

Choose Your Test
Sat / act prep online guides and tips, how to do homework: 15 expert tips and tricks.
Coursework/GPA

Everyone struggles with homework sometimes, but if getting your homework done has become a chronic issue for you, then you may need a little extra help. That’s why we’ve written this article all about how to do homework. Once you’re finished reading it, you’ll know how to do homework (and have tons of new ways to motivate yourself to do homework)!
We’ve broken this article down into a few major sections. You’ll find:
- A diagnostic test to help you figure out why you’re struggling with homework
- A discussion of the four major homework problems students face, along with expert tips for addressing them
- A bonus section with tips for how to do homework fast
By the end of this article, you’ll be prepared to tackle whatever homework assignments your teachers throw at you .
So let’s get started!

How to Do Homework: Figure Out Your Struggles
Sometimes it feels like everything is standing between you and getting your homework done. But the truth is, most people only have one or two major roadblocks that are keeping them from getting their homework done well and on time.
The best way to figure out how to get motivated to do homework starts with pinpointing the issues that are affecting your ability to get your assignments done. That’s why we’ve developed a short quiz to help you identify the areas where you’re struggling.
Take the quiz below and record your answers on your phone or on a scrap piece of paper. Keep in mind there are no wrong answers!
1. You’ve just been assigned an essay in your English class that’s due at the end of the week. What’s the first thing you do?
A. Keep it in mind, even though you won’t start it until the day before it’s due B. Open up your planner. You’ve got to figure out when you’ll write your paper since you have band practice, a speech tournament, and your little sister’s dance recital this week, too. C. Groan out loud. Another essay? You could barely get yourself to write the last one! D. Start thinking about your essay topic, which makes you think about your art project that’s due the same day, which reminds you that your favorite artist might have just posted to Instagram...so you better check your feed right now.
2. Your mom asked you to pick up your room before she gets home from work. You’ve just gotten home from school. You decide you’ll tackle your chores:
A. Five minutes before your mom walks through the front door. As long as it gets done, who cares when you start? B. As soon as you get home from your shift at the local grocery store. C. After you give yourself a 15-minute pep talk about how you need to get to work. D. You won’t get it done. Between texts from your friends, trying to watch your favorite Netflix show, and playing with your dog, you just lost track of time!
3. You’ve signed up to wash dogs at the Humane Society to help earn money for your senior class trip. You:
A. Show up ten minutes late. You put off leaving your house until the last minute, then got stuck in unexpected traffic on the way to the shelter. B. Have to call and cancel at the last minute. You forgot you’d already agreed to babysit your cousin and bake cupcakes for tomorrow’s bake sale. C. Actually arrive fifteen minutes early with extra brushes and bandanas you picked up at the store. You’re passionate about animals, so you’re excited to help out! D. Show up on time, but only get three dogs washed. You couldn’t help it: you just kept getting distracted by how cute they were!
4. You have an hour of downtime, so you decide you’re going to watch an episode of The Great British Baking Show. You:
A. Scroll through your social media feeds for twenty minutes before hitting play, which means you’re not able to finish the whole episode. Ugh! You really wanted to see who was sent home! B. Watch fifteen minutes until you remember you’re supposed to pick up your sister from band practice before heading to your part-time job. No GBBO for you! C. You finish one episode, then decide to watch another even though you’ve got SAT studying to do. It’s just more fun to watch people make scones. D. Start the episode, but only catch bits and pieces of it because you’re reading Twitter, cleaning out your backpack, and eating a snack at the same time.
5. Your teacher asks you to stay after class because you’ve missed turning in two homework assignments in a row. When she asks you what’s wrong, you say:
A. You planned to do your assignments during lunch, but you ran out of time. You decided it would be better to turn in nothing at all than submit unfinished work. B. You really wanted to get the assignments done, but between your extracurriculars, family commitments, and your part-time job, your homework fell through the cracks. C. You have a hard time psyching yourself to tackle the assignments. You just can’t seem to find the motivation to work on them once you get home. D. You tried to do them, but you had a hard time focusing. By the time you realized you hadn’t gotten anything done, it was already time to turn them in.
Like we said earlier, there are no right or wrong answers to this quiz (though your results will be better if you answered as honestly as possible). Here’s how your answers break down:
- If your answers were mostly As, then your biggest struggle with doing homework is procrastination.
- If your answers were mostly Bs, then your biggest struggle with doing homework is time management.
- If your answers were mostly Cs, then your biggest struggle with doing homework is motivation.
- If your answers were mostly Ds, then your biggest struggle with doing homework is getting distracted.
Now that you’ve identified why you’re having a hard time getting your homework done, we can help you figure out how to fix it! Scroll down to find your core problem area to learn more about how you can start to address it.
And one more thing: you’re really struggling with homework, it’s a good idea to read through every section below. You may find some additional tips that will help make homework less intimidating.
How to Do Homework When You’re a Procrastinator
Merriam Webster defines “procrastinate” as “to put off intentionally and habitually.” In other words, procrastination is when you choose to do something at the last minute on a regular basis. If you’ve ever found yourself pulling an all-nighter, trying to finish an assignment between periods, or sprinting to turn in a paper minutes before a deadline, you’ve experienced the effects of procrastination.
If you’re a chronic procrastinator, you’re in good company. In fact, one study found that 70% to 95% of undergraduate students procrastinate when it comes to doing their homework. Unfortunately, procrastination can negatively impact your grades. Researchers have found that procrastination can lower your grade on an assignment by as much as five points ...which might not sound serious until you realize that can mean the difference between a B- and a C+.
Procrastination can also negatively affect your health by increasing your stress levels , which can lead to other health conditions like insomnia, a weakened immune system, and even heart conditions. Getting a handle on procrastination can not only improve your grades, it can make you feel better, too!
The big thing to understand about procrastination is that it’s not the result of laziness. Laziness is defined as being “disinclined to activity or exertion.” In other words, being lazy is all about doing nothing. But a s this Psychology Today article explains , procrastinators don’t put things off because they don’t want to work. Instead, procrastinators tend to postpone tasks they don’t want to do in favor of tasks that they perceive as either more important or more fun. Put another way, procrastinators want to do things...as long as it’s not their homework!
3 Tips f or Conquering Procrastination
Because putting off doing homework is a common problem, there are lots of good tactics for addressing procrastination. Keep reading for our three expert tips that will get your homework habits back on track in no time.
#1: Create a Reward System
Like we mentioned earlier, procrastination happens when you prioritize other activities over getting your homework done. Many times, this happens because homework...well, just isn’t enjoyable. But you can add some fun back into the process by rewarding yourself for getting your work done.
Here’s what we mean: let’s say you decide that every time you get your homework done before the day it’s due, you’ll give yourself a point. For every five points you earn, you’ll treat yourself to your favorite dessert: a chocolate cupcake! Now you have an extra (delicious!) incentive to motivate you to leave procrastination in the dust.
If you’re not into cupcakes, don’t worry. Your reward can be anything that motivates you . Maybe it’s hanging out with your best friend or an extra ten minutes of video game time. As long as you’re choosing something that makes homework worth doing, you’ll be successful.
#2: Have a Homework Accountability Partner
If you’re having trouble getting yourself to start your homework ahead of time, it may be a good idea to call in reinforcements . Find a friend or classmate you can trust and explain to them that you’re trying to change your homework habits. Ask them if they’d be willing to text you to make sure you’re doing your homework and check in with you once a week to see if you’re meeting your anti-procrastination goals.
Sharing your goals can make them feel more real, and an accountability partner can help hold you responsible for your decisions. For example, let’s say you’re tempted to put off your science lab write-up until the morning before it’s due. But you know that your accountability partner is going to text you about it tomorrow...and you don’t want to fess up that you haven’t started your assignment. A homework accountability partner can give you the extra support and incentive you need to keep your homework habits on track.
#3: Create Your Own Due Dates
If you’re a life-long procrastinator, you might find that changing the habit is harder than you expected. In that case, you might try using procrastination to your advantage! If you just can’t seem to stop doing your work at the last minute, try setting your own due dates for assignments that range from a day to a week before the assignment is actually due.
Here’s what we mean. Let’s say you have a math worksheet that’s been assigned on Tuesday and is due on Friday. In your planner, you can write down the due date as Thursday instead. You may still put off your homework assignment until the last minute...but in this case, the “last minute” is a day before the assignment’s real due date . This little hack can trick your procrastination-addicted brain into planning ahead!
If you feel like Kevin Hart in this meme, then our tips for doing homework when you're busy are for you.
How to Do Homework When You’re too Busy
If you’re aiming to go to a top-tier college , you’re going to have a full plate. Because college admissions is getting more competitive, it’s important that you’re maintaining your grades , studying hard for your standardized tests , and participating in extracurriculars so your application stands out. A packed schedule can get even more hectic once you add family obligations or a part-time job to the mix.
If you feel like you’re being pulled in a million directions at once, you’re not alone. Recent research has found that stress—and more severe stress-related conditions like anxiety and depression— are a major problem for high school students . In fact, one study from the American Psychological Association found that during the school year, students’ stress levels are higher than those of the adults around them.
For students, homework is a major contributor to their overall stress levels . Many high schoolers have multiple hours of homework every night , and figuring out how to fit it into an already-packed schedule can seem impossible.
3 Tips for Fitting Homework Into Your Busy Schedule
While it might feel like you have literally no time left in your schedule, there are still ways to make sure you’re able to get your homework done and meet your other commitments. Here are our expert homework tips for even the busiest of students.
#1: Make a Prioritized To-Do List
You probably already have a to-do list to keep yourself on track. The next step is to prioritize the items on your to-do list so you can see what items need your attention right away.
Here’s how it works: at the beginning of each day, sit down and make a list of all the items you need to get done before you go to bed. This includes your homework, but it should also take into account any practices, chores, events, or job shifts you may have. Once you get everything listed out, it’s time to prioritize them using the labels A, B, and C. Here’s what those labels mean:
- A Tasks : tasks that have to get done—like showing up at work or turning in an assignment—get an A.
- B Tasks : these are tasks that you would like to get done by the end of the day but aren’t as time sensitive. For example, studying for a test you have next week could be a B-level task. It’s still important, but it doesn’t have to be done right away.
- C Tasks: these are tasks that aren’t very important and/or have no real consequences if you don’t get them done immediately. For instance, if you’re hoping to clean out your closet but it’s not an assigned chore from your parents, you could label that to-do item with a C.
Prioritizing your to-do list helps you visualize which items need your immediate attention, and which items you can leave for later. A prioritized to-do list ensures that you’re spending your time efficiently and effectively, which helps you make room in your schedule for homework. So even though you might really want to start making decorations for Homecoming (a B task), you’ll know that finishing your reading log (an A task) is more important.
#2: Use a Planner With Time Labels
Your planner is probably packed with notes, events, and assignments already. (And if you’re not using a planner, it’s time to start!) But planners can do more for you than just remind you when an assignment is due. If you’re using a planner with time labels, it can help you visualize how you need to spend your day.
A planner with time labels breaks your day down into chunks, and you assign tasks to each chunk of time. For example, you can make a note of your class schedule with assignments, block out time to study, and make sure you know when you need to be at practice. Once you know which tasks take priority, you can add them to any empty spaces in your day.
Planning out how you spend your time not only helps you use it wisely, it can help you feel less overwhelmed, too . We’re big fans of planners that include a task list ( like this one ) or have room for notes ( like this one ).
#3: Set Reminders on Your Phone
If you need a little extra nudge to make sure you’re getting your homework done on time, it’s a good idea to set some reminders on your phone. You don’t need a fancy app, either. You can use your alarm app to have it go off at specific times throughout the day to remind you to do your homework. This works especially well if you have a set homework time scheduled. So if you’ve decided you’re doing homework at 6:00 pm, you can set an alarm to remind you to bust out your books and get to work.
If you use your phone as your planner, you may have the option to add alerts, emails, or notifications to scheduled events . Many calendar apps, including the one that comes with your phone, have built-in reminders that you can customize to meet your needs. So if you block off time to do your homework from 4:30 to 6:00 pm, you can set a reminder that will pop up on your phone when it’s time to get started.

This dog isn't judging your lack of motivation...but your teacher might. Keep reading for tips to help you motivate yourself to do your homework.
How to Do Homework When You’re Unmotivated
At first glance, it may seem like procrastination and being unmotivated are the same thing. After all, both of these issues usually result in you putting off your homework until the very last minute.
But there’s one key difference: many procrastinators are working, they’re just prioritizing work differently. They know they’re going to start their homework...they’re just going to do it later.
Conversely, people who are unmotivated to do homework just can’t find the willpower to tackle their assignments. Procrastinators know they’ll at least attempt the homework at the last minute, whereas people who are unmotivated struggle with convincing themselves to do it at a ll. For procrastinators, the stress comes from the inevitable time crunch. For unmotivated people, the stress comes from trying to convince themselves to do something they don’t want to do in the first place.
Here are some common reasons students are unmotivated in doing homework :
- Assignments are too easy, too hard, or seemingly pointless
- Students aren’t interested in (or passionate about) the subject matter
- Students are intimidated by the work and/or feels like they don’t understand the assignment
- Homework isn’t fun, and students would rather spend their time on things that they enjoy
To sum it up: people who lack motivation to do their homework are more likely to not do it at all, or to spend more time worrying about doing their homework than...well, actually doing it.
3 Tips for How to Get Motivated to Do Homework
The key to getting homework done when you’re unmotivated is to figure out what does motivate you, then apply those things to homework. It sounds tricky...but it’s pretty simple once you get the hang of it! Here are our three expert tips for motivating yourself to do your homework.
#1: Use Incremental Incentives
When you’re not motivated, it’s important to give yourself small rewards to stay focused on finishing the task at hand. The trick is to keep the incentives small and to reward yourself often. For example, maybe you’re reading a good book in your free time. For every ten minutes you spend on your homework, you get to read five pages of your book. Like we mentioned earlier, make sure you’re choosing a reward that works for you!
So why does this technique work? Using small rewards more often allows you to experience small wins for getting your work done. Every time you make it to one of your tiny reward points, you get to celebrate your success, which gives your brain a boost of dopamine . Dopamine helps you stay motivated and also creates a feeling of satisfaction when you complete your homework !
#2: Form a Homework Group
If you’re having trouble motivating yourself, it’s okay to turn to others for support. Creating a homework group can help with this. Bring together a group of your friends or classmates, and pick one time a week where you meet and work on homework together. You don’t have to be in the same class, or even taking the same subjects— the goal is to encourage one another to start (and finish!) your assignments.
Another added benefit of a homework group is that you can help one another if you’re struggling to understand the material covered in your classes. This is especially helpful if your lack of motivation comes from being intimidated by your assignments. Asking your friends for help may feel less scary than talking to your teacher...and once you get a handle on the material, your homework may become less frightening, too.
#3: Change Up Your Environment
If you find that you’re totally unmotivated, it may help if you find a new place to do your homework. For example, if you’ve been struggling to get your homework done at home, try spending an extra hour in the library after school instead. The change of scenery can limit your distractions and give you the energy you need to get your work done.
If you’re stuck doing homework at home, you can still use this tip. For instance, maybe you’ve always done your homework sitting on your bed. Try relocating somewhere else, like your kitchen table, for a few weeks. You may find that setting up a new “homework spot” in your house gives you a motivational lift and helps you get your work done.
Social media can be a huge problem when it comes to doing homework. We have advice for helping you unplug and regain focus.
How to Do Homework When You’re Easily Distracted
We live in an always-on world, and there are tons of things clamoring for our attention. From friends and family to pop culture and social media, it seems like there’s always something (or someone!) distracting us from the things we need to do.
The 24/7 world we live in has affected our ability to focus on tasks for prolonged periods of time. Research has shown that over the past decade, an average person’s attention span has gone from 12 seconds to eight seconds . And when we do lose focus, i t takes people a long time to get back on task . One study found that it can take as long as 23 minutes to get back to work once we’ve been distracte d. No wonder it can take hours to get your homework done!
3 Tips to Improve Your Focus
If you have a hard time focusing when you’re doing your homework, it’s a good idea to try and eliminate as many distractions as possible. Here are three expert tips for blocking out the noise so you can focus on getting your homework done.
#1: Create a Distraction-Free Environment
Pick a place where you’ll do your homework every day, and make it as distraction-free as possible. Try to find a location where there won’t be tons of noise, and limit your access to screens while you’re doing your homework. Put together a focus-oriented playlist (or choose one on your favorite streaming service), and put your headphones on while you work.
You may find that other people, like your friends and family, are your biggest distraction. If that’s the case, try setting up some homework boundaries. Let them know when you’ll be working on homework every day, and ask them if they’ll help you keep a quiet environment. They’ll be happy to lend a hand!
#2: Limit Your Access to Technology
We know, we know...this tip isn’t fun, but it does work. For homework that doesn’t require a computer, like handouts or worksheets, it’s best to put all your technology away . Turn off your television, put your phone and laptop in your backpack, and silence notifications on any wearable tech you may be sporting. If you listen to music while you work, that’s fine...but make sure you have a playlist set up so you’re not shuffling through songs once you get started on your homework.
If your homework requires your laptop or tablet, it can be harder to limit your access to distractions. But it’s not impossible! T here are apps you can download that will block certain websites while you’re working so that you’re not tempted to scroll through Twitter or check your Facebook feed. Silence notifications and text messages on your computer, and don’t open your email account unless you absolutely have to. And if you don’t need access to the internet to complete your assignments, turn off your WiFi. Cutting out the online chatter is a great way to make sure you’re getting your homework done.
#3: Set a Timer (the Pomodoro Technique)
Have you ever heard of the Pomodoro technique ? It’s a productivity hack that uses a timer to help you focus!
Here’s how it works: first, set a timer for 25 minutes. This is going to be your work time. During this 25 minutes, all you can do is work on whatever homework assignment you have in front of you. No email, no text messaging, no phone calls—just homework. When that timer goes off, you get to take a 5 minute break. Every time you go through one of these cycles, it’s called a “pomodoro.” For every four pomodoros you complete, you can take a longer break of 15 to 30 minutes.
The pomodoro technique works through a combination of boundary setting and rewards. First, it gives you a finite amount of time to focus, so you know that you only have to work really hard for 25 minutes. Once you’ve done that, you’re rewarded with a short break where you can do whatever you want. Additionally, tracking how many pomodoros you complete can help you see how long you’re really working on your homework. (Once you start using our focus tips, you may find it doesn’t take as long as you thought!)

Two Bonus Tips for How to Do Homework Fast
Even if you’re doing everything right, there will be times when you just need to get your homework done as fast as possible. (Why do teachers always have projects due in the same week? The world may never know.)
The problem with speeding through homework is that it’s easy to make mistakes. While turning in an assignment is always better than not submitting anything at all, you want to make sure that you’re not compromising quality for speed. Simply put, the goal is to get your homework done quickly and still make a good grade on the assignment!
Here are our two bonus tips for getting a decent grade on your homework assignments , even when you’re in a time crunch.
#1: Do the Easy Parts First
This is especially true if you’re working on a handout with multiple questions. Before you start working on the assignment, read through all the questions and problems. As you do, make a mark beside the questions you think are “easy” to answer .
Once you’ve finished going through the whole assignment, you can answer these questions first. Getting the easy questions out of the way as quickly as possible lets you spend more time on the trickier portions of your homework, which will maximize your assignment grade.
(Quick note: this is also a good strategy to use on timed assignments and tests, like the SAT and the ACT !)
#2: Pay Attention in Class
Homework gets a lot easier when you’re actively learning the material. Teachers aren’t giving you homework because they’re mean or trying to ruin your weekend... it’s because they want you to really understand the course material. Homework is designed to reinforce what you’re already learning in class so you’ll be ready to tackle harder concepts later.
When you pay attention in class, ask questions, and take good notes, you’re absorbing the information you’ll need to succeed on your homework assignments. (You’re stuck in class anyway, so you might as well make the most of it!) Not only will paying attention in class make your homework less confusing, it will also help it go much faster, too.

What’s Next?
If you’re looking to improve your productivity beyond homework, a good place to begin is with time management. After all, we only have so much time in a day...so it’s important to get the most out of it! To get you started, check out this list of the 12 best time management techniques that you can start using today.
You may have read this article because homework struggles have been affecting your GPA. Now that you’re on the path to homework success, it’s time to start being proactive about raising your grades. This article teaches you everything you need to know about raising your GPA so you can
Now you know how to get motivated to do homework...but what about your study habits? Studying is just as critical to getting good grades, and ultimately getting into a good college . We can teach you how to study bette r in high school. (We’ve also got tons of resources to help you study for your ACT and SAT exams , too!)
These recommendations are based solely on our knowledge and experience. If you purchase an item through one of our links, PrepScholar may receive a commission.

Ashley Sufflé Robinson has a Ph.D. in 19th Century English Literature. As a content writer for PrepScholar, Ashley is passionate about giving college-bound students the in-depth information they need to get into the school of their dreams.
Student and Parent Forum
Our new student and parent forum, at ExpertHub.PrepScholar.com , allow you to interact with your peers and the PrepScholar staff. See how other students and parents are navigating high school, college, and the college admissions process. Ask questions; get answers.

Ask a Question Below
Have any questions about this article or other topics? Ask below and we'll reply!
Improve With Our Famous Guides
- For All Students
The 5 Strategies You Must Be Using to Improve 160+ SAT Points
How to Get a Perfect 1600, by a Perfect Scorer
Series: How to Get 800 on Each SAT Section:
Score 800 on SAT Math
Score 800 on SAT Reading
Score 800 on SAT Writing
Series: How to Get to 600 on Each SAT Section:
Score 600 on SAT Math
Score 600 on SAT Reading
Score 600 on SAT Writing
Free Complete Official SAT Practice Tests
What SAT Target Score Should You Be Aiming For?
15 Strategies to Improve Your SAT Essay
The 5 Strategies You Must Be Using to Improve 4+ ACT Points
How to Get a Perfect 36 ACT, by a Perfect Scorer
Series: How to Get 36 on Each ACT Section:
36 on ACT English
36 on ACT Math
36 on ACT Reading
36 on ACT Science

Series: How to Get to 24 on Each ACT Section:
24 on ACT English
24 on ACT Math
24 on ACT Reading
24 on ACT Science
What ACT target score should you be aiming for?
ACT Vocabulary You Must Know
ACT Writing: 15 Tips to Raise Your Essay Score
How to Get Into Harvard and the Ivy League
How to Get a Perfect 4.0 GPA
How to Write an Amazing College Essay
What Exactly Are Colleges Looking For?
Is the ACT easier than the SAT? A Comprehensive Guide
Should you retake your SAT or ACT?
When should you take the SAT or ACT?
Stay Informed
Get the latest articles and test prep tips!
Looking for Graduate School Test Prep?
Check out our top-rated graduate blogs here:
GRE Online Prep Blog
GMAT Online Prep Blog
TOEFL Online Prep Blog
Holly R. "I am absolutely overjoyed and cannot thank you enough for helping me!”
weekly math homework grade 5
All Formats
Resource types, all resource types.
- Rating Count
- Price (Ascending)
- Price (Descending)
- Most Recent
Weekly math homework grade 5

Grade 5 Weekly Math Homework

5th Grade Weekly Math Homework Year-Long Set

Grade 5 Weekly Math Homework Multiplication and Division

Grade 5 Weekly Math Homework Number Sense

Grade 5 Weekly Math Homework Geometry

2nd Grade Math Weekly Homework Week 5
Grade 5 Weekly Math Homework Grids
EUREKA MATH 2nd Grade Module 5 Homework & Assessments CC
4th Grade Math Packet Weekly Spiraled Review Worksheets Homework Morning Work

3rd Grade Math Packet Weekly Spiraled Review Worksheets Homework Morning Work
Weekly Math Homework Multiplication & Division 3rd Grade Common Core

5th - 8th Grade Math Curriculum Bundle | No Prep Notes & Practice

5th Grade Weekly Math Homework *BUNDLE* 24 Weeks ALL Math Standards
3rd Grade Common Core Weekly Math Homework

5th Grade Math Homework | 5th Grade Math Review HW| Weekly Skill Check| NGLS

6th Grade Math Weekly Homework - YEAR ROUND

- Google Slides™
Set 1, English & Math Rules; Weekly Homework Sheets & PowerPoint Lessons.

6th Grade Math Weekly Warmups and Homework Sample

5th Grade : Math Vocabulary Crossword Puzzle Worksheet 5 .NBT.7

5th Grade : Math Vocabulary Crossword Puzzle Worksheet 5 .NBT.6
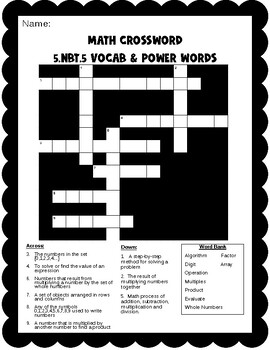
5th Grade : Math Vocabulary Crossword Puzzle Worksheet 5 .NBT. 5
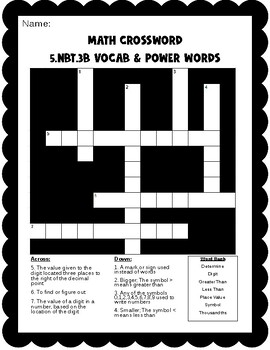
5th Grade : Math Vocabulary Crossword Puzzle Worksheet 5 .NBT.3b
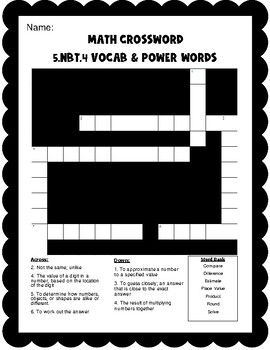
5th Grade : Math Vocabulary Crossword Puzzle Worksheet 5 .NBT.4
5th Grade Weekly Math Homework Place Value Decimals Multiplication and Division
- We're hiring
- Help & FAQ
- Privacy policy
- Student privacy
- Terms of service
- Tell us what you think
- Study Guides
- Homework Questions
Week 5 Coding Scenarios Homework Assignment 3.31.24
- Health Science
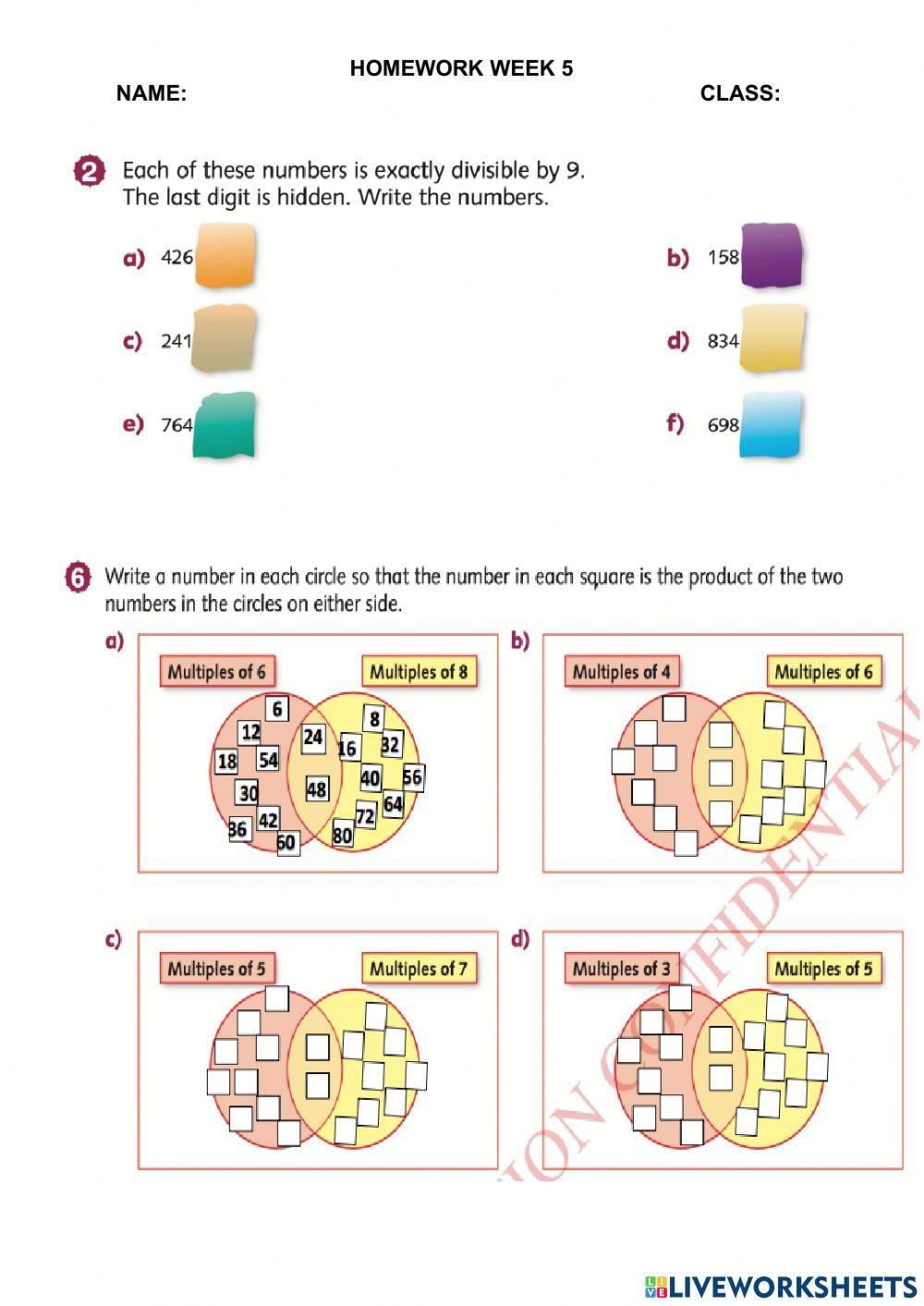
Homework week 5
Loading ad...
You can do the exercises online or download the worksheet as pdf
- Google Classroom
- Microsoft Teams
- Download PDF
Well-planned online essay writing assistance by PenMyPaper
Writing my essays has long been a part and parcel of our lives but as we grow older, we enter the stage of drawing critical analysis of the subjects in the writings. This requires a lot of hard work, which includes extensive research to be done before you start drafting. But most of the students, nowadays, are already overburdened with academics and some of them also work part-time jobs. In such a scenario, it becomes impossible to write all the drafts on your own. The writing service by the experts of PenMyPaper can be your rescuer amidst such a situation. We will write my essay for me with ease. You need not face the trouble to write alone, rather leave it to the experts and they will do all that is required to write your essays. You will just have to sit back and relax. We are offering you unmatched service for drafting various kinds for my essays, everything on an online basis to write with. You will not even have to visit anywhere to order. Just a click and you can get the best writing service from us.
- Password reminder
- Registration
Finished Papers

IMAGES
VIDEO
COMMENTS
3. 5.26/5 points Previous Answers BBBasicStat8Acc 7.1. My Notes Ask Your Teacher 4. 5.26/5 points Previous Answers BBBasicStat8Acc 7.1. My Notes Ask Your Teacher 5. 5.26/5 points Previous Answers BBBasicStat8Acc 7.2. My Notes Ask Your Teacher Raul received a score of 73 on a history test for which the class mean was 70 with a standard deviation ...
Would a B+ person's blood sample clump during an agglutination test with anti-Rh antibodies? active agents. What type of vaccine needs to be refrigerated? E-test. What test would help find the minimal inhibitory concentration for an antibacterial? 100% Learn with flashcards, games, and more — for free.
Homework Week 5 (ADA) 5/5/19, 11'37 PM Oba Lewis MATH120 Spring April 2019, section B007, Spring 2019 Homework Week 5 (ADA) (Homework) Instructor: Martha Stillman Current Score : 96.36 / 100 Due : Sunday, May 26, 2019 11:59 PM EDTLast Saved : n/a Saving. Solutions available. MATH 120.
This Grammar Homework Week Five will be a perfect addition to your English resource collection. This great homework activity will build on lessons in school and help improve grammar skills. Recently Viewed and Downloaded ›
You finish one episode, then decide to watch another even though you've got SAT studying to do. It's just more fun to watch people make scones. D. Start the episode, but only catch bits and pieces of it because you're reading Twitter, cleaning out your backpack, and eating a snack at the same time. 5.
View Homework Week 5 (ADA).pdf from MATH 120 at American Military University. Homework Week 5 (ADA) 5/5/19, 11'37 PM Oba Lewis MATH120 Spring April 2019, section B007, Spring 2019 Homework Week 5
1 2 5, 5 5 2 Find the Sum. 7 3, 9 8 3 + 8, 3 9 9 8 2, 3 8 2 Find the Sum. 9 9, 7 8 2 + 5, 1 8 7 1 0 4, 9 6 9 The school store sold 83,299 pencils the first week of school and 92,185 pencils the second week of school. How many pencils did they sell all together? 175,484 pencils Phillip has $24.25 and Cheryl has $2.33.
• Homework Week 5 Exercise • With your tongue find the dome in your hard palate (roof of the mouth). • Sing the 'ooooo' vowel • Will naturally place in the mask. • Feel it vibrate in the dome, nose and eye area. • Morph to an 'eeeee' vowel and try to feel the same sensations.
Question: = Week 5 - ALEKS Homework Question 1 of 10 (1 point) = 2 = 3 F4 = 5 = 6 The one-to-one functions g and h are defined as follows. g={(-8, 2), (1, -8), (5, - 4), (8, 4)} h(x)=(x-13 Find the following. g X (n.)(2) = 0 Example . Show transcribed image text. Here's the best way to solve it.
View Homework week 5.docx from CHDV 133 at California State University, Sacramento. Homework week 5 Homework - Week 5 1. State two criteria that make variables suitable for scientific investigation,
Management document from University of Maryland, Baltimore County, 2 pages, Homework Assignment #5 You will have five questions to answer each week based on the week's topics and readings. You will be expected to write a thorough and well-reasoned response to each question. Support your response by citing the textbook or internet.
As is the case with our grade-specific printables for younger kids, our fifth grade worksheets are designed to simultaneously teach, engage, and entertain. That means students will find compelling biographical texts about important historical figures, fun crossword puzzles to assist with fifth grade vocabulary, Sudoku-style puzzles to enhance ...
Week 7 LES 305. 25 terms. DaniH113. Preview. polisci exam 2 - the presidency. 20 terms. newtonastrid4. Preview. sst unit 2 study notes. 46 terms. luminous443. Preview. Terms in this set (20) Bill of Rights. The first ten amendments of the U.S. Constitution. Checks and Balances.
A 2014 study found kindergarteners to fifth graders averaged 2.9 hours of homework per week, sixth to eighth graders 3.2 hours per teacher, and ninth to twelfth graders 3.5 hours per teacher. A 2014-2019 study found that teens spent about an hour a day on homework. Beginning in 2020, the COVID-19 pandemic complicated the very idea of homework ...
Grade 5 Weekly Math Homework Multiplication and Division. This is weeks 21-23 of the grade 5 weekly math homework, multiplication and division, that is organized as a nightly routine, with questions relating to the work taught in class. Students can choose to do the whole week at once, or each day individually.
Homework week 5 Homework week 5. Loading ad... math4_tnd Member for 2 years 5 months Age: 9-15. Level: 4. Language: English (en) ID: 1470373. 01/10/2021. Country code: VN. Country: Vietnam. School subject: math (1066928) ...
Health-science document from Bryant & Stratton College, 5 pages, Week 5 Coding Scenarios Homework Assignment Question Puncture aspiration of skin cyst of the forearm Question Debridement of infected skin on 30% of the body surface [A] [B] [C] Question Excision of 0.2 cm lesion of the lip Question Excision of ingrown na
Homework week 5 Homework week 5. Loading ad... math5_tnd Member for 2 years 5 months Age: 9-15. Level: 5. Language: English (en) ID: 1481272. 04/10/2021. Country code: VN. Country: Vietnam. School subject: math (1066928) ...
160 Week 5 Pre-Class Student Worksheets NOTE TO Students: For this week please review the Cooper and Giddens chapters on Fluids and Electrolytes for this lesson. NOTE TO Students: You will complete all the tables on these pre-class worksheets prior to cla ... 160 Week 9 Homework.docx. 160 Week 9 Pre-Class Student Worksheets Concept: Palliation ...
Homework Week 5 - 26 Customer reviews. 4.7/5. Featured Samples. E-mail: Homework Week 5: Can you write essays for free? Sometimes our managers receive ambiguous questions from the site. At first, we did not know how to correctly respond to such requests, but we are progressing every day, so we have improved our support service. ...