require human judgment.
- Government and Private Sector in Cybersecurity Richards highlights the government’s leading role in the context of cyber threats while stating that the number of attacks is still on the increase.
- Hacking as a Crime and Related Theories The move to embrace the novel technology has led to the emergence of a new form of crime and behavior referred to as “hacking”. Today, the term is used to refer to individuals engaged in […]
- Ethical Hacking: Is It a Thing? Computer programmers implemented the term ‘hacker’ at the beginning of the 1960s in the framework of a positive definition for an individual of dexterous software development skill.
- Computer Network Security Legal Framework With the introduction of cloud computing, the need of data protection has been rising significantly within computer networks to facilitate the protection of Intellectual Property among the users.
- Computer Forensics and Audio Data Retrieval Advanced technology in the modern society has contributed to the increase in computer and computer supported criminal activities due to the soaring increases in the number of internet users across the world and computerization of […]
- Cyber Security: Security Audit On the issue of computers and laptops, I learned from the administration that each laptop was specifically assigned to a single person who was entrusted with a password known to him and the organization’s administration […]
- Computer Forensics: Data Acquisition Data acquisition is a branch of computer forensics concerned with the retrieval of data originally located on a suspect medium such as a hard drive.
- Computer Forensic Timeline Visualization Tool The necessity to save time in computer forensic investigations is the basis of the tool that Olssen and Boldt came up with.
- The Qatar Independence Schools’ Computer Network Security Control The result of the interviews mainly outlined several common themes and patterns in terms of the design of the proposed security system.
- Computer Sciences Technology and HTTPS Hacking Protection Many are assured when they see the SSL symbol of a lock at the bottom of the screen and feel their information is confidential and the website is protected.
- Moral Issues Surrounding the Hacking of Emails The devises to enter into another people’s email and steal information in the email is called Email Hacking. It should noted that stealing of valuable information through email hacking has become a phenomenon in both […]
- Hacking Government Website From the View of Right and Justice Computer crimes refers to the use of the computer system or the internet to commit criminal activities A computer crime is an unlawful act done via a computer or a network and some of the […]
- COBIT5 vs. ITIL4 in Cybersecurity Significantly, ITSM is the alignment of information systems and enterprise IT services with business and the needs of the customer who is the end-user.
- Cybercrime and Cybersecurity: Data Protection One of the biggest Constitutional concerns for electronic surveillance as well as search and seize of evidence is protected by the Fourth Amendment which limits any such activities against the private persons, property, or effects […]
- Cyber Security Threat and Its Impact on the UAE In 2018, the UAE government and private sector were the subject of a total of 230 cyber attacks, as The National UAE reports.
- Agility and Situational Awareness in the Context of Cyber Security As a result, measures should be implemented to create cyber security, which will protect the information resources of an organization from damage.
- Research Tools Used by Computer Forensic Teams Computer Forensics is a branch of digital forensics which is used in “identifying, preserving, recovering, analyzing and presenting facts and opinions about the information”.
- Cybersecurity and Social Networks Recently, there have been many trends the security of information and communication technologies, in particular, due to the expansion of the reach of social media which increase the size of social network, which has taken […]
- Business and Cybersecurity Research Thus, a more sophisticated theoretical approach is taken to represent the goals of cyber security. A mediating variable, in turn, is the effectiveness of cyber security measures perceived from theory- and practice-related standpoints.
- Quality Control of Digital Forensics The quality control over computer forensic products is necessary because of the growth of the Internet services. Thus, the investigator and the lab are challenged not only with solving a case but also providing the […]
- Windows Logs: Improving Cybersecurity The specified event points to the need to configure the current settings of the master browser in order to address possible security issues and close the loopholes that potentially make the computer vulnerable to malware.
- Cybersecurity: Weak and Strong Passwords The strong passwords have a low probability of being guessed because the amount of possible iterations and combinations is extremely high.
- “Evolution of Federal Cyber Security” by J. Roth Even after training, the GAO report continued to demonstrate system control deficiencies due to failures in the identification of enough boundary security mechanisms, breakdown in the need to know, insufficient restriction of physical access, and […]
- The Different Sides of Hacking In a general sense, computer hacking involves the intrusion of the computing privacy of other people, damage of the computing property of other people like files, software etc.or the theft of private information by unauthorized […]
- US Brokerage Hacking by India Issue The personal accounts of the defendants were used to purchase shares of stocks, following which they hacked into other people’s accounts and made good use of their passwords and usernames.
- Cyber Security in the Energy Sector The organization’s innovation can be catalytic for the change in the industry of energy since the largest sources of carbon emissions are power plants that generate energy by burning fossil fuels.
- Computer Forensics in Criminal Investigation In this section, this paper will address the components of a computer to photograph during forensic photography, the most emergent action an investigating officer should take upon arriving at a cyber-crime scene, the value of […]
- Computer Forensics and Cyber Crime Due to age characteristics, the insufficient educational activity of parents, the provision of unlimited opportunities in the online environment, and also due to the low media literacy of the population, people can become victims of […]
- Cyber Security: Shadow Brokers Hacker Group A concealed group of hackers stole several disks containing secret data belonging to the National Security Agency in 2013; In 2016, they announced an auction to sell off the data they had obtained illegally; […]
- Cybersecurity as a Leadership Challenge Cybercrime can lead to the leakage of important data, system interference, and the delivery of unsatisfactory services to consumers. This sophistication has amplified the insecurity of information systems to the extent of creating more threats […]
- Shadow Brokers Hacker Group and Cyber Security Industry Therefore, in order to prevent the recurrence of such attacks, the N.S.A.needs to strengthen the security system of particularly essential information to eliminate its diversion.
- Deutsche Telecom Company’s Cyber Security The present work deals with the issue of DDoS attacks and builds a case on one of the well-known IT companies to single out the problem, the immediate solutions and preventive practices, and the lessons […]
- Cybersecurity: Deutsche Telekom Company’s Case The example of Deutsche Telekom proves the importance of the development of cybersecurity programs and strategies to protect users and their interests.
- Cybersecurity Risks Affecting Enterprises From a national security standpoint, it is crucial to know and understand the nature of the enemy and be prepared for an increase in cyberterrorism attempts.
- Cyber Security and Employees The major factors that define the thriving of cyber ganging are the insufficient level of employees’ competence, the lack of knowledge about the technical side of information protection, and non-compliance with safety standards.
- Cybersecurity Directives and Laws Describe the National Strategy for the Physical Protection of Critical Infrastructures and Key Assets and how it attempts to protect cyber assets.
- Cybersecurity and Vital Elements The focus of any risk management effort is a standard system or a framework that help organizations and individuals to manage integrity, confidentiality, and data and ensure critical resources availability.
- Emerging Cyber Security Approaches and Technologies These emerging cyber security approaches and technologies are unique and new, and they look promising for securing critical infrastructures in the cyberspace.
- Cybersecurity Dilemmas: Technology, Policy and Incentives The value of the assets determines the amount of time and resources that can be invested to protect a particular system.
- Hacking: White, Black and Gray Hats Living in the era of the Internet and online technology increases the vulnerability of the information stored online and on electronic devices.
- A Duty of Care for Cyber Security Hence, the sensitive data can be easily accessed by cyber criminals in the event that the cloud service is breached by users.
- Digital Forensics: Open Source Tools The National Software Reference Library is a project at the National Institute of Standards and Technology, the primary goals of which are to store all existing software, file profiles, and file signatures and to provide […]
- Digital Forensic Methodology In the event that sufficient information is available, the required system configuration should be developed by ensuring that the forensic software and hardware are established and validated.
- Automotive Industry’s Cybersecurity and Threats It is significant to ensure the security of this system because it focuses not only on the audio and video entertainment but also allows to control navigation system and manipulate the behavior of the car.
- Cybersecurity and Risk Control Implementation The first component of the risk treatment framework refers to the decision not to go through with the procedures that may present a risk; the second one stands for the minimization of the possibility of […]
- Online Predators and Childrens’ Cybersecurity To win the battle against online predators it is important to craft laws that were created by people with a thorough understanding of how perpetrators utilize information systems and the Internet to commit sexually-related cyber […]
- Computer and Digital Forensics and Cybercrimes This has greatly affected the success of computer forensics and it is the main drawback in this area. The world is now safer due to the increasing usage of computer forensics in court cases.
- Cyber Security’s and Counter Terrorism’ Intersection Realization of national interests is the concern of many states in the current international and security is the main challenge that each government is trying to cope up with given the fact terrorists are ever […]
- Cybercrime, Digital Evidence, Computer Forensics The website “howstuffworks” carries an article discussing the basics of computer forensics, this is a good example of a website that is useful in explaining or understanding the reality of cybercrime and digital evidence. Not […]
- Middle East Cybersecurity, E-Government, Ecommerce The findings in the research revealed that five main issues led to the reluctance in the adoption of e-commerce and e-governance by the Emirates.
- Growth Hacking and Marketing Methods As a result, it could be observed that the combination of the growth hacking methods and the permission-based marketing appear to be one of the most efficient techniques towards marketing that is low-cost and effective.
- Cybersecurity: Stuxnet Virus Cyber security is one of the major concerns of governments in the contemporary world. It is important to note that in case of Stuxnet the three aspects prove to be vulnerable.
- Ways to Stop Cell Phones Hacking Although it is in the view of many that their phones cannot be hacked as they only protect their computers from hacking, mobile phone operators are more predisposed to being hacked since a mobile operator […]
- Banking Sector Cyber Wars and International Hacking Flaws in the network allow hackers to access the systems. In efforts to reduce hacking in the country, a number of police units have been formed.
- The Threats of Cyber Security Under the PPD-21, the owners of the critical infrastructure will work with the government to hasten the process of strengthening the national critical infrastructure in terms of the much needed security.
- Two Greatest Hacking Systems in the USA Appropriating intellectual output of someone else is also a computer malpractice that is intolerable. Generally, Computer malpractice is seen when a person shows hasty and careless conducts or behaviors when making use of computer systems.
- Cybercrime: Gary McKinnon’s Hacking Event It is the lack of effective controls that accounts for most hacking incidences, as depicted by the case of Gary McKinnon who was able to gain unauthorized access to NASA and pentagon systems, deleting crucial […]
- Important Problem of Cybersecurity Simulations The information stored in the company’s database was encrypted to create confidence in the customers on the security of the data.
- Analysis of Mandiant Cyber Security Company The company’s innovation theories and products need to accommodate other companies that do not view cyber crime as a major risk on their systems.
- Leadership: Mandiant Cyber Security Company Kevin Mandia is the founder and the CEO of the company. The achievements behind Mandiant Cyber Security Company owe its success to the leadership styles exhibited in the firm.
- Adrian Lamo’s Hacking: Is It Right? The example of Galileo introduces a theory about the construction of the Solar System that was the target of interest of the well-known scientist.
- Computer Forensics and Digital Evidence When electronic data has been collected to identify the kind of the incident and introduce evidence of the crime, it is important to organize a meeting with the witness who can provide details of the […]
- Cyber Security Threat Posed by a Terrorist Group These among other features of the internet have been identified to form the basis of the cyber terrorism attacks. A comprehensive international collaboration among investigators and prosecution teams in cases of cyber attacks have also […]
- Information Security Fundamentals: Computer Forensics In addition, the paper provides an overview of the techniques used in obtaining evidence from the internet and web resources, the types of evidence that can be recovered from electronic and computer resources, and the […]
- Computer Forensics Related Ethics Due to advancement in technology, individual information can be kept in databases, the risk of accessing this data is evident and this necessity the need of such a law so as to ensure security.
- The Cyber Security Act of 2009 Analysis This would contribute to enormous benefits to both the government and private stakeholders by ensuring a cyber security strategy that serves the interests of all.
- Air Force and Cyber Security Policies The use of technology in processing financial transactions implies that there is need to boost the trustworthiness, security, resilience, and reliability.
- The Role of Computer Forensics in Criminology In fact, since the development of the virtual machine monitors, the live-state analysis in digital forensics has become common and easy to understand.
- Ethical Hacking: Bad in a Good Way Introduction of personal computers led to the increase in the number of hackers as well as hacker targets were widened. Many hackers lack the skills to damage network systems in a major way.
- Hacking: Social Engineering Online The information is fed to the main web site that’s runs the hacking software, where the information is sorted according to various numbers.
- Cyber Security in Private and Public Sectors The US has the Health Insurance Portability and Accountability Act that ensures that patients’ data remain accessible only to the authorized segment of the staff.
- Cyber Crime and Necessity of Cyber Security This is one of the policies that has been proposed to curb cyber crimes and is being debated in the congress.
- Cybersecurity in the Energy Industry In this regard, in the event that a cyber attack is launched against the energy sector, it is bound to have far reaching consequences.
- Ethics in Computer Hacking Hacking by no means follows ethics; the infiltration is to the benefit of hacker and loss of users of computer system, network or website.
- Computer Forensics and Investigations It is crucial in the investigation of crimes that are related to the manipulation of computer systems. For digital evidence to be admissible in court, investigations should be conducted in a manner that adopts the […]
- Basic Operations of Computer Forensic Laboratories All computer forensic laboratories in the US have to adhere to the national standards before they could be certified. Standard computer forensic equipment is used to support standard procedures and conditions in the laboratories.
- Introducing Cybersecurity Policies: Challenges and Solutions The major purpose for establishing security guidelines is to set an organization’s data security standard and describe the role of employees in safeguarding the documents of the firm, as well as the significance of a […]
- Computer Security Breaches and Hacking To avoid such an attack in the future, it is advisable to keep both the client and server applications up to date.
- Analysis of BJG Cybersecurity Consultants
- Analysis of Cybersecurity and Risk Management
- Analysis of Cybersecurity Metrics as Well a Governmental
- Analyzing the Impact of Mobile Devices on Cybersecurity
- Assessing the Impact of Cybersecurity Attacks on Power Systems
- Building Cybersecurity Awareness: What Should Both Companies and Consumers Do to Protect Themselves?
- Current Practice Analysis for IT Control and Security
- Why Cybersecurity Is Important?
- Cybersecurity in Banking Financial Services Secto
- Cybersecurity in the European Union: Resilience and Adaptability in Governance Policy
- Cyber Security : Is No Silver Bullet For Cybersecurity?
- Dealing With Cybersecurity Threats Posed by Globalized Information Technology Suppliers
- Emerging Technologies That Impact the Cybersecurity Field
- Hacker’s Culture and Cultural Aspects of Cybersecurity
- How Cybersecurity Is an Aspect of Security?
- How Cybersecurity Is Important Resources?
- How Policies, Laws and Regulations Affect the Cybersecurity Field?
- Is Cybersecurity a Big Deal?
- Risk Assessment Uncertainties in Cybersecurity Investments
- What Is Cybersecurity?
- When Cybersecurity Policy Is Discussed the Topics Often?
- Why Computer Scientists Should Care About Cybersecurity?
- Access Single Most Important Cybersecurity Vulnerability Facing IT Mangers
- Model for the Impact of Cybersecurity Infrastructure on Economic Development in Emerging Economies: Evaluating the Contrasting Cases of India and Pakistan
- Cybersecurity and Its Importance in the Modern World
- Architecture for Managing Knowledge on Cybersecurity in Sub-Saharan Africa
- Benefits of Using Cybersecurity
- Border and Cybersecurity in the United States
- Botching Human Factors in Cybersecurity in Business Organizations
- Companies Responsibilities in Enhancing Cybersecurity Chapter
- Cybersecurity and Law Enforcement
- Cybersecurity and Organizational Change Concept Map
- Cybersecurity at European Level: The Role of Information Availability
- Cybersecurity for Critical Infrastructure Protection
- Cybersecurity for Digital Financial Service
- Cybersecurity Policy Making at a Turning Point: Analysing a New Generation of National
- Effect of Bring Your Own Device (BYOD) on Cybersecurity
- Human Aspects in Cybersecurity on a Government Agency and a Private Organization
- Improvement of Cybersecurity Is Necessary
- Most Important Cybersecurity Vulnerability Facing It Managers Computer Knowledge
- Obama Administration’s Policy Views on Cybersecurity
- Review of Cybersecurity Risks of Medical Device Software
- Small Business Cybersecurity and the Public Cloud
- The Influence of Cybersecurity Define the Hacker Motives
- Effect of Cybersecurity on Higher Education
- Importance of Cybersecurity for The Future
- Role of Cybersecurity and Its Effects on the World
- Why Should Computer Scientists Care About Cybersecurity?
- What Are the Roles and Responsibilities of an Organization in Considering Cybersecurity?
- What Are Three Models for Sharing Cybersecurity Incident Information?
- What Are the Private Sector and Public Sector Cybersecurity Issues?
- How Do Policies, Laws, and Regulations Affect the Cybersecurity Field?
- How to Improving Password Cybersecurity Through Inexpensive and Minimally Invasive Means?
- What Kind Are International Cybersecurity Collaboration Initiatives and Multinational Cybersecurity?
- What Is the Most Important Cybersecurity Vulnerability Facing Managers in Computer Science?
- What Are New Concepts for Cybersecurity in Port Communication Networks?
- What Does Cyber Security Do?
- Is Cyber Security a Promising Career?
- What Are the Three Major Threats to Cyber Security Today?
- What Qualifications Do You Need for Cybersecurity?
- What Is a Cyber Security Example?
- What Are the Main Problems With Cyber Security?
- What Is the Biggest Threat to Cyber Security?
- What Are Cyber Security Tools?
- What Is the Risk in Cyber Security?
- What Is the Best Cyber Security?
- What Is Wireshark in Cyber Security?
- Which Are Fundamentals of Petroleum Energy & Mitigating Global Cybersecurity Attacks?
- Which International Cybersecurity Collaboration Initiatives and Multinational Cybersecurity?
- Which Vulnerability Assessments and Mitigating Global Cybersecurity Attacks on the Enterprise?
- Who Is the Founder of Cyber Security?
- What Are the Seven Types of Cyber Security?
- What Is the Most Significant Cybersecurity Company?
- Chicago (A-D)
- Chicago (N-B)
IvyPanda. (2024, February 27). 237 Cyber Security Essay Topics, Ideas, and Examples. https://ivypanda.com/essays/topic/cybersecurity-essay-topics/
"237 Cyber Security Essay Topics, Ideas, and Examples." IvyPanda , 27 Feb. 2024, ivypanda.com/essays/topic/cybersecurity-essay-topics/.
IvyPanda . (2024) '237 Cyber Security Essay Topics, Ideas, and Examples'. 27 February.
IvyPanda . 2024. "237 Cyber Security Essay Topics, Ideas, and Examples." February 27, 2024. https://ivypanda.com/essays/topic/cybersecurity-essay-topics/.
1. IvyPanda . "237 Cyber Security Essay Topics, Ideas, and Examples." February 27, 2024. https://ivypanda.com/essays/topic/cybersecurity-essay-topics/.
Bibliography
IvyPanda . "237 Cyber Security Essay Topics, Ideas, and Examples." February 27, 2024. https://ivypanda.com/essays/topic/cybersecurity-essay-topics/.
- Security Management Essay Ideas
- Cyber Bullying Essay Ideas
- Internet Research Ideas
- Computer Forensics Essay Topics
- Data Mining Titles
- Crime Prevention Research Topics
- Hacking Essay Topics
- Cryptocurrency Essay Ideas
- Identity Theft Essay Ideas
- Viruses Research Topics
- Cryptography Paper Topics
- Encryption Essay Titles
- Internet Privacy Essay Topics
- Digital Transformation Topics
- Software Engineering Topics

Essay on Cyber Crime
Students are often asked to write an essay on Cyber Crime in their schools and colleges. And if you’re also looking for the same, we have created 100-word, 250-word, and 500-word essays on the topic.
Let’s take a look…
100 Words Essay on Cyber Crime
Introduction to cyber crime.
Cybercrime refers to illegal activities conducted through the internet. It’s a fast-growing area of crime, with more criminals exploiting the speed, convenience, and anonymity of the internet.
Types of Cyber Crime
There are many types of cybercrimes. These include hacking, where unauthorized access is gained to a computer system, and identity theft, where personal information is stolen and used fraudulently.
Preventing Cyber Crime
Preventing cybercrime is crucial. This can be achieved by using strong, unique passwords, keeping software and systems updated, and being cautious of suspicious emails or websites.
Cybercrime is a significant issue in today’s digital age. Awareness and proper precautions can help in preventing these crimes.
Also check:
- 10 Lines on Cyber Crime
- Paragraph on Cyber Crime
- Speech on Cyber Crime
250 Words Essay on Cyber Crime
Introduction.
Cybercrime, an umbrella term encompassing a variety of offenses committed using digital technology, poses a significant threat to the modern world. As our reliance on technology increases, so does the potential for misuse, leading to a surge in cybercrimes.
The Nature of Cybercrime
Cybercrimes can range from financial theft, identity theft, cyberstalking, to more complex forms like cyber terrorism and cyber warfare. They exploit the anonymity provided by the internet, making them difficult to trace, investigate, and prosecute.
Impact of Cybercrime
The impact of cybercrime extends beyond financial loss. It can cause significant psychological harm to victims, damage reputations, and even pose threats to national security. In a digital world, the effects of cybercrime are far-reaching and potentially devastating.
Preventing Cybercrime
Preventing cybercrime requires a multi-faceted approach. It involves not only technological solutions but also legal and educational measures. A robust cybersecurity infrastructure, stringent laws, and increased public awareness are crucial to mitigating the risk of cybercrime.
In conclusion, as technology advances, so too does the sophistication of cybercrimes. Combating this growing threat requires a comprehensive approach that combines technology, legislation, and education. The fight against cybercrime is a shared responsibility, requiring collective effort from individuals, organizations, and governments alike.
500 Words Essay on Cyber Crime
In the digital age, our reliance on technology has given rise to a new form of criminal activity known as cyber crime. This term encapsulates any illegal activity that utilizes a computer as its primary means of commission. Cyber crime has become a critical concern due to its widespread impact, affecting individuals, businesses, and even nations.
The Different Forms of Cyber Crime
Cyber crime manifests in various forms, each carrying its unique implications. Identity theft, for instance, involves unauthorized access and use of personal information for fraudulent purposes. Another common type, cyberstalking, uses digital tools to harass or threaten individuals. More complex forms of cyber crime include cyberterrorism and cyber warfare, which target national security and infrastructure.
The Impact of Cyber Crime
The impact of cyber crime is far-reaching and multifaceted. On an individual level, victims may face financial loss, emotional distress, and privacy invasion. For businesses, the implications can be devastating, leading to significant financial losses, reputational damage, and loss of customer trust. On a national level, cyber crime can threaten a country’s security, economy, and infrastructure.
Preventing cyber crime requires a multi-pronged approach. On a personal level, individuals must take precautions such as using strong passwords, regularly updating software, and being cautious of suspicious emails or links. Businesses, on the other hand, need robust cybersecurity measures, including firewalls, intrusion detection systems, and regular employee training. Governments must also play their part, enacting robust cyber crime laws and cooperating internationally to apprehend and prosecute cyber criminals.
Legal and Ethical Considerations
The legal landscape surrounding cyber crime is complex and continually evolving. Jurisdictional issues often arise, given the borderless nature of the internet. Ethically, the debate around privacy and security is pertinent. While law enforcement agencies advocate for backdoors into encrypted systems to combat cyber crime, this raises concerns about potential misuse and invasion of privacy.
The Future of Cyber Crime
As technology advances, so does the sophistication of cyber crimes. Future threats could involve artificial intelligence and machine learning, making detection and prevention even more challenging. Therefore, continuous research, development of advanced cybersecurity measures, and international cooperation are imperative to stay a step ahead of cyber criminals.
In conclusion, cyber crime poses a significant threat in the digital age, affecting all aspects of society. A comprehensive understanding of its forms, impacts, prevention strategies, and the associated legal and ethical considerations is crucial for individuals, businesses, and governments alike. As we move further into the digital era, the fight against cyber crime will undoubtedly remain a pressing issue.
That’s it! I hope the essay helped you.
If you’re looking for more, here are essays on other interesting topics:
- Essay on Christmas Celebration in School
- Essay on How I Spent My Christmas Vacation
- Essay on My Aim of Life to Become a Bank Manager
Apart from these, you can look at all the essays by clicking here .
Happy studying!
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.

25,000+ students realised their study abroad dream with us. Take the first step today
Meet top uk universities from the comfort of your home, here’s your new year gift, one app for all your, study abroad needs, start your journey, track your progress, grow with the community and so much more.

Verification Code
An OTP has been sent to your registered mobile no. Please verify

Thanks for your comment !
Our team will review it before it's shown to our readers.

- School Education /
✍️Essay on Cybercrime: Free Samples in 100, 200, 300 Words
- Updated on
- Nov 2, 2023
The 21st century is a digital age, where any and every task is done on the internet. All thanks to the developments in technology which have been the main factor to ease human life on earth and maybe on other plants in future. But with the benefits of technology, there are several harmful effects, one of them which has recently gained popularity; Cyber Crime.
Cybercrime has emerged as pervasive and evolved as one of the most dangerous threats to humans. There are several users on the internet who indulge in illegal and criminal activities, using computers and networks. To guide you through this hot debate topic, below we have discussed essays on cybercrime.
This Blog Includes:
Essay on cybercrime in 100 words, essay on cybercrime in 200 words, essay on cybercrime in 300 words.
Also Read: Essay on Student Life
Cybercrime involves illegal activities like hacking, ransomware, cyberbullying, online fraud, etc. People who are involved in cybercrime or any similar activities are called hackers, scammers or fraudsters. Cybercrime leads to financial loss for individuals who have fallen victim to one. Cybercrime often invades a person’s privacy by stealing their personal details, including sensitive data, photos, and communication records, which can be used for blackmailing or any malicious purpose.
There are several governmental and non-government organizations which are working
To tackle cybercrime by raising awareness among the masses, cyber security training, implementing robust security protocols, and enacting comprehensive cybercrime laws.
Cybercrime is a criminal activity done online using a computer, network and internet. With the increasing use of the internet and mobile phones, the number of criminal activities has also gained pace. These criminal-minded people steal the personal details of a person, which leads to financial losses and damages the reputation of the victims. Various scams and fraudulent schemes are offered on the internet like online auctions, advance fees, or any investment scam, which are all aimed at deceiving individuals into parting with their money.
Cybercrime is not limited to financial losses or reputational damage, a more discrete term has emerged; cyberbullying. In cyberbullying, a person is harassed, humiliated, or threatened online. This can have severe psychological and emotional consequences. Ethical hackers or white hat hackers can help organizations identify vulnerabilities in their systems before malicious hackers exploit them.
Cybercrime doesn’t have any boundaries and is an international issue and international cooperation is crucial for tracking and prosecuting cybercriminals who operate across borders. To combat cybercrime effectively, a multi-faceted approach is required, involving education, technology, legislation, and international cooperation. As technology continues to advance, our efforts to combat cybercrime must keep pace to protect our increasingly interconnected world.
Also Read – Essay on Winter Season
Economists have termed cybercrime as ‘ A Hidden Threat to the Digital World.’ Modern humans are relying on the internet for their day-to-day activities and every macro and micro activity. In this sense, the term cybercrime comes to the front. Cybercrime refers to criminal activities conducted through the use of computers, networks, and the Internet.
Cybercrime consists of various malicious activities like hacking, phishing, ransomware attacks, identity theft, online fraud, and cyberbullying. Hackers, fraudsters, scammers, criminals, and even state-sponsored actors exploit vulnerabilities in digital systems to steal sensitive information, disrupt operations, and cause financial and emotional harm to victims.
The consequences of cybercrime are far-reaching. Financial losses run into 10 digits annually, affecting individuals and organizations alike. Personal privacy is invaded as cybercriminals steal sensitive data, photos, and communication records. In cases of cyberbullying and harassment, victims suffer reputational damages, psychological distress, and emotional trauma, particularly in cases of cyberbullying and harassment.
It’s necessary to look for a multifaceted approach to deal with cybercrime, some of which are.
- Raising public awareness through campaigns where people are informed about the risks of cybercrime and educate them on best practices for online safety.
- Individuals and organizations should implement robust security protocols, regularly update software, and use multi-factor authentication to protect their digital assets.
- Governments should enact and enforce cybercrime laws, providing law enforcement agencies with the resources and expertise needed to prosecute cybercriminals effectively.
- Looking at the global nature of cybercrime, international collaboration is vital. Countries should work together to share threat intelligence and cooperate in the investigation and prosecution of cybercriminals.
- Ethical hackers can help organizations identify and rectify vulnerabilities in their systems before malicious actors exploit them.
Tackling cybercrime requires proactive measures, including education, strong cybersecurity practices, legislation, international cooperation, and the active involvement of ethical hackers.
Related Articles
Cybercrime is an illegal and unethical activity which is done by hackers and fraudsters to gain financial or any other benefits for themselves.
To tackle cybercrime, several measures can be taken. Some of these measures are education and public awareness, research and innovation, ethical hacking, etc.
To write an essay on cybercrime, you need to give details on how it works and the level of danger it poses to humans. Cybercrime consists of various malicious activities like hacking, phishing, ransomware attacks, identity theft, online fraud, and cyberbullying. Hackers, fraudsters, scammers, criminals, and even state-sponsored actors exploit vulnerabilities in digital systems to steal sensitive information, disrupt operations, and cause financial and emotional harm to victims.
For more information about such informative articles, visit our essay writing page and make sure to follow Leverage Edu .
Shiva Tyagi
With an experience of over a year, I've developed a passion for writing blogs on wide range of topics. I am mostly inspired from topics related to social and environmental fields, where you come up with a positive outcome.
Leave a Reply Cancel reply
Save my name, email, and website in this browser for the next time I comment.
Contact no. *

Connect With Us
25,000+ students realised their study abroad dream with us. Take the first step today.

Resend OTP in

Need help with?
Study abroad.
UK, Canada, US & More
IELTS, GRE, GMAT & More
Scholarship, Loans & Forex
Country Preference
New Zealand
Which English test are you planning to take?
Which academic test are you planning to take.
Not Sure yet
When are you planning to take the exam?
Already booked my exam slot
Within 2 Months
Want to learn about the test
Which Degree do you wish to pursue?
When do you want to start studying abroad.
January 2024
September 2024
What is your budget to study abroad?
How would you describe this article ?
Please rate this article
We would like to hear more.
Have something on your mind?

Make your study abroad dream a reality in January 2022 with
India's Biggest Virtual University Fair

Essex Direct Admission Day
Why attend .

Don't Miss Out
Home — Essay Samples — Law, Crime & Punishment — Cyber Crimes — Cyber Crime: The Meaning, Types, And Ways To Avoid
Cyber Crime: The Meaning, Types, and Ways to Avoid
- Categories: Cyber Crimes Cyber Security
About this sample

Words: 2343 |
12 min read
Published: May 17, 2022
Words: 2343 | Pages: 5 | 12 min read
Table of contents
Introduction, types of cyber crime.
- Phising/Spoofing: Unlawfully accessing a computer without authorization and sending multiple e-mails; resending multiple commercial email messages with the intent to deceive recipients; or falsifying header information in multiple email messages.
- Blackmail/Extortion: Using the Internet to threaten to cause damage with the intent to extort from any person any money or other thing of value.
- Accessing Stored Communications: Intentionally accessing, without authorization, a facility through which an electronic communication service is provided.
- Sports Betting: Engaging in the business of betting or wagering on any sporting event or contest over the Internet.
- Non-Delivery of Merchandise: Devising any scheme to defraud, or for obtaining money or property by means of false or fraudulent pretenses, or promises, and using the Internet for the purpose of executing the scheme.
- Electronic Harassment: Anonymously using the Internet to annoy, abuse, threaten, or harass the person who receives the communication.
- Child Pornography: Using the Internet to transmit child pornography.
- Prostitution: Persuading, inducing, enticing, or coercing any individual to travel in interstate commerce to engage in prostitution.
- Drug Trafficking: Delivering, distributing, or dispensing a controlled substance by means of the Internet.
- Criminal Copyright Infringement: Infringing a copyright for financial gain...or by distributing a work being prepared for commercial distribution on a computer network.
Avoiding Cyber Crime
Anti-virus software.
- It became common to distribute software and updates via downloads from the Internet,
- Hackers developed viruses that were delivered inside macros for Microsoft Word, which malicious macros could be hidden inside a document sent by e-mail, and
- Hackers developed malicious computer programs that were commonly distributed as attachments to e-mail: clicking on the attachment executed the malicious computer program and infected the victim's computer.
- Never open an executable attachment.
- Never open any attachment from an unknown source.
- Be cautious of any attachment that has a double file extension, especially when the rightmost file extension is an executable file type.

Avoiding harassment
- https://www.slideshare.net/bharadwajchetan/an-introduction-to-cyber-law-it-act-2000-india
- https://cybercrime.org.za/definition
- http://www.cyberlawsindia.net/cyber-india.html
- Dorothy E. Denning, Information Warfare and Security, Addison- Wesley Publishing Co., 1998.
- Dorothy E. Denning and Peter J. Denning, Internet Besieged, Addison- Wesley Publishing Co., 1997.
- Peter J. Denning (editor), Computers Under Attack, Addison- Wesley Publishing Co., 1990.
- Peter G. Neumann, Computer –Related Risks, Addison – Wesley Publishing Co., 1995.
Cite this Essay
Let us write you an essay from scratch
- 450+ experts on 30 subjects ready to help
- Custom essay delivered in as few as 3 hours
Get high-quality help

Verified writer
- Expert in: Law, Crime & Punishment Information Science and Technology

+ 120 experts online
By clicking “Check Writers’ Offers”, you agree to our terms of service and privacy policy . We’ll occasionally send you promo and account related email
No need to pay just yet!
Related Essays
6 pages / 2847 words
5 pages / 2098 words
5 pages / 2249 words
4 pages / 1863 words
Remember! This is just a sample.
You can get your custom paper by one of our expert writers.
121 writers online
Still can’t find what you need?
Browse our vast selection of original essay samples, each expertly formatted and styled
Related Essays on Cyber Crimes
In our increasingly interconnected world, where technology is deeply woven into the fabric of our daily lives, the specter of computer threats looms large. From malware attacks to hacking and data breaches, the digital landscape [...]
Lee, S. (2017). Encrypted Messaging: Keeping Your Conversations Secure. Security Boulevard.Smirnoff, V., & Turner, S. (2019). Symmetric Encryption: Definition, Types, and Examples. SecurityTrails.Almeida, R. (2019). Asymmetric [...]
Cybersecurity has become a very familiar term that has drawn increasing awareness of the danger of leaving cybercrimes unpunished. Because the world is moving more toward online trading and e-commerce, and basically living [...]
The research study provides a review and analysis about the various kinds of cyber crimes that are committed by the perpetrators who are always in search of vulnerable people who could be victimized. Women are said to be [...]
There are myriad ways for the bad guys to get your information and use it for all sorts of nefarious purposes — mainly, stealing your money, althoughoccasionally for other kinds of fraud or to cover their tracks when committing [...]
Mankiewicz’s All About Eve uses the theatre as a medium in which the female protagonists, Eve and Margo, are victimized at the hands of varying internal and external factors. The film clearly portrays Margo as a casualty of [...]
Related Topics
By clicking “Send”, you agree to our Terms of service and Privacy statement . We will occasionally send you account related emails.
Where do you want us to send this sample?
By clicking “Continue”, you agree to our terms of service and privacy policy.
Be careful. This essay is not unique
This essay was donated by a student and is likely to have been used and submitted before
Download this Sample
Free samples may contain mistakes and not unique parts
Sorry, we could not paraphrase this essay. Our professional writers can rewrite it and get you a unique paper.
Please check your inbox.
We can write you a custom essay that will follow your exact instructions and meet the deadlines. Let's fix your grades together!
Get Your Personalized Essay in 3 Hours or Less!
We use cookies to personalyze your web-site experience. By continuing we’ll assume you board with our cookie policy .
- Instructions Followed To The Letter
- Deadlines Met At Every Stage
- Unique And Plagiarism Free

Essay on Cyber Crime | 500+ Words
Cybercrime is like a shadow lurking in the digital world, ready to harm us. In this essay, we will explore the world of cybercrime, its types, consequences, and how we can protect ourselves in the digital age.
Defining Cybercrime:
Cybercrime involves illegal activities conducted online. These crimes can harm individuals, organizations, and even entire nations.
The Digital Revolution
The rise of technology has brought convenience but also vulnerabilities. Cybercriminals exploit these vulnerabilities for personal gain.
Types of Cybercrime
Cybercrime takes many forms, including hacking, identity theft, online scams, and cyberbullying. Each poses unique risks and challenges.
Hacking and Data Breaches
Hackers gain unauthorized access to computer systems, stealing valuable data. These breaches can lead to financial loss and privacy violations.
Identity Theft
Identity theft involves stealing personal information for fraudulent purposes. Victims can face financial ruin and emotional distress.
Online Scams
Scammers trick people into giving away money or personal information. Awareness and skepticism are key defenses against these scams.
Cyberbullying
Cyberbullying involves using the internet to harass or harm others. It can have devastating effects on mental and emotional well-being.
The Impact of Cybercrime
Cybercrime has far-reaching consequences, affecting individuals, businesses, and governments. It erodes trust and security in the digital world.
Financial Loss
Victims of cybercrime often suffer financial losses. Recovering stolen funds can be challenging, and the impact can be long-lasting.
Emotional Toll
The emotional toll of cybercrime can be severe. Victims may experience fear, anxiety, and a loss of trust in online interactions.
Expert Opinions on Cybercrime
Experts in cybersecurity emphasize the importance of vigilance, education, and strong security measures in protecting against cyber threats.
Cybersecurity Measures
Protecting against cybercrime requires cybersecurity measures like strong passwords, antivirus software, and regular software updates.
The Role of Education
Education about online safety is vital. Schools and organizations should teach digital literacy and cybersecurity from an early age.
Online Privacy
Protecting online privacy means being cautious about sharing personal information and understanding the importance of data protection laws.
Reporting Cybercrime
Reporting cybercrime to law enforcement is crucial. It helps track down cybercriminals and prevent further harm.
International Cooperation
Cybercrime is a global issue. International cooperation and laws are essential to combating it effectively.
The Future of Cybersecurity
As technology evolves, so do cyber threats. Ongoing research and innovation in cybersecurity are essential to staying ahead of cybercriminals.
Conclusion of Essay on Cyber Crime
In conclusion, cybercrime is a digital menace that affects us all. Whether it’s hacking, scams, or cyberbullying, the consequences can be devastating. However, we can protect ourselves by staying informed, practicing good cybersecurity habits, and reporting cybercrime when it occurs.
The digital age has brought us incredible opportunities, but it has also brought risks. It is our responsibility to navigate this digital world with caution and vigilance. By doing so, we can reduce the impact of cybercrime and make the internet a safer place for everyone. Cybersecurity is not just a personal responsibility; it’s a collective effort to keep our digital world secure and trustworthy.
Also Check: The Essay on Essay: All you need to know
140 Interesting Cybercrime Research Topics To Focus On
Table of Contents
Do you have to submit a cybercrime research paper? Are you looking for the best cybercrime research topics for your law assignments? Well, to help you out, here, we have compiled a list of interesting essays and research topic ideas on cybercrimes. Continue reading this blog post and gain unique ideas for writing a cybercrime research paper or an essay.
What is a Cybercrime?
Cybercrime is a criminal activity that is committed using a computer, a network, or a networked device. In recent times, the internet plays a vital role in the daily life of an individual. Particularly, a lot of financial transactions and data sharing are happening over the internet. So, considering that many cybercrimes are being carried out by cybercriminals for generating a profit. Basically, cybercrimes are of three categories.
- Crimes in which the computer is used as a weapon. E.g., launching a denial-of-service (DoS) attack, or malware attack.
- Crimes in which a computer or networked device is a target. E.g., gaining network access.
- Crimes in which a computer is used as an accessory to a crime. E.g., data theft, cyberstalking.
Under the above-mentioned categories, different types of cybercrimes are being carried out by cybercriminals. Cybercrimes include both monetary and non-monetary offenses. Mostly, cybercrimes result in damage to an individual, a device, or a government.
List of Cybercrimes
In the entire world, plenty of cybercrimes are happening. The masterminds behind all those dangerous crimes are the hackers with strong hacking and technical knowledge. Mainly, cybercrimes are carried out at locations where there is digital data.

Here is a list of some widely carried out cybercrimes across the world.
- Cyber Bullying
- Cyber Grooming
- Child Pornography
- Cyber Stalking
- Online Job Fraud
- Online Sextortion
- SIM Swap Scam
- Credit Card/Debit Card Fraud
- Impersonation/Identity Theft
- Viruses, Trojans, and Worms
- Online Drug Trafficking
- Data Breach
- Cryptojacking
- Cyber-Squatting
- Website Defacement
In order to prevent cybercrimes and reduce the risk of cyberattacks, cyber security is practiced. Also, to handle all the cybercrimes, each country has a separate cybercrime department and they follow strict cyber laws.
Cybercrime Research Topics and Ideas
Nowadays, a lot of questions are being raised about cybercrimes. To get answers for them all, conducting research is the only option. In case, you are asked to craft a cybercrime research paper on the topic of your preference, consider any topic related to common cybercrime cases such as personal data theft, financial theft, cyber-extortion, drug trafficking, and terrorism.

Are you a law student who has a keen interest to analyze and study cybercrimes? If yes, then the list of the best cybercrime research topics recommended below will be helpful to you. Without any hesitation, explore the full list and select any topic that is comfortable for you to analyze and write about.
Best Cybercrime Research Topics
- What is the role of America in protecting corporations from cybercrime?
- Have a close look at cybercrime, cyber forensics, and digital evidence.
- Is cybercrime the top IT threat?
- Write about the necessity of cyber security in preventing cybercrimes.
- Discuss the international laws and regulations related to cybercrime.
- Explain the effects of the UAE Cybercrime policy.
- What are the toolkits used in cybercrimes?
- Discuss the cybercrimes in Singapore.
- Write about UAE cybercrime laws.
- Explain the impact of cybercrime on the global criminal justice system.
- Have a detailed look at international cyberwar.
- Talk about Cybercrimes in the US.
- Discuss identity theft and cybercrime in contemporary society.
- Explain the significance of digital education and creating awareness of cybercrime.
- What are the effects of cybercrime on the world’s major countries?
- Explain UAE cybercrime laws.
- What is the need for cyber security in preventing cybercrimes?
- Discuss the role of America in protecting corporations from cybercrime.
- Importance of raising cybercrime awareness and digital education
- Analyze some recent cases of cybercrime in the banking industry and its consequences
- Discuss the impact of IP (intellectual property) rights, cyber piracy, and cybercrime on domestic and international business with the latest examples
- Critically analyze the degree and frequency of cybercrime in the United States
- Analyse the Cybercrime Legislation Amendment Act 2012(Cth) (CLAA)
- Compare and contrast the cybercrime prevention laws in India and the United Kingdom
- Analyze the Cybersecurity Laws and Regulations Report 2023 USA
- What are the key measures to undertake by a company to protect the cloud computing environment from cybersecurity issues?
- Identify and analyze the components of broadband industry structure and cybercrime
- Discuss the relationship between cybercrime, the economy, privacy, hacking, and terrorism
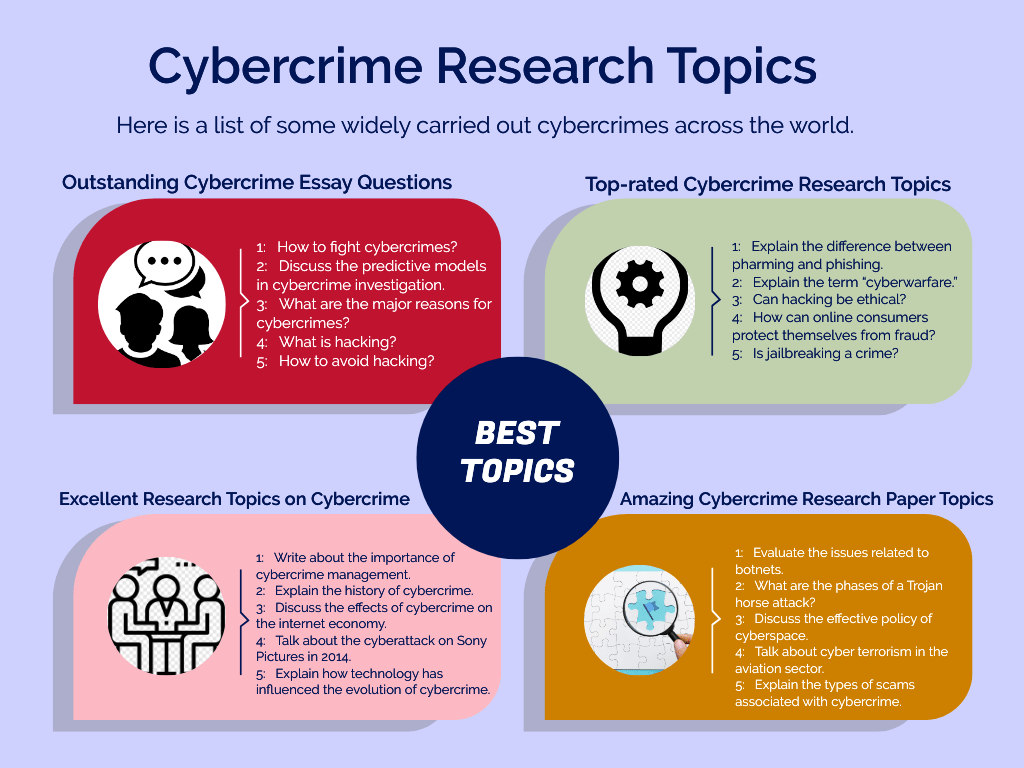
Good Cybercrime Essay Topics
- What are all the effects of cybercrime on the world’s major countries?
- Discuss the cybercrimes in the healthcare industry.
- Explain the developments in hacking.
- Discuss the trends of the future of good cybercrime.
- Write about Cybercrimes in Australia.
- What are the impacts of cybercrime on the banking industry?
- Is identity theft a cybercrime?
- Should capital punishment be given for cybercrime?
- Discuss the solutions for cybercrimes in Information Technology.
- Talk about cybercrime and social media.
- Explain the cybercrime challenges in public universities.
- Have a closer look at business fraud and cybercrime.
- Write about cybercrimes in India.
- Discuss terrorist cyberattacks with an example.
- Explain the impact of cybercrime on a government.
- Discuss the five biggest cyber security trends in 2022
- Remote working risks of cybersecurity
- Importance of Password-only Authentication in restricting cybercrime
- The Rise of Ransomware: Discuss
Unique Cybercrime Research Topics
- How to explain cybercrime using criminological theories ?
- How does crypto jacking work?
- Track the evolution of online scams.
- Analyze the implications of the Cyberpunk 2077 leak.
- How do cybercrimes afflict retail shops?
- What are man-in-the-middle attacks?
- What are the various phases of a DDoS attack?
- How to mitigate a denial-of-service attack?
- Analyze the success rate of email scams.
- Describe the working of WannaCry malware.
- Describe what happens during a Brute Force attack.
- How does ransomware work?
- How to protect children from cyberbullying?
- Have a closer look at big data and increased cybercrimes.
- Compare various types of fraud methods.
- What are identity theft and cybercrime in contemporary society
- Discuss the statistics on cybercrime as well as Fraud
Outstanding Cybercrime Essay Questions
- How to fight cybercrimes?
- Discuss the predictive models in cybercrime investigation.
- What are the major reasons for cybercrimes?
- What is hacking?
- How to avoid hacking?
- Whose responsibility is cybercrime?
- Discuss the cost of cybercrime and digital spying.
- How does cybercrime affect domestic and foreign business?
- How to investigate cybercrime?
- Discuss the link between fraud and invisible attackers.
Top-rated Cybercrime Research Topics
- Explain the difference between pharming and phishing.
- Explain the term “cyberwarfare.”
- Can hacking be ethical?
- How can online consumers protect themselves from fraud?
- Is jailbreaking a crime?
- How can parents monitor their children’s behavior on the web?
- How to prevent cyberbullying in the online learning environment?
- Would cyber communism decrease bullying?
- Discuss the connection between political protests and hacking.
- Talk about the mental health effects of internet bullying.
- Who is responsible for online misbehavior?
- Who are white hat and black hat hackers?
- Explain the effects and solutions of catfishing.
- Should schools teach online etiquette?
- Does internet anonymity bring out the worst in people?
- How to stay safe online?
- How does a firewall help to protect the network?
- Explain how cyberbullying differs from in-person harassment.
- How to cope with online harassment?
- Write about phishing and scam on the internet.
Also read: Best Cybersecurity Research Topics for Students to Consider
Excellent Research Topics on Cybercrime
- Write about the importance of cybercrime management.
- Explain the history of cybercrime.
- Discuss the effects of cybercrime on the Internet economy.
- Talk about the cyberattack on Sony Pictures in 2014.
- Explain how technology has influenced the evolution of cybercrime.
- Discuss the social effects of cyberbullying on children.
- What are the signs of phishing attempts?
- What emergency action should an individual take after being hacked?
- Research and explain the significant cyber threats to US national security.
- Different types of cybercriminals.
- How do private sectors battle cybercrimes?
- Discuss the impacts of mobile devices on cyber security.
- Take a closer look at cyberfeminism and social media.
- Compare the functions of various antivirus programs.
- Discuss the pros and cons of various InfoSec certificates.
Amazing Cybercrime Research Paper Topics
- Evaluate the issues related to botnets.
- What are the phases of a Trojan horse attack?
- Discuss the effective policy of cyberspace.
- Talk about cyber terrorism in the aviation sector.
- Explain the types of scams associated with cybercrime.
- Discuss the potential effects the cyber currencies have on South African Businesses.
- How the automotive software of smart cars can be protected from cyberattacks?
- Discuss the effects of cyberbullying on teen suicides.
- Have a closer look at the cyber policy and strategy of the United Kingdom.
- What are the dangers of public Wi-Fi networks?
High-quality Cybercrime Research Ideas
- Describe the technology of unlocking a phone through facial recognition and the fingerprint of the owner of the phone
- Select a company from the United States and discuss their efforts and strategies to ensure cyber security
- Discuss the reasons that make every individual aware when it comes to safeguarding and protecting personal data and information from hackers
- Face recognition vs. a simple security code vs. fingerprint: Which is the safest locking option for smart devices and why?
- The increasing use of the internet consecutively increases the likelihood of adolescents and young adults engaging in cybercrime-related activities (e.g., email and internet fraud, identify fraud)
- Compare and contrast the effects of Phishing Emails, DoS (Denial of Service) Attacks, and Social Engineering
- Describe the history of cybercrime and the way cybercriminals have introduced different strategies to commit such crimes over the past decades
- Discuss the similarities and differences between distributed denial-of-service (DDoS) attacks and DoS (Denial of service) attacks
- Examination of the consequences a community or society would have to bear in case a hacker targeted the entire state
- Is purchasing from e-commerce sites such as eBay, Amazon, and Craigslist more ethical and safe compared to buying from other online marketplaces? Explain with reasons and the cyber security strategies of the aforementioned sites.
Impressive Cybercrime Research Topics
- Explain the importance of parental control mechanisms on children’s computers.
- What are effective strategies to cope with online harassment?
- Establish a link between feminism and the fight against cyberstalking.
- Analyze online gaming behavior from a psychological standpoint.
- How did industrial espionage evolve into hacking?
- Describe how an SQL injection attack unfolds.
- What are the safest ways to ensure data integrity?
- Discuss the pros and Cons of various cryptographic methods.
- How can a person reach maximum technological security?
- Explain the mechanics of password protection.
Final Words
From the list of ideas suggested above, choose any topic that matches your requirements and craft a detailed cybercrime research paper with proper citations and proofs to prove your thesis statement. In case, you need an expert to offer you help with cybercrime research paper topic selection and writing, get in touch with us immediately. We have numerous professional writers who are experts in the field of law and cybercrime to provide assignment help online according to your needs.
If you wish to make use of our cybercrime research paper writing service, just write your requirements in the order form and submit it. Based on the specifications you send us, our cybercrime research paper helpers will craft and dispatch a well-structured and plagiarism-free academic paper on time. Also, you can opt for endless paper revisions and round-the-clock customer support by availing of our assignment writing services.

Related Post

220 Amazing Religious Research Paper Topics and Ideas

Read and Understand How to Write a Research Proposal

100+ Controversial Research Topics and Ideas to Focus On
About author.
Jacob Smith
I am an Academic Writer and have affection to share my knowledge through posts’. I do not feel tiredness while research and analyzing the things. Sometime, I write down hundred of research topics as per the students requirements. I want to share solution oriented content to the students.
Comments are closed.
- Featured Posts
140 Unique Geology Research Topics to Focus On
200+ outstanding world history topics and ideas 2023, 190 excellent ap research topics and ideas, 150+ trending group discussion topics and ideas, 170 funny speech topics to blow the minds of audience, who invented exams learn the history of examination, how to focus on reading 15 effective tips for better concentration, what is a rhetorical analysis essay and how to write it, primary school teacher in australia- eligibility, job role, career options, and salary, 4 steps to build a flawless business letter format, get help instantly.
Raise Your Grades with Assignment Help Pro

Essay on Cyber Crime
In the digital age, the rapid advancement of technology has reshaped the way we live, work, and interact. However, alongside the countless benefits, this evolution has given rise to a darker phenomenon known as cyber crime. Cyber crime encompasses a wide range of malicious activities carried out through digital means, affecting individuals, organizations, and even nations. This essay delves into the intricacies of cyber crime, exploring its types, causes, impacts, and measures to combat it, offering a comprehensive overview for students participating in essay writing competitions.
Cyber Crime
Cyber crime refers to any criminal activity that involves a computer, networked device, or a network. While most cyber crimes are carried out to generate profit for the criminals, some are done to harm or intimidate individuals, governments, or entire societies. The anonymity, vast reach, and speed of the internet have made cyber crime a highly effective and dangerous tool in the hands of criminals.
Types of Cyber Crime
Cyber crime can be broadly categorized into three types: crimes against individuals, crimes against property, and crimes against governments or society at large.
- Phishing: Phishing involves sending fraudulent emails or messages that appear to be from legitimate sources to deceive individuals into revealing sensitive information, such as passwords, credit card numbers, or personal details.
- Ransomware: Ransomware is a type of malware that encrypts a victim’s files or data, rendering them inaccessible. The attacker demands a ransom payment from the victim to provide the decryption key.
- Malware: Malware (malicious software) includes viruses, Trojans, worms, and spyware designed to infect and compromise computer systems, steal data, or disrupt operations.
- Identity Theft: Cybercriminals steal personal information, such as Social Security numbers or financial data, to impersonate victims for financial gain, fraudulent activities, or accessing accounts.
- Cyberbullying: Cyberbullying involves using digital platforms, such as social media or messaging apps, to harass, threaten, or intimidate individuals, often leading to emotional and psychological distress.
- Online Scams: Various online scams deceive individuals into parting with their money, including advance-fee fraud, lottery scams, and romance scams. These scams exploit trust and gullibility.
- Data Breaches: Data breaches occur when cybercriminals gain unauthorized access to databases or systems, exposing sensitive information, such as customer data, financial records, or trade secrets.
- Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks: These attacks overwhelm a target system, website, or network with excessive traffic, rendering it unavailable to legitimate users.
- Cyber Espionage: State-sponsored or corporate espionage involves infiltrating computer systems to steal sensitive information, trade secrets, or government intelligence.
- Child Exploitation: Child exploitation includes online activities like child pornography, grooming, or sextortion, targeting minors and causing severe harm to victims.
- Hacking and Unauthorized Access: Unauthorized access to computer systems, networks, or accounts for the purpose of data theft, vandalism, or disruption is considered hacking.
- Financial Cybercrimes: Financial cybercrimes involve fraud, embezzlement, or theft of funds through various digital means, such as credit card fraud, online banking fraud, or investment scams.
- Online Harassment and Stalking: Cybercriminals engage in online harassment, stalking, or doxxing (publishing private information) to harass and intimidate victims.
- Social Engineering: Social engineering techniques manipulate individuals into divulging confidential information or performing actions that compromise security, often through impersonation or pretexting.
- Botnets and Cyber Attacks: Cybercriminals create botnets, networks of compromised devices, to launch coordinated cyberattacks, such as spam distribution, information theft, or credential stuffing attacks.
- Cryptojacking: Cryptojacking involves using a victim’s computer or device to mine cryptocurrencies without their consent or knowledge, causing system slowdowns and increased energy consumption.
- Online Copyright Infringement: Copyright infringement on the internet involves illegally sharing or distributing copyrighted content, such as movies, music, or software, without authorization.
- Deepfake and Manipulated Media: Deepfake technology creates convincing but fabricated audio, video, or text content, leading to misinformation, impersonation, and reputational harm.
Causes of Cyber Crime
Several factors contribute to the prevalence of cyber crime, including:
- Anonymity: The internet provides a level of anonymity that emboldens criminals, making it challenging to trace illegal activities back to the perpetrators.
- Global Reach: Cyber criminals can operate from any location, targeting victims worldwide without ever crossing physical borders.
- Technological Complexity: The complexity and rapid evolution of technology can outpace security measures, leaving vulnerabilities that can be exploited.
- Lack of Awareness: Many users are unaware of the risks associated with their online activities, making them easy targets for cyber criminals.
Impacts of Cyber Crime
The effects of cyber crime are vast and varied, affecting individuals, organizations, and nations.
- Financial Loss: Cyber crime costs the global economy billions of dollars annually through fraud, theft of intellectual property, and other financial crimes.
- Psychological Impact: Victims of cyber crime, such as cyberbullying or identity theft, can experience significant emotional distress.
- Reputation Damage: Businesses and governments can suffer reputational damage due to data breaches, undermining public trust.
- National Security Threats: Cyber attacks on critical infrastructure can pose significant threats to national security, potentially leading to chaos and crisis.
Combating Cyber Crime
Addressing the challenge of cyber crime requires a multi-faceted approach, involving individuals, businesses, governments, and international bodies.
- Legislation: Implementing comprehensive cyber crime laws and regulations is crucial to defining and deterring illegal online activities.
- Cybersecurity Measures: Individuals and organizations must adopt robust cybersecurity practices, including the use of firewalls, antivirus software, and strong passwords.
- Education and Awareness: Raising awareness about the risks of cyber crime and promoting safe online behaviors can significantly reduce vulnerability.
- International Cooperation: Cyber crime is a global issue that necessitates international collaboration to develop strategies for prevention, investigation, and prosecution.
Future Directions
As technology continues to evolve, so too will the nature of cyber crime. The rise of artificial intelligence, the Internet of Things (IoT), and other emerging technologies will introduce new vulnerabilities and challenges. Future efforts to combat cyber crime must focus on advancing cybersecurity technologies, enhancing international legal frameworks, and fostering a culture of security awareness among all internet users.
In conclusion, Cyber crime is a pervasive issue that poses significant challenges to the security, privacy, and well-being of individuals and societies worldwide. Understanding the complexities of cyber crime is the first step toward developing effective strategies to combat it. By fostering collaboration among various stakeholders and embracing a proactive approach to cybersecurity, we can hope to mitigate the risks associated with our increasingly connected world. For students aspiring to make a difference, participating in essay writing competitions on topics such as cyber crime not only raises awareness but also encourages the development of innovative solutions to safeguard our digital future.

Essay Generator
Text prompt
- Instructive
- Professional
Generate an essay on the importance of extracurricular activities for student development
Write an essay discussing the role of technology in modern education.
50 Latest Cyber crime IELTS Topics
- Unlimited Essay Checks: Practice and perfect your skills.
- Detailed Error Analysis: Spot every mistake.
- In-Built Grammar Checker: Say no to grammatical errors.
- Personalized Suggestions: Know how to boost your score.
- Progress Tracking: View your checked essay history.
- Still thinking? We have a 14-day money-back guarantee. Take a leap of faith!
We use cookies to enhance our website for you. Proceed if you agree to this policy or learn more about it.
- Essay Database >
- Essays Examples >
- Essay Topics
Essays on Cyber Crime
10 samples on this topic
Writing lots of Cyber Crime papers is an essential part of contemporary studying, be it in high-school, college, or university. If you can do that unassisted, that's just awesome; yet, other learners might not be that lucky, as Cyber Crime writing can be quite challenging. The collection of free sample Cyber Crime papers exhibited below was set up in order to help embattled learners rise up to the challenge.
On the one hand, Cyber Crime essays we present here precisely demonstrate how a really well-written academic paper should be developed. On the other hand, upon your request and for a reasonable price, a professional essay helper with the relevant academic background can put together a top-notch paper model on Cyber Crime from scratch.
Criminal Justice: A Global Perspective Assessment Research Paper Samples
Introduction
Perfect Model Critical Thinking On Risk Assessment And Countermeasures
Expertly written essay on mars, inc. to follow.
Information technology is an essential tool for the development of an organization. Technology assists companies in their operation. The use of technology is especially crucial in the management of global organizations. The technological advances assist these organizations to avoid crimes and errors committed through technology. Mars Inc. is one of the companies that have embraced technology in their operations. This paper is set to research on Mars Inc. and its operations in the global market. Additionally, it analyzes the technological advancements employed by the organization in its operations.
The History of Mars Inc
Proper Essay Example About Differences Between Categories Of Crime
Crimes against Persons
Crimes against persons are those criminal conducts punishable under penal law and which are mainly committed against individuals as the victims (Gardner & Anderson, 2014, p.25). In such categories of crimes, the perpetrator or offender normally has the intention to cause the victim actual grievous bodily injury and harm. Examples of crimes under this category include rape, assault and murder.
Crimes against Property
Learn To Craft Essays On Mitigation Of Cyber Attacks With This Example
Mitigation of cyber attacks
Free Digital Computer Crimes Essay Example
The history and importance of cyber security essay examples.
The History and importance of cyber security
Example Of Cyber Law Research Paper
(Institution Name)
275 words = 1 page double-spaced

Password recovery email has been sent to [email protected]
Use your new password to log in
You are not register!
By clicking Register, you agree to our Terms of Service and that you have read our Privacy Policy .
Now you can download documents directly to your device!
Check your email! An email with your password has already been sent to you! Now you can download documents directly to your device.
or Use the QR code to Save this Paper to Your Phone
The sample is NOT original!
Short on a deadline?
Don't waste time. Get help with 11% off using code - GETWOWED
No, thanks! I'm fine with missing my deadline

Essay on Cyber Crime
Cyber crime is the result of technological advancements. It is a dangerous crime involving the use of internet and computers. Cybercrime is undetectable at the initial phase but comes to notice with the consequences. Through this, the illegal transfer of data and information is made, which is of confidential value to an individual or a group.
Short and Long Essays on Cyber Crime in English
Essay on Cyber Crime for students of class 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11 and class 12 in English in 100, 150, 200, 250, 300, 500 words. Also find short Cyber Crime essay 10 lines.
Cyber Crime Essay 10 Lines (100 – 150 Words)
1) The crime done with the help of a computer network is termed as cybercrime.
2) Cybercrime can harm your privacy and security.
3) Cybercrime is an illegal act that tends to hack your private data.
4) Cybercriminals try to gain money through illegal methods.
5) Phishing, DoS attack, spoofing, etc are some common cybercrimes.
6) With the increasing use of the internet, cybercrimes are on the rise.
7) Cybercrime makes the victim helpless by stealing their money and credentials.
8) One should be conscious while using the internet.
9) Cybercrimes can affect a person, an organization, or even the government.
10) Cybercrime is the misuse of advanced technologies.
Essay 1 (250 Words) – Cyber Crime: A Threat to Society
Introduction
Crime is a word used for wrong deed or offence, but when it comes to cybercrime then, it can be defined as a crime done by internet to cause an immeasurable loss to the individual, organization, or the government. Cyber crime is a punishable offence committed by cyber criminals .
Cyber Crime – A Threat to Society
Cyber crime is the criminal act which takes place over the internet through computers as tools or targets or other smart devices meant for making our work easier. The hacker or criminals are having various motives of the crime. They may be involved to cause a loss to an individual, some organization or government.
Several examples of cyber crime include frauds, identity theft, cyberstalking, creating and sending malware like viruses for destroying the systems or steal the data to make money. People involved in such activities find them as an easy way of making money. Even many of the well-educated and knowledge full persons are involved in such activities. Instead of using their mind in a positive way they employ themselves in cyber crime activities. Day by day this is becoming a great threat to our society and nation.
Cybercrime is the most prevailing crime in the present scenario, done through the internet. It causes a severe loss to the victim. Therefore some of the measures should be taken by us to avoid such crimes. The vigilant behaviour and following the safety protocols are only helping aids which can reduce the occurrence of cybercrime.
Essay 2 (400 Words) – Cyber Crime: Classification and Impacts
Man has been innovative and inventive by nature, since early ages. The different needs gave rise to new devices, tools, and technologies. Technology is also a discovery of man for making work easier. The advancement in technology is useful on one side and on the other side has some devastating effects. Cybercrime is also a negative aspect of these technological developments. The individual, organization and groups are involved in committing such criminal activities.
Classification of Cyber Crimes
- Crime Against an Individual – Crime committed against an individual by use of an individual’s credit card details, confidential data and sending of spam emails. This crime is mainly done for making money.
- Crime Against an Organization – This is done against a firm, company or organization to get unauthorized access to the data. This is done either to reveal the important data and employee details of the company or for money-making.
- Crime Against Government – This is the crime against the nation, by getting access to the national data and records. This crime is of main concern as it concerned with the safety of the people of the nation.
Impacts of Cyber Crime
Cyber crime has ruined up the lives of many. The people involved in cyber crime are called hackers.
- If we discuss on an individual level, the people affected with this are still trying to adjust the loss. Some have opted to commit suicide. The ultimate loss of money and any data which is confidential make the person helpless and left out in a painful situation.
- On an organization level, the loss is made by stealing the data of the company or destroying the system by malware so that it may not work till the terms and conditions of the criminal get fulfilled. The companies are at a greater loss as their strategies and important data is stolen and leaked out.
- The government is also the victim of this offence. Much confidential data is leaked as the result of cyber crime at the government level, risking the nation’s sovereignty. This is a serious issue as it may happen that the lives of people of the nation are threatened and frightened. The loss can be economical too. Many lakh and crore have been lost from the nation because of these cyber crimes.
Cyber crime is an offence related to the use of the internet. It is dealt with some important information to be leaked in public or money-making in an easy way. Therefore we should be practicing some safety measures and security applications to prevent the crime.
Essay 3 (500 – 600 Words) – Cyber Crime
Cybercrime can be mentioned as illicit use of the internet and computers. The computers are either the target of the crimes or used as a weapon for the crime. These crimes have become a common part of our daily lives. Each and every day one or the other person is becoming the victim of cybercrime. Internet is accessed by a number of people at the same time for various purposes, these hackers make their way out of these opportunities.
Different Types of Cyber Crimes
- Phishing – This involves obtaining the personal information of the user by sending spam emails or by means of phishing website which resembles the same as authorized website.
- Identity Theft – This involves getting the information about credit or debit cards or bank details, further unwanted money can be easily deducted after the information is hacked.
- Malware Attacks – Malware is the hostile software which is designed to damage the computer or systems. This is done to access meaningful information or for doing some crime by using that system.
- ATM Frauds – The ATM machine is totally hacked in this crime. The criminals have developed the way to access both the data on the card along with the pin, further they are successful in making the duplicate of the cards and use the same to withdraw money.
- Cyber Stalking – The criminal is involved in following the person through online measures. They can even send malware to damage the systems to get the exact information. It involves harassment of the user.
- Pornography – The act of presenting sexual activity containing video, through pornographic websites.
- Spoofing – In this, an email is received and appears to be from some authentic source, but it is not the same. It is corrupted.
- Piracy – It is unauthorized access to the information which is confidential. Many of the times the government websites are hacked and files are pirated containing important data.
The First National Conference on National Crime Investigation and Crime Forensics
- Our nation India, for the first time had a national conference on national crime investigation held in New Delhi at headquarters of CBI (Central Bureau of Investigation) on 4 and 5 September 2019.
- The main motive of the conference was to create a common platform for the investigators, forensic teams and other officials involved to discuss various methods and ways to tackle the cyber-related crimes. The conference was of 2 days i.e. 4th and 5th September.
Cyber Crime Awareness
Different security measures should be followed to be safe from the dreadful act of cyber crime.
- Strong passwords should be used. The password must be a complex one, could not be possible to guess.
- Use antivirus programmes to keep the system free of malware.
- Continuously update the system.
- Be vigilant and use the presence of mind to avoid identity thefts.
- Make your children aware of the internet, so that they can state any misuse or harassment if they are going through.
- Maintain privacy settings over social media.
Cyber Security
Cyber security is saving our system, network, devices, and programmes from the attack of malicious software. Thus the illegal accessing of data can be stopped.
Importance – The information regarding any important issue of the nation or any data which is meant to be used personally, if gets shared will create several problems. Therefore if there will be a security check imposed at several levels, the information and important data can be saved from leaking.
Types of Cyber Security
- Network Security – Protects the network from being attacked by malware and thus using a secure network .
- Cloud security – Meant for safeguarding the data in the cloud resources .
- Information security – Helps in protecting the data from unauthorized or illegal access.
- End-user security – The user should be conscious of while inserting any external devices in the system, opening any mail or links.
- Application security – helps in keeping the system and software free of any threat .
Cyber crime is spreading its arms day by day. The most appropriate way of being safe from becoming the victim of its ill effects is following security measures. There are various ways by which we can protect our confidential information from being leaked. We should always focus on awareness as – ‘Prevention is better than cure’, especially when the cure is not available.
FAQs: Frequently Asked Questions
Ans . Cybercrime started in the world in the 1970s.
Ans . Ian Murphy was the first cybercriminal in the world.
Ans . Karuppannan Jaishankar is regarded as the father of Cyber criminology.
Ans . The Yahoo v. Akash Arora case was the first cybercrime case in India that happened in 1999.
Ans . The United States of America has the highest number of cybercrimes in the world.
Related Posts
Essay on digital india, cashless india essay, essay on child is father of the man, essay on causes, effects and prevention of corona virus, essay on dr. sarvepalli radhakrishnan, durga puja essay, essay on summer vacation, essay on my plans for summer vacation, essay on holiday, leave a comment cancel reply.
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.
- How it works
Useful Links
How much will your dissertation cost?
Have an expert academic write your dissertation paper!
Dissertation Services
Get unlimited topic ideas and a dissertation plan for just £45.00
Order topics and plan
Get 1 free topic in your area of study with aim and justification
Yes I want the free topic
5 Dissertation Topics on Cyber Crime
Published by Owen Ingram at January 9th, 2023 , Revised On August 15, 2023
Introduction
Any crime that is conducted using a computer and a network is known as cybercrime. Cybercrimes can target individuals in their personal capacity by targeting their property, the person himself, harming their mental health, and can even cause damage to governments.
Everyone using a computer and the internet can fall victim to cybercrime; however, understanding these crimes’ nature and how these are conducted can help people keep themselves safe and avoid falling victim.
Networks have weak spots, thus identifying those that can help you in determining possible attack points. This will eventually enable you to keep yourself safe from cybercrimes. Keeping your personal information safe at all times is critically important.
Never give out your passwords or any other personal information openly on any forum. This is one of the most effective ways of avoiding falling victim to cybercrime.
Being a pressing issue, cybercrime is continuously explored as to how it is conducted, what its types are, how it can be detected, how people can stay safe, etc. Here are five dissertation topics on cybercrime that will help gain an in-depth understanding of the issue.
These topics have been developed by PhD-qualified writers of our team , so you can trust to use these topics for drafting your dissertation.
You may also want to start your dissertation by requesting a brief research proposal from our writers on any of these topics, which includes an introduction to the topic, research question , aim and objectives , literature review along with the proposed methodology of research to be conducted. Let us know if you need any help in getting started.
Check our dissertation examples to get an idea of how to structure your dissertation .
Review the full list of dissertation topics for 2022 here.
5 Dissertation Topics on Cyber Crime 2022
Topic 1: is cybercrime a threat to banking sector in developing countries a case study of banking sector in pakistan.
Research Aim: This study aims to analyze the impact of cybercrime on the banking sector in developing countries. It will identify the possible threats faced by the banking sector due to increasing cybercrimes. These threats are related to the information security of the banks in developing countries. This research will be using Pakistan as a case study to find the threats posed by cybercrime to fragile banking. And after identifying the threats, the study will try to recommend possible solutions to ensure information security.
Topic 2: Impact of Cybercrime on E-Governance. Is cybercrime affecting the Confidentiality of Government Data?
Research Aim: This research aims to find the impact of cybercrime on modern-day governance systems or e-governance. It will identify the possible hindrances caused by cybercrime in implementing effective e-governance. This research will also investigate the impact of cybercrime on the confidentiality of government data. And after investigating the impact of cybercrime on the confidentiality of government data, this research will recommend the modern-day practices used to maintain the security of the information.
Topic 3: Is Information Safe Today? A survey to find the impact of cybercrime on the information security of the businesses
Research Aim: This study aims to find the impact of cybercrime on the information security of modern-day businesses. It will be a survey-based study to find out the problems faced by modern-day businesses due to cybercrime. These problems include confidential information leakage, which can benefit the competitors in the market. And another major problem is data stealing. This study will identify all these problems. And it will also recommend modern-day solutions to increase the security of the information.
Topic 4: A Socio-Technological Examination of Cybercrime and Information Security in Nigeria
Research Aim: This current research intends to determine Nigerian society’s vulnerabilities to cybercrime and exploitation and the global information infrastructure in general. It also aims to determine the informal, social, and technical drivers of Nigerian cybercrime and cybersecurity. To examine Nigerian law enforcement agencies and cybersecurity stakeholders’ efforts to combat cybercrime and guarantee cybersecurity. This analysis provides an opportunity for legislators, policymakers, and law enforcement agencies can utilize the law to establish legally valid definitions of cybercrime and information security from sociological and technological points of view
Topic 5: Impact of Cyber laws on Information Security. A Cross-Country Analysis
Research Aim: This study aims to analyse the impact of cyber laws on information security. This study is a cross-country analysis that will find the effectiveness of cyber laws across countries. It will see how over time, the introduction of cyber laws has affected information security after the find out the relationship between cyber laws and information security. This research will identify the most effective cyber laws in the countries under study. And after identifying the best laws among the countries under study. This study will recommend the best laws from individual countries or a set of laws from different countries.
Covid-19 Cyber Crime Research Topics
Topic 1: cybercrimes and coronavirus pandemic.
Research Aim: This study will focus on the increased cybercrimes during the coronavirus pandemic and the effective ways to overcome them.
Topic 2: Cybersecurity and COVID-19
Research Aim: This study will focus on the role of cybersecurity in minimizing cybercrimes during the crisis of the pandemic.
Topic 3: Cyber threats can harm industries
Research Aim: This study will address the growing cyber threats during COVID-19, where remote work has been adopted to combat the pandemic. It’ll highlight the threats, their harmful effect, and their solution.
Cyber Crime Research Topics 2021
Topic 1: importance of password security.
Research Aim: This research aims to identify the importance of Password security in safe computing.
Topic 2: Phishing scams
Research Aim: This research aims to highlight phishing scams issues and suggest various tips to avoid such scams.
Topic 3: Mobile protection
Research Aim: This research aims to highlight mobile security threats and suggest possible ways to protect mobile phones from hackers.
Topic 4: How to ensure safe computing?
Research Aim: This research will focus on types of hackings, scams and suggests possible ways to ensure safe computing
Topic 5: Cybercrime Dissertation Topics – The Evolution of Cyber Crime and the Attacks that Led to the Formation of Cyber Crime Policies
Research Aim: This dissertation will focus on the history of how this crime came into existence. The thesis’s main focus will be on understanding cybercrime, how it is being conducted worldwide, and what has led to an increase in these types of attacks.
The thesis will also discuss the initial attacks due to which cybercrime policies came into place. All policies will be discussed as to how they help curb cybercrimes and the extent to which they have been successful in reducing them.
Finally, the thesis will suggest if any new policies must be developed. What aspects need to be focused on, are there any new areas that need attention, or do the existing policies need to be revised?
Topic 6: Cybercrime Dissertation Topics – Cyber Crime: How it Impacts Young Adults
Research Aim: Cybercrime can have a great impact on the younger generation. Young adults use the internet more than any other age group, which is why they are the first victims of cybercrime. This dissertation will explore how cybercrime affects the younger generation and how it causes problems for them.
Issues such as health, specifically mental health, will be discussed to understand the many problems caused by cybercrime. Many individuals from the younger generation have attempted suicide after falling victim to cybercrime.
This research study will discuss all such effects of cybercrime, including cyberbullying (a form of cybercrime). The study will also present ways as to how they can avoid falling victim to cybercrime.
How Can ResearchProspect Help?
ResearchProspect writers can send several custom topic ideas to your email address. Once you have chosen a topic that suits your needs and interests, you can order for our dissertation outline service which will include a brief introduction to the topic, research questions , literature review , methodology , expected results , and conclusion . The dissertation outline will enable you to review the quality of our work before placing the order for our full dissertation writing service !
Topic 7: Cybercrime Dissertation Topics – Investigating Various Approaches and Ways to Detect Cyber Crime
Research Aim: Cybercrime, one of the most secret crimes, is spread all over the world. The number of cybercrimes worldwide is on the rise. Thus, every individual using a computer and connected to a network must be aware of the different types of cybercrimes.
Before discussing the different ways to detect cybercrime, this dissertation study will briefly discuss the many cybercrime types. Essentially, the research will focus on various ways through which each form of cybercrime can be detected.
Different forms of cybercrimes can be detected differently. For instance, data theft can be determined by asking for a password or other sensitive information through a call or an email. The research will then conclude how people can identify different forms of cybercrime and not fall victim to any of them.
Topic 8: Cybercrime Dissertation Topics – Evaluating Existing Cyber Crime Policies: Do They Suffice in Today’s World?
Research Aim: Cybercrime, being a major cause of concern throughout the world, is controlled and curbed by different policies in place. These policies are designed to make sure that cybercrime is reduced and gradually eliminated from society. However, with the increased numbers, the need for a policy change or amendment seems inevitable.
This means that the existing policies need to be reworked or revised, or abandoned completely, and new policies should be formed. This dissertation will investigate both these options and emphasize whether policies should be revised or new policies should be formed.
If new policies should be formed, the research will explain how these should be shaped, and if they need to be revised, then which aspects need to be considered for amendments will be the main focus of the dissertation. A detailed analysis will be presented to make an informed decision.
Topic 9: Cybercrime Dissertation Topics – Understanding the Different Types of Cyber Crime
Research Aim: Cybercrime, undoubtedly, is one of the most deadly forms of crime. Without causing physical harm, the crime causes the victim to attempt suicide or suffer from mental diseases such as anxiety, depression, etc.
This research will focus on the different types of cybercrimes that impact people in today’s world. This research will highlight almost all cybercrime forms while emphasising the most common forms such as cyberbullying, hacking, data theft, child pornography, etc.
In-depth research will be conducted through surveys and by using numbers and percentages of cybercrime from credible resources such as government websites, etc.
This will help understand the various forms of cybercrime, how widespread the crime is, and how many people are impacted by cybercrime throughout the world.
Important Notes:
As a cybercrime student looking to get good grades, it is essential to develop new ideas and experiment with existing cybercrime theories – i.e., to add value and interest to your research topic.
The field of cybercrime is vast and interrelated to so many other academic disciplines like Facebook , Instagram , Cryptocurrency , Twitter , civil engineering , facial recognition , construction , project management , engineering management , healthcare , finance and accounting , artificial intelligence , tourism , physiotherapy , sociology , management , and project management , graphic design , and nursing . That is why it is imperative to create a project management dissertation topic that is articular, sound, and actually solves a practical problem that may be rampant in the field.
We can’t stress how important it is to develop a logical research topic based on your entire research. There are several significant downfalls to getting your topic wrong; your supervisor may not be interested in working on it, the topic has no academic creditability, the research may not make logical sense, and there is a possibility that the study is not viable.
This impacts your time and efforts in writing your dissertation as you may end up in the cycle of rejection at the initial stage of the dissertation. That is why we recommend reviewing existing research to develop a topic, taking advice from your supervisor, and even asking for help in this particular stage of your dissertation.
Keeping our advice in mind while developing a research topic will allow you to pick one of the best cyber crime dissertation topics that fulfil your requirement of writing a research paper and add to the body of knowledge.
Therefore, it is recommended that when finalizing your dissertation topic, you read recently published literature to identify gaps in the research that you may help fill.
Remember- dissertation topics need to be unique, solve an identified problem, be logical, and be practically implemented. Please look at some of our sample cybercrime dissertation topics to get an idea for your own dissertation.
How to Structure your Cyber Crime Dissertation
A well-structured dissertation can help students to achieve a high overall academic grade.
- A Title Page
- Acknowledgements
- Declaration
- Abstract: A summary of the research completed
- Table of Contents
- Introduction : This chapter includes the project rationale, research background, key research aims and objectives, and the research problems. An outline of the structure of a dissertation can also be added to this chapter.
- Literature Review : This chapter presents relevant theories and frameworks by analysing published and unpublished literature available on the chosen research topic to address research questions . The purpose is to highlight and discuss the selected research area’s relative weaknesses and strengths whilst identifying any research gaps. Break down the topic, and key terms that can positively impact your dissertation and your tutor.
- Methodology : The data collection and analysis methods and techniques employed by the researcher are presented in the Methodology chapter which usually includes research design , research philosophy, research limitations, code of conduct, ethical consideration, data collection methods, and data analysis strategy .
- Findings and Analysis : Findings of the research are analysed in detail under the Findings and Analysis chapter. All key findings/results are outlined in this chapter without interpreting the data or drawing any conclusions. It can be useful to include graphs, charts, and tables in this chapter to identify meaningful trends and relationships.
- Discussion and Conclusion : The researcher presents his interpretation of the results in this chapter, and states whether the research hypothesis has been verified or not. An essential aspect of this section of the paper is to draw a linkage between the results and evidence from the literature. Recommendations with regards to implications of the findings and directions for the future may also be provided. Finally, a summary of the overall research, along with final judgments, opinions, and comments, must be included in the form of suggestions for improvement.
- References : This should be completed following your University’s requirements
- Bibliography
- Appendices : Any additional information, diagrams, and graphs used to complete the dissertation but not part of the dissertation should be included in the Appendices chapter. Essentially, the purpose is to expand the information/data.
About ResearchProspect Ltd
ResearchProspect is the world’s best academic writing service that provides help with Dissertation Proposal Writing , PhD Proposal Writing , Dissertation Writing , Dissertation Editing, and Improvement .
Our team of writers is highly qualified. They are experts in their respective fields. They have been working in the industry for a long, thus are aware of the issues and the trends of the industry they are working in.
Free Dissertation Topic
Phone Number
Academic Level Select Academic Level Undergraduate Graduate PHD
Academic Subject
Area of Research
Frequently Asked Questions
How to find dissertation topics on cyber crime.
To find dissertation topics on cybercrime:
- Study recent cyber threats and attacks.
- Analyze legal and ethical aspects.
- Explore technological advancements.
- Investigate prevention measures.
- Consider international perspectives.
- Select a focused area of interest for in-depth research.
You May Also Like
Physiotherapy is a healthcare profession that deals with movement disorders of the body arising from different conditions. Physiotherapy focuses on performing practices that reduce physical ailments.
Here is a list of Ecology dissertation topics to help you choose the one studies anyone as per your requirements.
Urban geography is a growing field of study that provides learners with a comprehensive understanding of how cities, towns and other human settlements develop and change over time.
USEFUL LINKS
LEARNING RESOURCES

COMPANY DETAILS
- How It Works
- Work & Careers
- Life & Arts
Become an FT subscriber
Limited time offer save up to 40% on standard digital.
- Global news & analysis
- Expert opinion
- Special features
- FirstFT newsletter
- Videos & Podcasts
- Android & iOS app
- FT Edit app
- 10 gift articles per month
Explore more offers.
Standard digital.
- FT Digital Edition
Premium Digital
Print + premium digital.
Then $75 per month. Complete digital access to quality FT journalism on any device. Cancel anytime during your trial.
- 10 additional gift articles per month
- Global news & analysis
- Exclusive FT analysis
- Videos & Podcasts
- FT App on Android & iOS
- Everything in Standard Digital
- Premium newsletters
- Weekday Print Edition
Complete digital access to quality FT journalism with expert analysis from industry leaders. Pay a year upfront and save 20%.
- Everything in Print
- Everything in Premium Digital
The new FT Digital Edition: today’s FT, cover to cover on any device. This subscription does not include access to ft.com or the FT App.
Terms & Conditions apply
Explore our full range of subscriptions.
Why the ft.
See why over a million readers pay to read the Financial Times.
International Edition
- International edition
- Australia edition
- Europe edition
Chinese ‘state-affiliated’ organisations behind cyber-attacks on MPs and Electoral Commission, Dowden says – as it happened
Deputy PM says international partners, including the US, will also be making statements today about similar Chinese cyber-attacks. This live blog is closed
- Chinese hackers targeted UK’s Electoral Commission and politicians, say security services
- 4d ago Early evening summary
- 4d ago Home Office accepts recommendations in Angiolini report on treating indecent exposure more seriously
- 5d ago Stride tells MPs DWP will 'fully and properly' consider report saying Waspi women should get compensation
- 5d ago Vaughan Gething plays down prospect of M4 relief road plan being revived
- 5d ago Dowden dismisses Labour questions about Cameron's China links as 'desperate stuff'
- 5d ago Dowden says goverment still trying to reach agreement on whether to submit China to 'enhanced' scrutiny under National Security Act
- 5d ago Dowden describes anti-China measures as a 'first step' after being urged to call Beijing as 'threat'
- 5d ago Dowden says cyber-attacks show 'clear and persistent pattern' of 'hostile intent' from China
- 5d ago Oliver Dowden tells MPs Chinese 'state-affiliated' organisations behind cyber-attacks on Electoral Commission and on MPs
- 5d ago Sunak facing fresh byelection challenge after Scott Benton resigns as MP before recall petition closes
- 5d ago Gove apologises over 'minor' breach of Commons rules relating to VIP football match tickets not declared in register
- 5d ago No 10 insists it remains committed to leasehold reform following reports plan to axe ground rents in jeopardy
- 5d ago No 10 accepts £100,000 a year is a high salary, while defending Jeremy Hunt over his claims suggesting it isn't
- 5d ago Energy minister Andrew Bowie says government's investment in nuclear power should have happened 'years ago'
- 5d ago Sunak insists UK has 'very strong' capabilities to resist cyber-attacks
- 5d ago Sunak announces investment worth more than £200m over 10 years for Barrow
- 5d ago Lib Dems say it's 'outrageous' Cameron won't take questions from Commons as whole, but will speak to Tory MPs in private
- 5d ago How serious was Electoral Commison cyber-attack being blamed on China?
- 5d ago Home Office launches social media campaigning to try to deter people in Vietnam from entering UK illegally on small boats
- 5d ago Labour says its Great British Energy company would prioritise floating offshore energy
- 5d ago UK ‘slow to hold China to account’ for cyber-attacks against MPs and voters
- 5d ago Government urged to end its ‘naivety on China’ as Dowden to brief MPs on Beijing’s role in cyber-attacks

Oliver Dowden tells MPs Chinese 'state-affiliated' organisations behind cyber-attacks on Electoral Commission and on MPs
Oliver Dowden , the deputy PM, is making his Commons statement. He says it is about malicious cyber activity directed at the UK by actors affiliated to the Chinese state.
He says Chinese state-affiliated actors have been involved in two cyber-attacks on the UK: the hacking of the Electoral Commission , and attacks aimed at parliamentarians.
He says international partners, including the US, will be making statements today about similar Chinese cyber-attacks they have suffered.
Early evening summary
Chinese state-backed hackers were responsible for two “malicious” digital campaigns targeting the UK’s democratic institutions and politicians, the security services have found.
Rishi Sunak is to face another tricky byelection in the coming weeks after the former Conservative backbencher Scott Benton quit parliament before the conclusion of a recall petition among his constituents.
Mel Stride, the work and pensions secretary, has been criticised by campaigners for giving a non-committal response in the Commons to the report saying the government should pay compensation to the Waspi women. (See 5.26pm .) The chair of Women Against State Pension Inequality (Waspi), Angela Madden, responded to what he said with this statement:
The secretary of state now says this matter is so complex, he needs yet more months and years of head scratching to sort it out. He has made much of the report being 100 pages long as if he were being asked to digest War and Peace . The fact it is has taken five years for the ombudsman to produce his conclusions is a pretty perverse reason to say more delay is now justified. The report is not complicated at all. He says that 1950s-born women should be compensated and that Parliament should intervene to make a scheme happen. Every day 111 of the affected women die waiting for justice. The Commons must get a debate and vote on compensation as soon as possible after Easter.
Labour’s plan for state-backed offshore windfarms will be a “gamechanger”, Keir Starmer has said, as the party seeks to regain the initiative on green policy after the slow-motion ditching of its £28bn investment pledge.
Michael Gove breached standards rules by failing to register hospitality he enjoyed with a Conservative donor whose company was awarded personal protective equipment contracts during the Covid pandemic, parliament’s sleaze watchdog has found.

Murdo Fraser , a Conservative MSP, has threatened to take legal action against Police Scotland after a tweet he posted comparing choosing to identify as non-binary to “choosing to identify as a cat” was logged as a hate incident, the BBC reports.
Home Office accepts recommendations in Angiolini report on treating indecent exposure more seriously
The Home Office has announced that it is accepting the recommendations in the report from Dame Elish Angiolini last month into the events leading up to the rape and murder of Sarah Everard by a police officer. They include calling for a public campaign “to raise awareness that indecent exposure and sending unsolicited photographs of genitals amounts to criminality”.
The Conservatives have had to remove an online video attacking Labour’s record on crime in London after it was pointed out to them that the video they were using was from New York, Kevin Schofield from HuffPost UK reports.
NEW: The Tories have been forced to delete a Labour attack video about crime in London after it featured a scene showing chaos at Penn Station in ... er New York. pic.twitter.com/NQm6EA5tNy — Kevin Schofield (@KevinASchofield) March 25, 2024
Stride tells MPs DWP will 'fully and properly' consider report saying Waspi women should get compensation
In the Commons Mel Stride , the work and pensions secretary, is giving a statement about the report from the Parliamentary and Health Service Ombudsman (PHSO) published on Thursday saying the goverment should pay compensation to women who lost out because the government did not adequately communicate the fact that a decision was taken in the 1990s to raise the age at which they would start getting the state pension. These are the so-called Waspi women, named after the campaign called Women Against State Pension Inequality.
The PHSO said its compensation plan could cost up to £10.5bn (campaigners claim this isn’t enough, and that a more generous compensation scheme is needed) and on Thursday the government just said it would consider the recommendations, without committing to compensation of any kind.
In his statement Stride said very little that went beyond this. He said the PHSO did not criticise the decision to raise the state pension age for women, and he said that women involved did not suffer a “direct” financial loss from the decision taken by the DWP. But it did find the DWP did not publicise the forthcoming changes as well as it should have done, he said.
The government would “fully and properly consider the findings” in the report, he said.
Vaughan Gething plays down prospect of M4 relief road plan being revived
Keir Starmer and Vaughan Gething , the new first minister of Wales, gave a brief interview to WalesOnline today while they were on their visit to Holyhead. According to the write-up , much of it consisted the two leaders giving slightly evasive answers about the prospect of the plan to build an M4 relief road in south Wales being revived.
When Mark Drakeford was first minister, he ruled out the idea on environmental grounds.
At the weekend Ken Skates , the new transport secretary in Gething’s cabinet, gave an interview implying there could be a rethink in relation to some road schemes that have been blocked. He was fairly clear that the M4 relief road plan would not be resurrected (“I just can’t see that happening – the cost would just be astronomical”). But David TC Davies , the Welsh secretary, responded to the Skates interview by claiming that if money were the only problem, Westminster might be willing to help out – thereby implying this could be an election issue.
Starmer and Gething both stressed to WalesOnline that they wanted more infrastructure investment in Wales , while not saying anything to suggest that an M4 relief road would be on their list. “David TC Davies may say he wants to sit down and talk to us but that isn’t the relationship we find with the UK government,” Gething said.
Carol Monaghan (SNP) asks about the threat posed by electric cars manufactured in China to the UK.
Dowden says cars would have to meet UK safety standards. And he says the government can block investments on security grounds.
Back in the Commons Vicky Ford (Con) says she is very concerned about the physical safety of MPs. She says on Friday last week the security guards she was advised to have at her constituency surgery did not turn up. That was the second time this year this has happened, she says.
Dowden says the government takes threats to MPs exceptionally seriously. He says he will take his issue up.

Chris Law (SNP) asks why anyone can trust the government when it has been “far too late” responding to the threat from China .
Dowden does not accept that. He says he has consistently warned about the threat from China.
Dowden dismisses Labour questions about Cameron's China links as 'desperate stuff'
Stephen Kinnock (Lab) asks about David Cameron’s visit to Sri Lanka to back a Chinese investment scheme. He says the Foreign Office has not replied to Freedom of Information requests about this. Will Dowden ensure it does?
Dowden says this is “pretty desperate stuff”. He goes on:
Trying to link Chinese cyber-attacks to our our current foreign secretary just doesn’t wash.
Here is our story on the Dowden announcement by Pippa Crerar and Eleni Courea.
- Politics live with Andrew Sparrow
- Conservatives
- Rishi Sunak
- Keir Starmer
Comments (…)
Most viewed.
Special Features
Vendor voice.
Cyber-crime
US charges Chinese nationals with cyber-spying on pretty much everyone for Beijing
Plus: alleged front sanctioned, uk blames prc for electoral commission theft, and does america need a cyber force.
The United States on Monday accused seven Chinese men of breaking into computer networks, email accounts, and cloud storage belonging to numerous critical infrastructure organizations, companies, and individuals, including US businesses, politicians, and their political parties.
According to American prosecutors, the suspected spies are members of APT31, a cyber-espionage group said to be run by China's Ministry of State Security (MSS) out of Wuhan and otherwise known as Zirconium, Violet Typhoon, Judgment Panda, and Altaire.
And according to the UK government today, that's the same crew responsible for the attempted compromise of British politicians' email accounts in 2021 .
Both the UK and the US sanctioned Wuhan Xiaoruizhi Science and Technology, said to be a front company for the MSS and its computer-intrusion activities, and two of the seven Chinese nationals for their alleged roles in that espionage. The UK also separately disclosed today that it believes its Electoral Commission was compromised between 2021 and 2022 by Chinese agents, who stole email data, and data from the Electoral Register.
The seven suspected members of APT31 charged by the United States on Monday are: Ni Gaobin, 38; Weng Ming, 37; Cheng Feng, 34; Peng Yaowen, 38; Sun Xiaohui, 38; Xiong Wang, 35; and Zhao Guangzong, 38. Gaobin and Guangzong were the pair sanctioned by the UK and US regarding Wuhan Xiaoruizhi.
All are believed to reside in the People's Republic of China, so there's a slim-to-zero chance of them being arrested and extradited to stand trial in the US, at least, for their alleged crimes.
That said, perhaps money will change all that. Uncle Sam offered a reward of up to $10 million for information on the seven individuals in the hope that someone will snitch and assist the Feds in bringing the alleged spies to justice. Or it could just be fancy posturing; what does the NSA and CIA, and MI6 and GCHQ, do all day, one doesn't have to wonder.

The US State Dept's wanted poster for the APT31 suspects ... Click to enlarge
According to the indictment [ PDF ] against the men in the US, the seven defendants worked with dozens of other MSS intel officers, contractors, and support personnel to compromise and spy on computer networks and online accounts that were of interest to Beijing.
'Thousands' targeted, 'millions' potentially affected
Since at least 2010, the alleged gang conducted massive globe-spanning campaigns targeting "thousands" of US and foreign individuals and companies, with a particular emphasis on journalists; pro-democracy activists; foreign policy experts; academics; workers in IT, telecoms, manufacturing and trade, finance, consulting, law, and research; and government officials, politicians, and candidates who have been critical of the Chinese government. We're told that trade secrets as well as personal data were pilfered.
"These computer network intrusion activities resulted in the confirmed and potential compromise of work and personal email accounts, cloud storage accounts and telephone call records belonging to millions of Americans, including at least some information that could be released in support of malign influence targeting democratic processes and institutions, and economic plans, intellectual property, and trade secrets belonging to American businesses, and contributed to the estimated billions of dollars lost every year as a result of the PRC's state-sponsored apparatus to transfer US technology to the PRC," the indictment thundered.
For instance, the Chinese g-men, it is claimed, sent "thousands" of crafty email messages to personal and professional accounts belonging to politicians and their family members, purporting to be from prominent American journalists. These messages contained malicious links that, when opened, disclosed the recipient's physical location and IP addresses as well as information about their networks and specific devices used to access the emails.
Chinese snoops use F5, ConnectWise bugs to sell access into top US, UK networks
- Exposed: Chinese smartphone farms that run thousands of barebones mobes to do crime
Beijing-backed cyberspies attacked 70+ orgs across 23 countries
Russia's cozy bear caught phishing german politicos with phony dinner invites.
"The conspirators used this method to enable more direct and sophisticated targeting of recipients' home routers and other electronic devices, including those of high-ranking US government officials and politicians and election campaign staff from both major US political parties," according to the indictment.
Report calls for US Cyber Force
The cyber-spy charges comes as a report urges the creation of a US Cyber Force — a new, independent branch of the military that will recruit and train defenders to protect America against online threats to national security.
"Years after designating cyberspace as a warfighting domain, leaders must acknowledge the writing on the wall," according to that report published Monday by the Foundation for Defense of Democracies, or FDD.
Report authors retired Rear Admiral Mark Montgomery, who is senior director of FDD's Center on Cyber and Technology Innovation, and Erica Lonergan, assistant professor in the School of International and Public Affairs at Columbia University, were both members of the government's Cyberspace Solarium Commission .
They interviewed more than 75 active duty and retired US military officers for their report, and noted "America's cyber force generation system is clearly broken."
The only way to fix it, they conclude, is an independent Cyber Force, located within the Army. The proposal is for 6,200 servicemembers, civilians, and contractors.
"The scope and scale of cyber threats are growing," the report stated, pointing to both China and Russia, and noting both countries' willingness to use cyber capabilities to disrupt critical infrastructure, military communications and American politics.
It concluded: "Only Congress can create a new independent service, so it is time for lawmakers to act."
Some of APT31's targets allegedly included individuals at the White House; and the US Departments of Justice, Commerce, Treasury, State, Labor and Transportation, as well as members of Congress and the spouses of a high-ranking Department of Justice official, high-ranking White House officials, and multiple US senators.
Outside of the United States, some of the gang's targets, according to prosecutors, included members of the Inter-Parliamentary Alliance on China (IPAC), a group founded in 2020 on the anniversary of the 1989 Tiananmen Square protests and massacre, plus dissidents and academics critical of the PRC, and 43 UK parliamentary IT accounts.
In addition to sending phishing emails, the crew also used "sophisticated types of custom malware such as RAWDOOR, Trochilus, EvilOSX, DropDoor/DropCat and others" to backdoor victims' machines, execute payloads, and steal sensitive data, it is claimed.
The indictment described one alleged intrusion in late 2016 during which a zero-day privilege-escalation exploit was used to drill into a US defense contractor with offices in Long Island, New York. This is just one of the "multiple" contractors providing products and services to the American military that the crew snooped on, it is claimed.
After exploiting the zero-day vulnerability, the alleged spies created a new account within the corporate network with admin privileges, uploaded a web shell for remote access and to establish a connection with APT31-controlled infrastructure, and then snooped around the defense contractor's systems and files.
In another example, between 2017 and 2019, it's claimed the crew broke into the networks of seven IT managed-service providers (MSPs) in New York, California, Massachusetts, Colorado, Idaho, and overseas. They then used this access to infiltrate servers belonging to the MSPs' customers, we're told.
From the California MSP alone the snoops gained access to at least 15 servers on seven remote networks, it is claimed. Affected customers included a financial business, a nuclear power engineering company, an enterprise-resources planning outfit, and three additional IT managed-service providers.
Other victim organizations include "a leading provider of 5G network equipment in the United States," a steel company, a New York-based apparel manufacturer, a California engineering company, an energy firm in Texas, and "many others." ®
Narrower topics
- Advanced persistent threat
- Application Delivery Controller
- Authentication
- China Mobile
- China telecom
- China Unicom
- Common Vulnerability Scoring System
- Cybersecurity
- Cybersecurity and Infrastructure Security Agency
- Cybersecurity Information Sharing Act
- Cyberspace Administration of China
- Data Breach
- Data Protection
- Digital certificate
- Great Firewall
- Identity Theft
- Incident response
- Kenna Security
- Palo Alto Networks
- Quantum key distribution
- Remote Access Trojan
- RSA Conference
- Semiconductor Manufacturing International Corporation
- Surveillance
- Trusted Platform Module
- Uyghur Muslims
- Vulnerability
Broader topics
Send us news
Other stories you might like
Uk elections are unaffected by china's cyber-interference, says deputy pm, developing ai workloads is complex. deciding where to run them might be easier.
Five Eyes tell critical infra orgs: Take these actions now to protect against China's Volt Typhoon
Miscreants are exploiting enterprise tech zero days more and more, google warns, 'thousands' of businesses at mercy of miscreants thanks to unpatched ray ai flaw, forget tiktok – chinese spies want to steal ip by backdooring digital locks, vans claims cyber crooks didn't run off with its customers' financial info, fujitsu: miscreants infected our systems with malware, may have stolen customer info, international effort to disrupt cybercrime moves into operational phase.
- Advertise with us
Our Websites
- The Next Platform
- Blocks and Files
Your Privacy
- Cookies Policy
- Privacy Policy
- Ts & Cs

Copyright. All rights reserved © 1998–2024

VIDEO
COMMENTS
116 CyberCrime Topics & Essay Samples. Updated: Mar 2nd, 2024. 9 min. If you are writing a cybercrime essay, our team prepared this article just for you. Here, you will find 115 unique topics for any type of paper. We will write. a custom essay specifically for you by our professional experts. 809 writers online.
500+ Words Essay on Cyber Crime. Cyber Crime Essay - Everybody thinks that only stealing someone's private data is Cyber Crime. But in defining terms we can say that 'Cyber Crime refers to the use of an electronic device (computer, laptop, etc.) for stealing someone's data or trying to harm them using a computer.
100 Words Essay on Cyber Crime. Cybercrime is the most discussed problem in the twenty-first century. The usage of cellphones and the internet is increasing dramatically over the world, which is generating questions about consumers' security and privacy. Because of this, it is crucial for all users to understand cybercrime and security.
Here, we present 117 cybercrime essay topic ideas and examples to help inspire your writing. The rise of ransomware attacks: Causes, consequences, and preventive measures. Cyberbullying: Analyzing its psychological impact on victims and strategies for prevention. Social engineering attacks: Understanding the methods and mitigating the risks.
These essay examples and topics on Cybercrime were carefully selected by the StudyCorgi editorial team. They meet our highest standards in terms of grammar, punctuation, style, and fact accuracy. Please ensure you properly reference the materials if you're using them to write your assignment. This essay topic collection was updated on ...
Recommended Cyber Crimes Essay Topics. If you are looking for essay topics related to cyber crimes, you have come to the right place. Below is a list of recommended cyber crimes essay topics, categorized for ease of selection. These topics cover a wide range of issues related to cyber crimes and provide ample opportunities for in-depth research ...
Essay on Cyber Crime. Cyber crime is the most discussed issue of the 21st century. The technology sector world wide is witnessing a boom in the consumer of smartphones and the internet which is raising concerns with regard to the privacy and security of the users. Owing to this reason, it is highly essential for all the users to know about ...
Cyber Crime Is a Serious. PAGES 8 WORDS 2431. These "stepping stone" computes can be located anywhee in the physical wold because eal-space is ielevant to activity in cybespace (Benne, 379)." The use of stepping stones can make it difficult fo law enfocement to find whee an attack actually oiginated.
Cybersecurity Necessity and Benefits. Second, the exploration of human factors in the framework of cyber-security can assist in resolving the issues of understanding a defender's cognitive state, possibilities for automation, and an attacker's subjective traits. Cybersecurity Incident Response and Risk Minimization.
2. Proliferation and Commercialization (1990s-2000s) Explosion of Malware: Malicious software, including viruses, worms, and trojans, became more prevalent in the 1990s. Commercial Exploitation: Cyber Crime became increasingly profit-driven with the advent of financial fraud, identity theft, and the rise of the cyber black market. 3.
Students are often asked to write an essay on Cyber Crime in their schools and colleges. And if you're also looking for the same, we have created 100-word, 250-word, and 500-word essays on the topic. Let's take a look… 100 Words Essay on Cyber Crime Introduction to Cyber Crime. Cybercrime refers to illegal activities conducted through the ...
Essay on Cybercrime in 300 Words. Economists have termed cybercrime as ' A Hidden Threat to the Digital World.'. Modern humans are relying on the internet for their day-to-day activities and every macro and micro activity. In this sense, the term cybercrime comes to the front. Cybercrime refers to criminal activities conducted through the ...
Check out original essays on Cyber Crime | You can find over 30k essay samples | Meet your academic needs with EduZaurus ... 3 Pages 1429 Words Topics: Cyber crime, Cyber Security, Internet . Cyber Crime Cyber Security Security . Information Security and the Rise of Cyber Crimes.
Introduction. Cyber crime evolved since 1990 when computers and networks came in to being. The types of attacks gradually grew from "Morris code worm" in 1997 to "Torjan" in 2004 and to "Ransom ware " attack in 2013. When computers and networks came into being in the 1990s, hacking was done basically to get more information about ...
Long and Short Essays on Cyber Crime for Students and Kids in English. We are providing students with essay samples on an extended essay of 500 words and a short piece of 150 words on the topic Cyber Crime for reference. Long Essay on Cyber Crime 500 Words in English. Long Essay on Cyber Crime is usually given to classes 7, 8, 9, and 10.
As technology evolves, so do cyber threats. Ongoing research and innovation in cybersecurity are essential to staying ahead of cybercriminals. Conclusion of Essay on Cyber Crime. In conclusion, cybercrime is a digital menace that affects us all. Whether it's hacking, scams, or cyberbullying, the consequences can be devastating.
Excellent Research Topics on Cybercrime. Write about the importance of cybercrime management. Explain the history of cybercrime. Discuss the effects of cybercrime on the Internet economy. Talk about the cyberattack on Sony Pictures in 2014. Explain how technology has influenced the evolution of cybercrime.
This essay delves into the intricacies of cyber crime, exploring its types, causes, impacts, and measures to combat it, offering a comprehensive overview for students participating in essay writing competitions. Cyber Crime. Cyber crime refers to any criminal activity that involves a computer, networked device, or a network.
This increase in, and shift to, cybercrime, combined with interchangeable and often confusing terminology, has led to recent suggestion that the prefix 'cyber-' may soon become redundant, as almost all crimes will be touched by technology (Furnell and Dowling, 2019).Indeed, all serious and organised crimes investigated now feature some encryption, and the Internet is used in the ...
50 Latest Cyber crime IELTS Topics. Get a band score and detailed report instantly. Check your IELTS essays right now! Read more ». Problem and Solution. Many people today are worried about cybercrime such as hacking and identity theft . what problem does cyber crime cause, and what solution can you suggest for ordinary people and business to ...
Get your free examples of research papers and essays on Cyber Crime here. Only the A-papers by top-of-the-class students. Learn from the best! ... Essay Topics. Essays on Cyber Crime. 10 samples on this topic . Writing lots of Cyber Crime papers is an essential part of contemporary studying, be it in high-school, college, or university. If you ...
Cyber Crime Essay 10 Lines (100 - 150 Words) 1) The crime done with the help of a computer network is termed as cybercrime. 2) Cybercrime can harm your privacy and security. 3) Cybercrime is an illegal act that tends to hack your private data. 4) Cybercriminals try to gain money through illegal methods. 5) Phishing, DoS attack, spoofing, etc ...
Topic 9: Cybercrime Dissertation Topics - Understanding the Different Types of Cyber Crime Research Aim: Cybercrime, undoubtedly, is one of the most deadly forms of crime. Without causing physical harm, the crime causes the victim to attempt suicide or suffer from mental diseases such as anxiety, depression, etc.
Publicly available information about wealthy people can aid cyber criminals in launching social engineering attacks, stealing personal identities and creating AI-generated videos of their victims ...
Oliver Dowden tells MPs Chinese 'state-affiliated' organisations behind cyber-attacks on Electoral Commission and on MPs. Oliver Dowden, the deputy PM, is making his Commons statement.He says it ...
The seven suspected members of APT31 charged by the United States on Monday are: Ni Gaobin, 38; Weng Ming, 37; Cheng Feng, 34; Peng Yaowen, 38; Sun Xiaohui, 38; Xiong Wang, 35; and Zhao Guangzong, 38. Gaobin and Guangzong were the pair sanctioned by the UK and US regarding Wuhan Xiaoruizhi. All are believed to reside in the People's Republic of China, so there's a slim-to-zero chance of them ...